The intelligence firm at the center of a notorious cybersecurity breach that affected top government officials failed to institute standard security measures prior to the attack, according to a newly leaked report.
In December 2011, a group of skilled hackers broke into the network of Strategic Forecasting, Inc. (Stratfor), compromising the personal data of some 860,000 customers, including a former U.S. vice president, CIA director, and secretary of state, among others.
The hackers, known collectively as AntiSec, exfiltrated approximately 60,000 credit card numbers and associated data, resulting in a reported $700,000 in fraudulent charges. Roughly 5 million internal emails were obtained by the hackers and later released by the whistleblower organization WikiLeaks as the "Global Intelligence Files."
For Stratfor, a Texas-based geopolitical intelligence and consulting firm, the incident was an international embarrassment that caused roughly $3.78 million in total damages—and all of it could’ve been avoided by meeting common fraud prevention requirements.
Based on confidential internal documents obtained by the Daily Dot and Motherboard, Stratfor employed substandard cybersecurity prior to the infiltration that left thousands of customers vulnerable to potential identity theft. The documents also lend credibility to statements made by Hyrriiya, a relatively unknown hacker who claimed responsibility for the breach.
The Daily Dot–Motherboard investigation is based on a cache of sealed court documents—roughly 3 gigabytes of previously unseen chat logs, warrants, and various government reports—some of which was collected by Hector “Sabu” Monsegur, a hacker-turned-informant. Evidence provided by Monsegur was used to convict eight members of Anonymous, including Jeremy Hammond, who is currently serving the remainder of a 10-year sentence for his role in the attack.
READ MORE:
How an FBI informant orchestrated the Stratfor hack
According to the documents, Stratfor engaged Verizon Business/Cybertrust to “conduct a forensic investigation” into the breach on Dec. 30, 2011, and requested that findings be shared with the Federal Bureau of Investigation. Verizon's security team inspected the computers at Stratfor's office shortly after the attack, as well as servers later confiscated by federal agents from CoreNAP, an Austin-based data center that hosted Stratfor's customer information.
In a 66-page report filed Feb. 15, 2012, Verizon concludes in painful detail that Stratfor had insufficient control over remote access to vital systems, and that those systems were not protected by a firewall and lacked proper file integrity-monitoring. (Editors’ note: The full report can be viewed below. Only Internet protocol addresses and private customer information have been redacted.)
"In light of a confirmed system breach,” Verizon reports, “it should be noted that several distinct vulnerabilities and network configurations existed that allowed this breach and subsequent data compromise to occur.”
For starters, at the time of the attack, no password management policy existed within Stratfor. Passwords were at times shared between employees, and nothing prevented the same passwords from being used on multiple devices. “Users commonly use the same password to access email as the password to remotely access a system containing sensitive information,” the report states.
According to Verizon, no anti-virus software had been deployed on any of the examined systems, which left Stratfor “wide open to not only the more sophisticated and customized hacker attempts, but also to other viruses.” While a firewall was in place for the office portion of the Stratfor network at the time of the breach, it was not properly configured to retain any useful information.
Moreover, Stratfor would have been immediately notified of attempts to exfiltrate its customer data and internal emails had it implemented a proper file-monitoring solution. Such a security precaution could have prevented Stratfor's customer data from being stolen by AntiSec in the first place.
Another "significant factor" in the breach was the design of Stratfor's e-commerce environment, which facilitated the electronic transfer of payments by its customers. According to the report, this system was accessible, needlessly, from anywhere within the company's network, "as well as the Internet directly."
Verizon also discovered traces of exfiltrated cardholder information from the e-commerce environment within Stratfor's mail server. That indicates that there were latent flaws in the architecture of the company’s network.
“This finding highlights the inherent problems around the lack of network segregation between the corporate Stratfor environment and the payment and e-commerce environment," the report claims.
