The biggest scoop in recent journalistic history almost didn’t happen because email encryption is really, really complicated.
In No Place To Hide, journalist Glenn Greenwald’s book about reporting on the trove of classified government documents leaked by former NSA contractor Edward Snowden, Greenwald recounted his first point of contact with the man who would be the singular source for the biggest story of his career. Snowden, using the pseudonym Cincinnatus, emailed Greenwald with an offer to give him a ?huge story” if Greenwald started using an encryption mechanism called Pretty Good Privacy (PGP).
“The program is complicated, especially for someone who had very little skill in programming and computers, like me,” writes Greenwald. ?So it was one of those things I had never gotten around to doing.”
Ultimately, Snowden recruited Greenwald through filmmaker Laura Poitras, who already used PGP—a system that often involves installing three different programs, wrestling with non-intuitive user interfaces, and a lot of frowning at your computer. Were Snowden less insistent in his belief that Greenwald was the only journalist who could do the NSA story justice, Greenwald would have missed out on the leaks and the story could have turned out much differently.
Had ProtonMail, an encrypted email system that launched its public beta test last Friday, been around at the time, Greenwald wouldn’t have had any difficulty encrypting his email—the process would have been as easy as signing up for a Gmail account.
ProtonMail was founded by a team of five researchers who met while working at the European Organization for Nuclear Research (CERN)—the same place that employed Tim Berners-Lee a quarter-century ago, when he first proposed the idea for the World Wide Web. After the Snowden revelations surfaced last year, the team started chatting on Facebook about privacy. They vowed to create a encrypted email system simple enough for anyone to use.
?I think we have struck the right combination of security and ease of use,” co-founder Andy Yen told the Daily Dot. ?The most secure system in the world is not useful if it is so complex nobody can use it. With ProtonMail, I think we have the ability to make encrypted communications mainstream instead of a niche market.”
On ProtonMail, everything is encrypted end-to-end, but implemented in a way that’s only slightly more onerous than using a standard webmail service. To access a ProtonMail account, a user enters two passwords—one to log onto the system and another to descramble all of the information in their inbox.
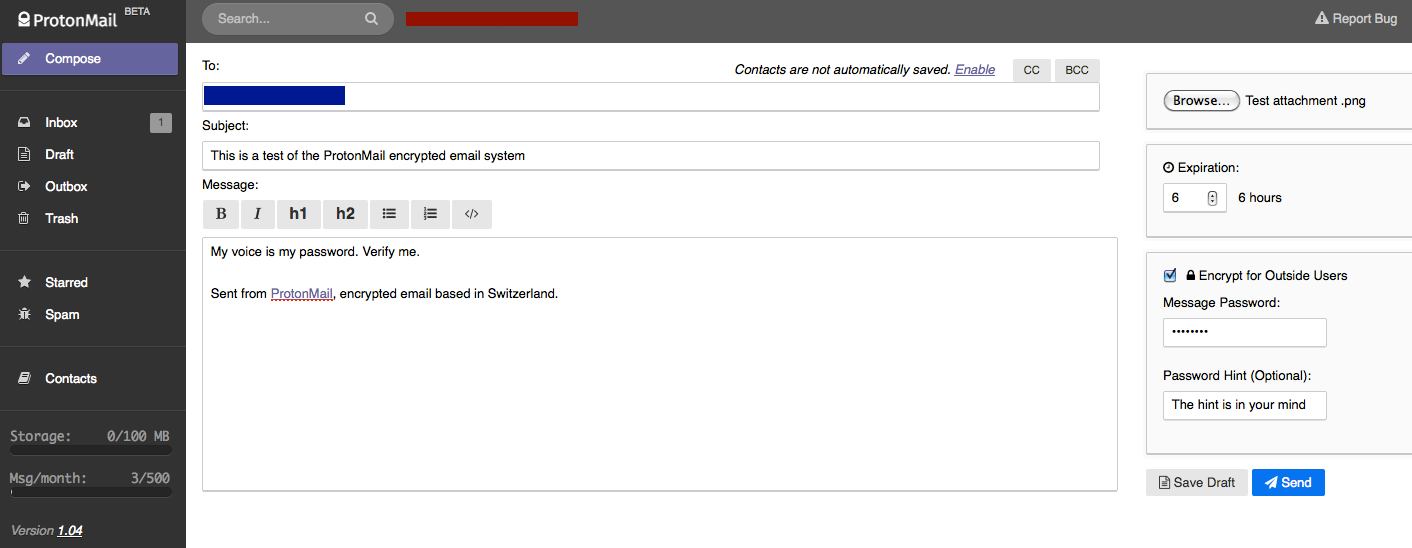
Emails to other ProtonMail users are automatically encrypted and don’t require any more thought than clicking “send.” To send an encrypted email to a non-ProtonMail address, however, a user must first compose the email, check the box labeled ?Encrypt for Outside Users” and then enter a password and an optional password hint.
