A potentially crippling botnet spread rapidly over the weekend, infecting thousands of Android devices with a malware that mines cryptocurrency, researchers at Netlab 360 discovered.
Dubbed “ADB.miner,” the malicious code attacks internet port 5555, a command-line tool used for debugging, installing apps, and other purposes. While the rarely used port is normally closed, a developer tool called Android Debug Bridge can open it to run diagnostics tests. For those who aren’t familiar, a botnet is a network of devices compromised by a malware the enables cybercriminals to remotely command them without the owners’ knowledge.
Once infected, devices are raided by an app that forces them to mine the cryptocurrency Monero, the digital coin of choice for hackers. We’ve seen similar attacks in recent months. Using javascript miner Coin Hive, hackers turned fact-checking publication Politifact into a Monero-harvesting goldmine. Another Monero-based attack used a fake video link to spread through Facebook Messenger.
What’s most concerning about ADB.miner is that it contains sections of code derived from the Mirai botnet, one of the most feared malware in existence. The Mirai botnet, which we now know was made to gain an advantage in the platforming game Minecraft, took down popular online services, including Twitter, Netflix, Spotify, and Reddit in 2016 after it successfully ambushed Dyn, a company that provides domain name services to major websites. Netlab 360 says this is the first it’s seen Mirai code used on an Android bot.
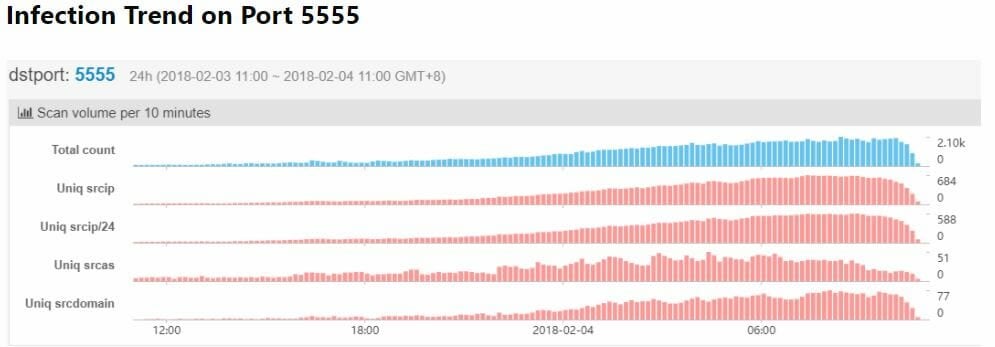
So far, between 2,750 and 5,000 devices—mostly Android smartphones and televisions—were infected in China and South Korea. Netlab 360 said the malware has “worm-like” qualities that allow it to proliferate without human interaction.
“Overall, we think there is a new and active worm targeting Android systems’ ADB debug interface spreading, and this worm has probably infected more than 5,000 devices in just 24 hours,” Netlab wrote in its report. “Those infected devices are actively trying to spread malicious code.”
The researchers are not disclosing information about infected devices, presumably to avoid giving copycat hackers what they need to further exploit the vulnerability. It’s also not clear what impact the malware has on devices aside from launching a cryptominer. In past cases, Monero-mining software has taken advantage of its host’s CPUs, causing them to slow or even shut down.
It’s not easy to offer advice on how to protect yourself from the malware since Netlab hasn’t said how it finds its way onto systems. However, developers should make sure the 5555 port on their devices is closed. Also, it’s always best practice to regularly change your passwords and download reliable anti-virus software.
We have reached out to Google and will update this article if we hear back.