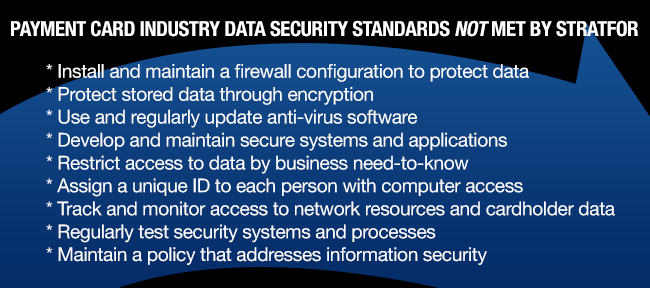
Verizon concluded that Stratfor's customer payment system, at the time of the attack, met only three out of the 12 fraud prevention requirements maintained by the report, which were taken from Visa’s fraud control and investigations procedures. Eight of those requirements, which were not met, directly contributed to the breach.
“Typically you’ll find a company deficient in one or two key areas,” noted Kevin Cunningham, the president and founder of SailPoint, a leading independent identity and access management provider. “This is an extreme case and a breakdown of a magnitude I’ve never seen before.
“Security is an interesting dynamic between risk and flexibility,” he continued. “You have to define your policy and ensure that controls are in place. In this case, it doesn’t look like they had any policies defined. It’d be like not only leaving your front door unlocked and your windows open, but also your family jewels on the kitchen table.
“It was an accident waiting to happen.”
FROM MOTHERBOARD:
How an FBI informant helped Anonymous hack Brazil
Along with the names, credit card numbers, and affiliated data for Stratfor's customers, AntiSec hackers obtained card verification values, the three-digit number located on the back of payment cards. It’s against payment card industry data security standards (PCI DSS) for merchants to retain those codes, according to the PCI Security Standards Council. (The report speculates that since Stratfor outsourced its payment processing functions, the organization may not have been directly required to adhere to these payment industry standards.)
PCI DSS also require credit card numbers to be encrypted when digitally stored by merchants. Stratfor’s founder and CEO previously admitted to storing unencrypted data in an official statement. It was this cardholder information that was stolen by AntiSec in December 2011.
Stratfor ultimately settled a class-action lawsuit with its customers over the losses in June 2012 for a reported $1.75 million.
Interestingly, Verizon also found evidence of another breach that accessed cardholder information: “Analysis of the Zimbra mail server provided Verizon Business with evidence that the intruder(s) created the database dump file (which was later exfiltrated from the STRATFOR environment) on November 16, 2011.”
That discovery appears to further validate the claims of Hyrriiya, an Anonymous hacker known for his cyberattacks on Syrian government websites. In a May 2012 letter sent to Hammond’s attorneys, Hyrriiya confessed to hacking Stratfor and providing AntiSec with access.
“This initial hack of Stratfor occurred approximately TWO week BEFORE anyone involved in #antisec (including Sabu and Hammond) had ANY knowledge or involvement in Stratfor,” Hyrriiya wrote. “After reviewing the data I was able to access in Stratfor, I realised that the customer details included all pertinent credit card information for both individuals and a multitude of corporate entities, military institutions and espionage agencies. Upon this realisation, I promptly decided that I wanted this information to be public.”
A previous Daily Dot investigation found that—contrary to the FBI’s official statements—the Stratfor breach was orchestrated by informant Hector Monsegur. Chat logs show Monsegur obtained critical information about Stratfor’s vulnerabilities privately from Hyrriiya, and then arranged for Hammond to meet with Hyrriiya and gain access to Stratfor.
Monsegur was released in late May on time served. Barrett Brown, a journalist who pleaded guilty in April to being an accessory after the fact in the Stratfor hack, is scheduled to be sentenced in August.
Verizon Wireless did not respond to multiple inquiries. Stratfor declined to comment on this article.
Verizon Wireless's forensics report on the 2011 Stratfor hack (click for full size)
Additional reporting by Austin Powell | Illustration by Jason Reed