Is your computer running slower than normal? Perhaps its battery is draining? You might want to check if it’s being used to mine cryptocurrency.
Another Chrome extension was caught cryptojacking, or hijacking users’ computers without consent and using their processing resources to mine cryptocurrency. The extension Archive Poster has been stealthily taking advantage of its 105,000 users for the past few weeks, Bleeping Computer reports.
Marketed as an easier way to “reblog, queue, draft, and like posts right from another blog’s archive” on Tumblr, the extension was using the well-known Coinhive miner without telling users. The Coinhive script has been deployed on numerous sites, including CBS’s Showtime and Pirate Bay as a way to inconspicuously mine cryptocurrency, or digital money. In the case of Archive Poster, it was used to harvest Monero, the same currency mined by “Digmine,” a malware that recently spread through Facebook Messenger.
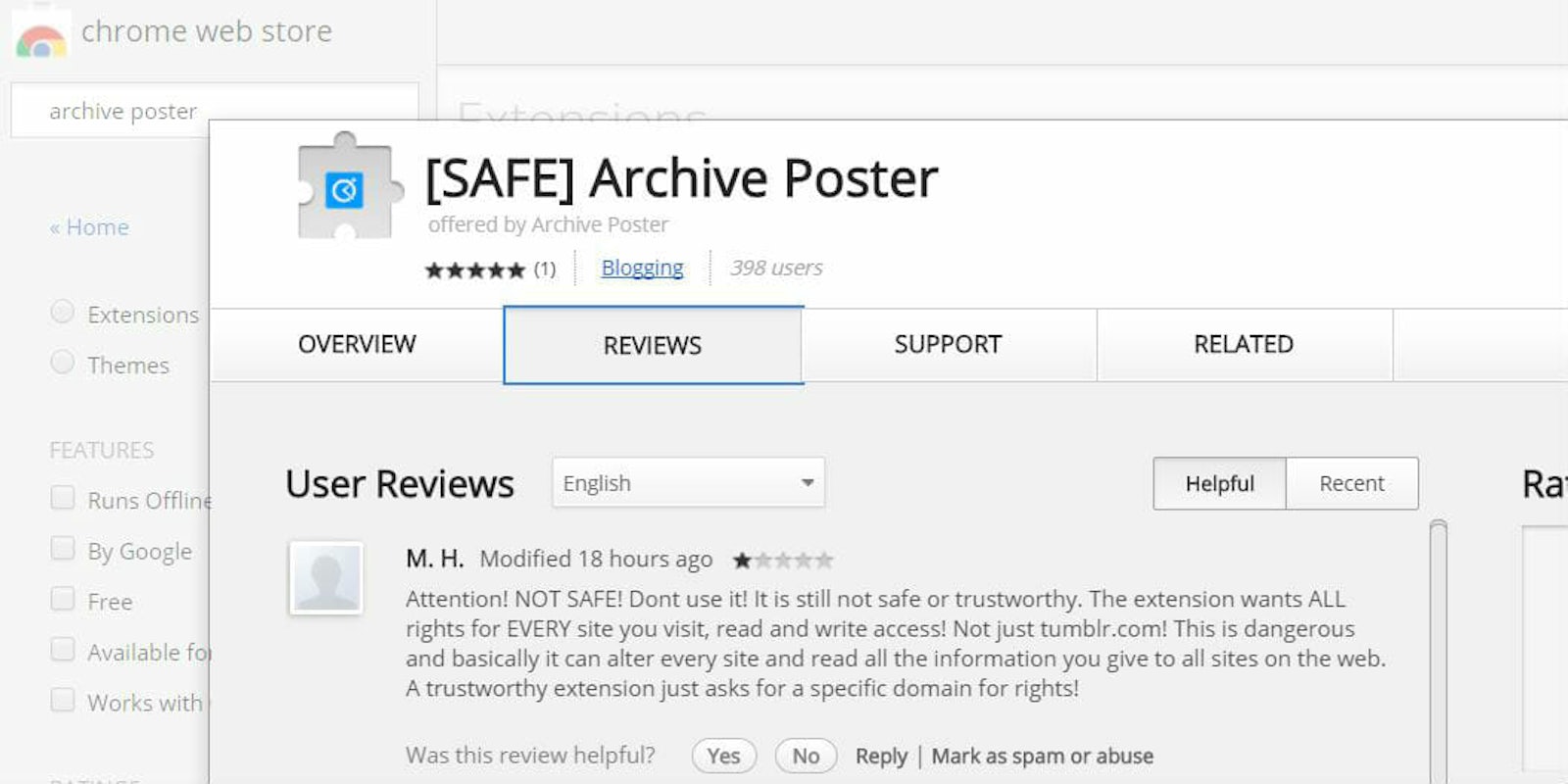
The code was hidden in at least four versions of the Archive Poster plugin from 4.4.3.994 to 4.4.3.998. Furious users flooded the extension’s product page with one-star reviews after the intrusive code was discovered. Some even reported the extension to the Google Chrome Help Forum, but the search giant told them to “get in touch with the extension developer for further assistance.”
As the value of cryptocurrency continues to boom, websites and services are finding inventive ways to mine more digital coin, often at the expense of customers. In November, a researcher documented more than 2,500 sites that actively run cryptocurrency mining code in popular browsers. While technically not illegal—they don’t steal your information like malware—cryptominers can have a negative impact on the performance of your computer and present a serious ethical dilemma.
A few ways to protect yourself from cryptocurrency mining code include downloading antivirus protection software and keeping it up to date. For suggestions, you can check out our list of the top security software for Mac and Windows. Other methods for protecting your devices include installing an ad-blocker (AdBlock Plus and AdGuard both block Coinhive’s JS library) or installing a cryptomining blocker extension onto your browser.
Google has removed Archive Poster from its store, but it appears a new version with the same description is already live. It’s not clear if this version includes the same mining code or if it was reapproved by Google. Whatever the case, we strongly recommend you avoid downloading it to be safe.
We have reached out to Google and will update this article if we find out more.