As encryption becomes increasingly popular, decryption keys are growing into highly valuable targets for hackers who want to break into even the most heavily protected data.
Now, according to new research from Tel Aviv University, there’s an even easier way for hackers to swipe the keys to your digital castle.
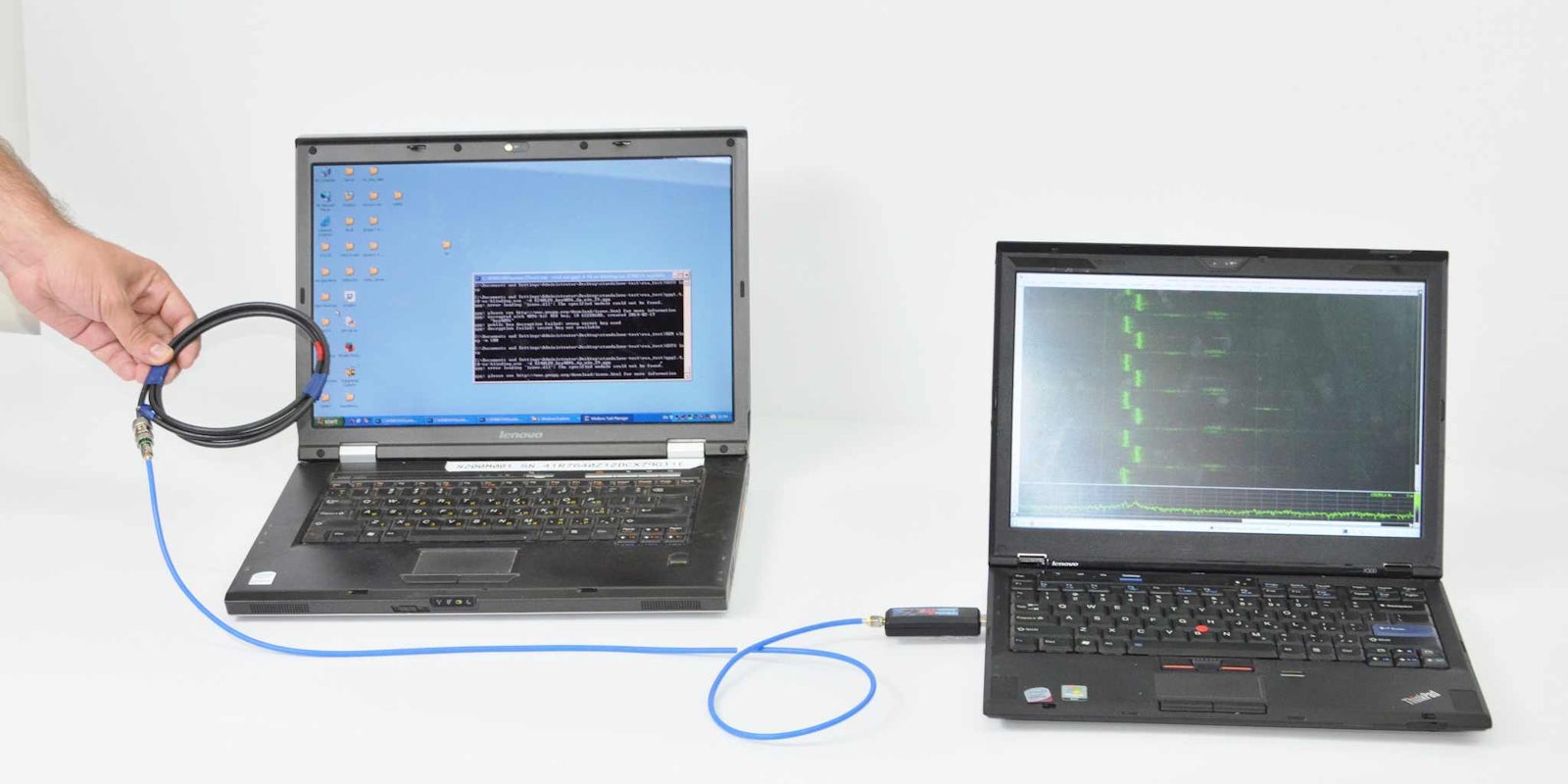
Attackers can steal decryption keys from laptop computers using a small radio almost two feet away that “can be easily concealed, e.g., inside pita bread,” the researchers write. The radio—either a receiver or USB dongle that anyone can buy—measures electromagnetic emanations to extract keys from some of the most popular encryption software around “within a few seconds.”
The hack takes advantage of the fact that every operation performed by a computer—from decrypting text to downloading a video—has different power requirements that put distinct electrical loads on the laptop’s voltage regulator, which reacts by producing electromagnetic radiation that can be measured from nearby.
“This radiation contains information regarding the CPU operations used in the decryption, which we use in our attack,” the researchers wrote.
The attack begins when the hacker sends encrypted messages to the target.
“When these are decrypted by the target computer, they trigger the occurrence of specially-structured values inside the decryption software,” the researchers explained. “These special values cause observable fluctuations in the electromagnetic field surrounding the laptop, in a way that depends on the pattern of key bits (specifically, the key-bits window in the exponentiation routine). The secret key can be deduced from these fluctuations, through signal processing and cryptanalysis.”
The researchers are Daniel Genkin, Lev Pachmanov, Itamar Pipman, and Eran Tromer. All four are at Tel Aviv University.
The four hackers build the PITA (Portal Instrument Trace Acquisition) from off-the-shelf items. PITA measures the signal produced by decryption. The photo below shows that anyone can make the device—the researchers boast of its “low price and compact size”—that can then either transmit the keys over the Internet or save them to be picked up physically whenever possible.
https://twitter.com/scanlime/status/619282579645054976
The newest version of GnuPG, a free version of the popular PGP encryption technology, attempts to resist this attack by ensuring that the key and radiation output are less easily linked, resulting in slower performance but theoretically a safer key.
Photo via Tel Aviv University