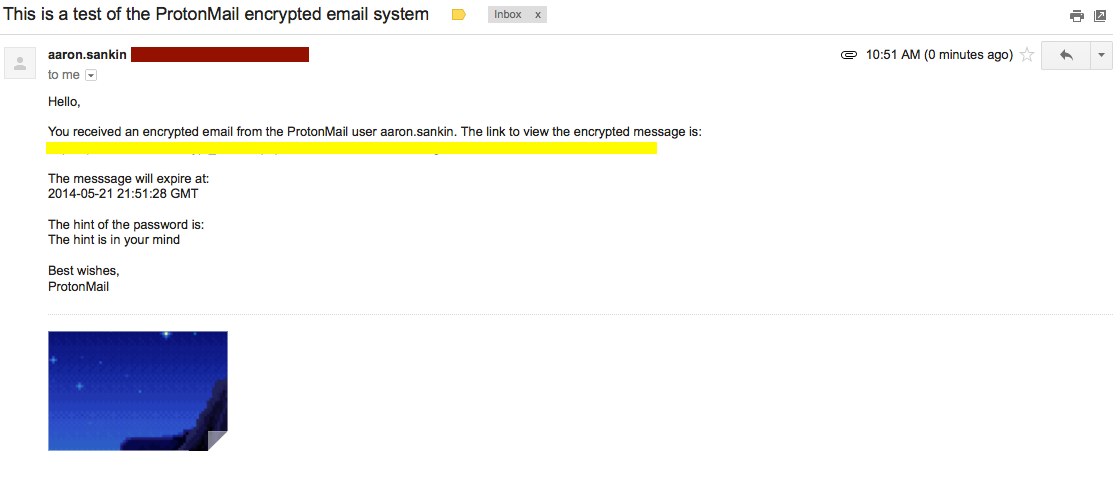
The recipient then gets an email informing them they have an encrypted message from a ProtonMail user and is given a link to where they can retrieve that message.
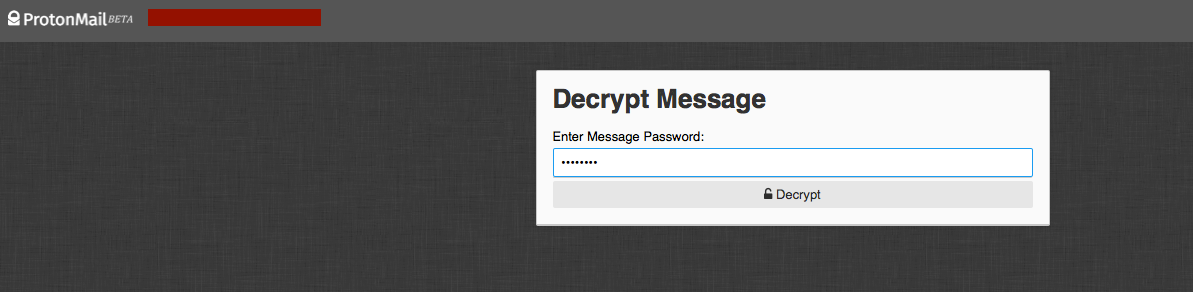
After clicking on the link, the recipient is instructed to enter a password.
