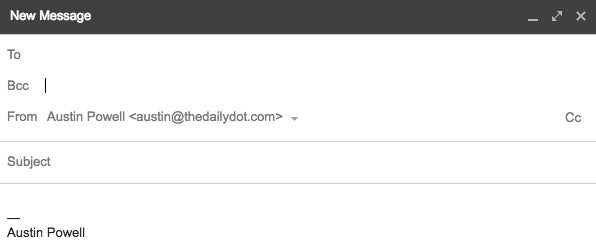
The act of emailing groups of people often presents quandaries, both of the etiquette and ethical variety. If you cc everyone, you run the risk of a never-ending reply-all chain that exposes the contact information of all parties. If you bcc everyone, no one knows who’s included in the email thread, leading to a formal and impersonal tone. Don’t bcc and someone will inevitably respond, “OMG use bcc!” If you bcc for a party invite, and you may get inquiries as to, “Who’s all invited?” More sinister: cc’ing individuals can feel like ganging up on the sender, where cc’ing can feel like the three-way call in Mean Girls with spectators hidden from view.
How does bcc even work? Are there ways that senders can actually see? What does bcc even stand for? I’ll tell you in a second, let me just make this more private and “move you to bcc.”
What does bcc stand for?
Though some believe it stands for “blind courtesy copy,” bcc is an antiquated abbreviation for “blind carbon copy.” In the early days of copy machines, one might create documents that had carbon paper behind each original sheet, making a carbon copy. Done on either a typewriter or by hand, the original would have information on the bottom of each page detailing who was getting a carbon copy (or cc) of the paper. This can still be seen in some receipt paper today. For example, the first page will say “original” and the second will say “customer copy.”
Blind carbon copies were an essential trick for typists to hide information about who was getting a copy of the carbon copy. The persons receiving the original and the cc would understand that they were both getting copies, but the bcc would be hidden from both parties. According to a 1979 secretarial handbook, in order to make a bcc, sheets of carbon paper were added to the cc paper so that the others wouldn’t see this new addressee. Secretaries were then supposed to make a note of these bcc recipients and keep them on file while still keeping their identities “blind” to the original parties.
With the dawn of the internet, the bcc name stuck as a way for newly formed businesses and newsletters to alert large groups of subscribers. The New York Times even wrote in 2001 that using bcc could we an effective way to prevent computer viruses. We know now that it’s absolutely not true (quite the opposite, in fact), but it’s nice to think about how quaint we once were.
How does bcc work?
Essentially every email system in use today uses a standardization protocol called “RFC 5322 – Internet Message Format.” This extremely boring document is kind of like the Magna Carta of the internet. It lays down the law about things like email addresses utilizing the @ symbol, syntax, and the fields that will be used when composing an email. Subject line, cc, and bcc are among these.
RFC 5322 provides code that defines what cc and bcc do. When one sends an email with a recipient and some addresses listed in the cc field, the email system is instructed to copy the message to the recipient as well as those copied on the message. The email system must also allow the recipient and all those cc’ed to see who is receiving the copy.
RFC 5322 thus defines bcc as a copy in which the email system is instructed to hide the bcc list from the recipients, those who are cc’ed and others who may be bcc’d. Privacy of the BCC’ers is protected in this way.
READ MORE:
- How to get faster Wi-Fi
- How to leave a group text message once and for all
- The best texting games to play when you’re bored
Is there any way others can find out who is bcc’d?
Thankfully, no. Unless your mail user agent (such as Gmail, Yahoo, etc) has made an error, there’s no way a recipient can see who you have bcc’d. Receiving servers just receive the email and cannot access information that is made blind by the sender’s mail user agent. However, if your company uses an exchange server (like Outlook), it’s possible that work emails can be viewed by an “administrator” like a boss or someone in the IT department.
Now that you know the basics of bcc, you can keep being passive aggressive or extremely conscientious while sending electronic communications.


