A misconfigured storage device discovered by a security researcher in October left exposed thousands of internal files belonging to an explosives-handling company.
The files, which have since been secured, reportedly included details about facilities in three U.S. states where explosives are stored.
The leaky file repository belonged to Allied-Horizontal Wireline Services (AHWS), a leading wireline company with more than 400 employees and 70 wireline units throughout the United States. (“Wireline” is an industry term that refers to cabling technology used at oil and gas wells.) The company is licensed by the federal government to store and use explosives to complete an oil-drilling process known as “perforation.”
Chris Vickery, a lead security researcher at MacKeeper who notably discovered several misconfigured voter databases this year, found the breach in early October. After verifying the device’s owner, Vickery reached out to an AHWS executive, who quickly moved to secure the company’s data.
AHWS did not respond to a request for comment.
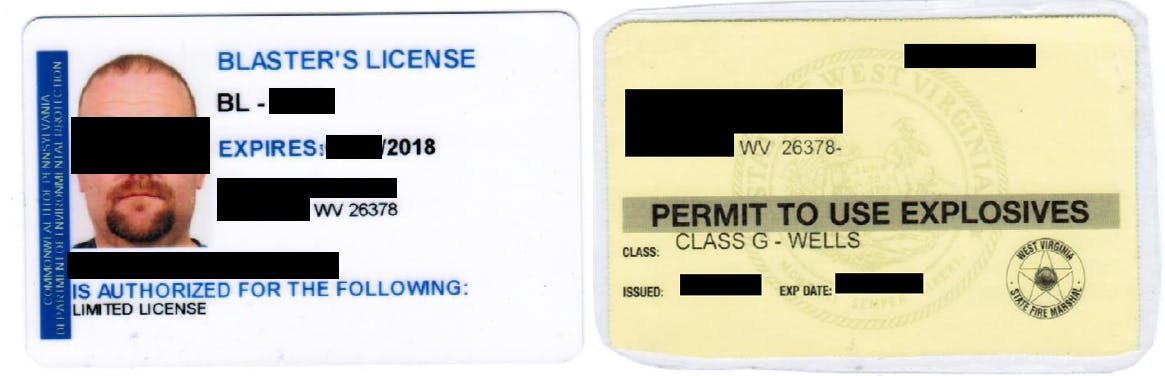
Among the files located online by Vickery were hundreds of high-quality scans of explosives handling licenses, a variety of AHWS employee information, and other files pertaining to the company’s contracts with leading oil companies, such as BP and Exxon. One database appeared to contain the personal information of every AHWS employee, including names, titles, Social Security numbers, and contact information.
Vickery told the Daily Dot this week that he went public about the breach due to public safety concerns stemming from the breadth of leaked data tied to the company’s use of explosives.
“The discovery of an exposed file repository for an explosives-handling company is alarming,” he said. “If bad guys wanted to know where explosives are being held, or who to blackmail into obtaining explosives, this would have been a prime knowledge base.”
“High quality scans of explosives-handling licenses were also found in the files, which raises the possibility of impersonating authorized explosives-handling personnel,” Vickery added.
In a statement, the Bureau of Alcohol, Tobacco, Firearms and Explosives (ATF) said that federal explosives licensees, on whom the agencies conduct extensive background checks, are “responsible for safeguarding their premises by establishing strong internal controls to prevent unauthorized entry to or possession of explosives.”
There are no federal laws prohibiting Allied-Horizontal Wireline Services from disclosing the location of its explosives, an ATF official said. “Licensees storing explosive materials must notify the authority having jurisdiction for fire safety in the locality where the explosive materials are stored.”
In a blog post on Thursday, Vickery praised AHWS for moving quickly to secure its data. “Their IT department also gets bonus points for not suggesting that I somehow ‘hacked’ them,” he said. “They were actually very grateful for the heads-up and couldn’t have been nicer to me. It’s refreshing when that happens.”