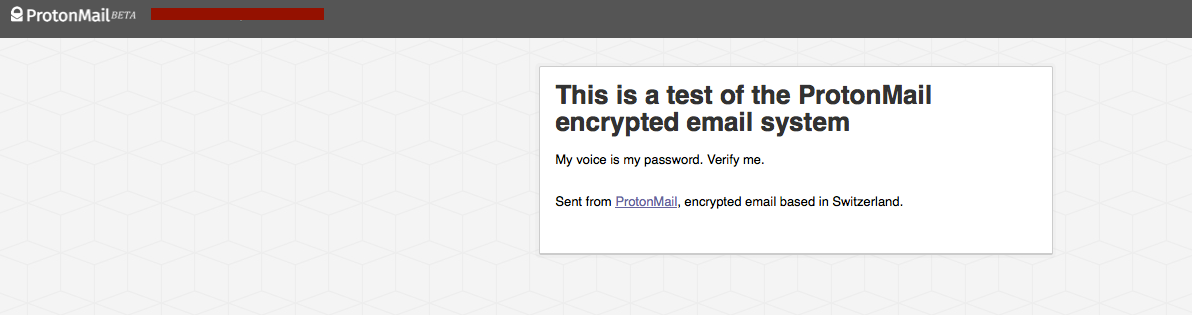
And then they can view their message:
The necessity of using a shared password to decrypt messages read by non-ProtonMail users has the potential to be problematic because it requires a way to get that password from Person A to Person B without letting any eavesdroppers discover what it is. PGP, by contrast, is based on a principle called public key encryption. The benefit of public key encryption is that it allows Person A to securely send a message to Person B without having to ever exchange sensitive security details.
Speaking via video chat at the South by Southwest Interactive conference earlier this year, Snowden posited the ?Greenwald test,” that any widely effective encrypted messaging system has to be simple enough for laymen to use it. ProtonMail certainly passes Snowden’s ?Greenwald test,” but, in order to do that, it does sacrifice some security in the process.
For one, ProtonMail is browser-based (as opposed to requiring a slew of different applications, like PGP) which, according to Yen, ?comes with some inherent weaknesses.”
?It is possible to do more secure implementations of PGP,” he says, ?but you would lose a lot of the ease of use.”
If Snowden wanted to use ProtonMail to send leaked documents to a non-ProtonMail using Greenwald, he would have had to find another way, such as an encrypted messaging app like Gliph or Seecrypt—a process that carries a degree of uncertainty.
Uncertainty is also the reason the company hasn’t yet committed to creating a mobile app. “We also have some security concerns with native apps because the iPhone and Android app stores are controlled by Apple and Google, and we can’t be sure that the NSA doesn’t compel Google or Apple to quietly backdoor those apps without us knowing,” ProtonMail co-founder and front-end developer Jason Stockman told CyrptoCoinNews. ?There is already a history of such activity, and it’s hard to prevent once we hand over the code to Apple and Google.”
Google is reportedly working on end-to-end encryption, but the company’s email system currently reads each and every one of your emails, gobbles up all that information, and then uses it show you targeted ads. ProtonMail’s creators insist they’ve designed the system in such a way that they wouldn’t even be able to do that if they wanted to. Instead of using advertising, ProtonMail is monetized on a freemium model with free basic accounts and $5/month paid accounts coming with increased storage. Naturally, they plan to accept Bitcoin.
Google ads aside, this architecture also makes it far more difficult for government officials to demand access to the private emails of ProtonMail users.
ProtonMail houses its servers, and is incorporated, in Switzerland—a country famous for respecting data privacy.
Yen notes that the response to ProtonMail has already been overwhelming. In less than a week following its launch, the service has signed up over 20,000 users from across the globe and been forced to temporarily halt the creation of new accounts due to a heavy server load.
?I think a lot of people feel that online privacy invasion is a real problem in society today and they appreciate the fact that we are trying to do something about it,” said Yen. ?It is an extremely difficult problem to tackle and what we have released so far is only the first step.”
“In the ideal world,” Yen added, “ProtonMail shouldn’t even have to exist.”
Photo by geralt/Pixabay (CC0 1.0)