Just browsing the internet on your Android device could hand hackers your credit card information.
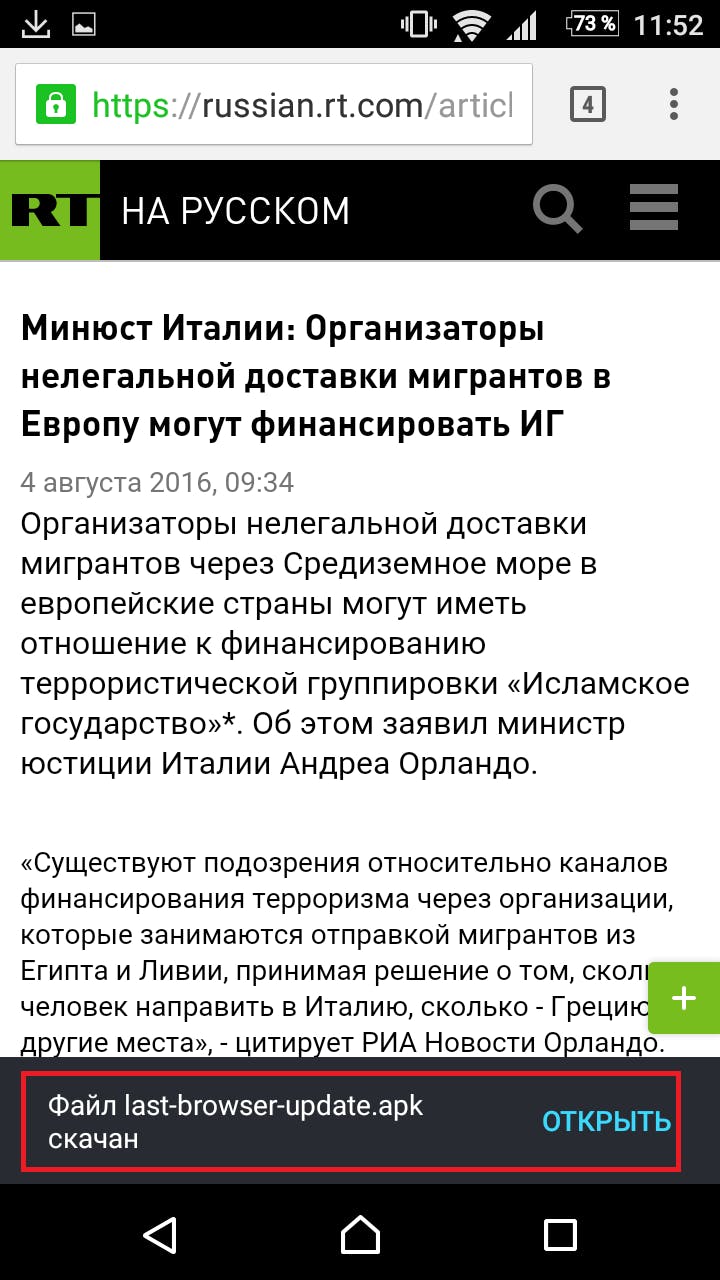
Researchers at the security firm Kaspersky Lab detailed on Monday a newly discovered banking Trojan distributed directly through Google‘s AdSense advertising network. Dubbed “Trojan-Banker.AndroidOS.Svpeng.q” by researchers Mikhail Kuzin and Nikita Buchka, the malware infects devices as soon as a user visits a page displaying the infected web ad.
“There you are, minding your own business, reading the news and BOOM!—no additional clicks or following links required,” write Kuzin and Buchka. “And be careful—it’s still out there!”
Used by some 15 million websites, AdSense allows third parties to display ads through its network for a fee. Google scans ads on its network for malware and allows website administrators to report ads they find problematic. But malicious code sometimes gets through.
A Google spokeswoman said the company is looking into the issue, but notes that the instance of this malicious ad appearing on a website cited by Kuzin and Buchka has since been corrected.
Buchka told the Daily Dot in an email that “Kaspersky Lab products have prevented nearly 20,000 (19,758) attempts to attack users” since the company first detected the malware on July 15.
As Kuzin and Buchka explain, the Svpeng banking malware works by automatically installing itself on a targeted user’s device then hiding the installation from the user and gaining admin rights to the device, which the researchers say makes it more difficult for antivirus software to remove it.
A user does not have to click on the malicious ad for the malware to install itself. Once installed, write Kuzin and Buchka, Svpeng “can steal information about the user’s bank cards via phishing windows, intercept, delete, and send text messages (this is necessary for attacks on remote banking systems that use SMS as a transport layer).”
Kuzin and Buchka recommend Android users install antivirus and other security programs to protect themselves against this malware. Buchka said an ad-blocker “will prevent users from downloading the malicious .apk simply by blocking all advertising on the mobile.”
Update 12pm CT, Aug. 15: Added comment from Google and Buchka.