American democracy is quite literally under attack. Why aren’t we spending as much money as it takes to protect it?
According to a security review published by the Virginia Information Technologies Agency earlier this week, the electronic voting machines sold to that state (as well as Pennsylvania and Mississippi) by Advanced Voting Solutions “operate with a high level of risk.” Its administrator account, WiFi network, and voting results database were protected by easily guessable passwords; the AVS WINVote machines operated using Windows software that hadn’t received a security patch since 2004; and the WiFi network was encrypted with an algorithm so weak that most hackers can break it within minutes.
Make no mistake about it: Although news reports are required to mention that we don’t have proof election results were actually compromised in states with AVS WINVote machines, it would be naive to assume otherwise.
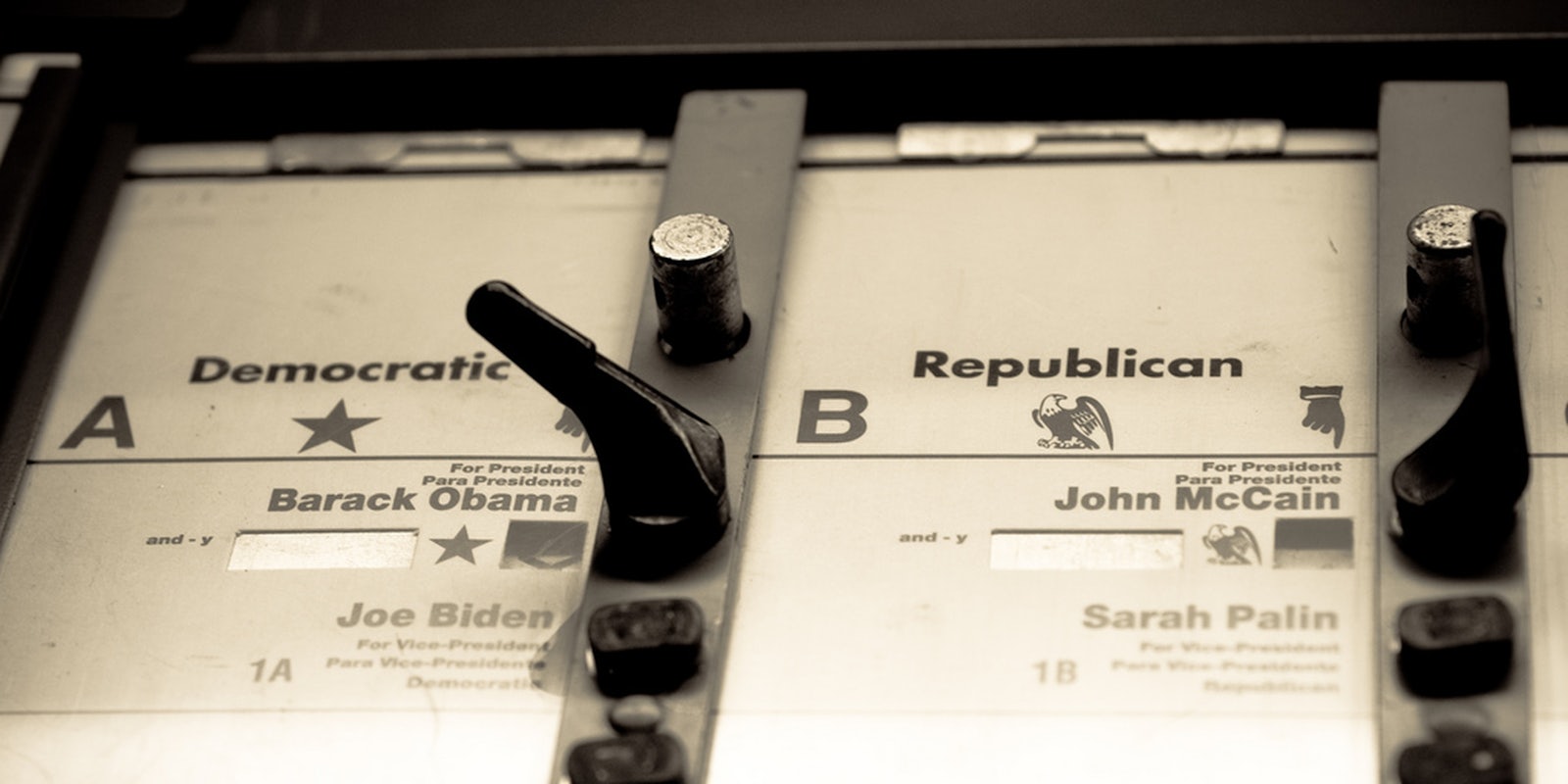
This isn’t even the first time that electronic voting machines were found to be insecure and woefully outdated. Back in 2008, private cybersecurity expert Ed Felten demonstrated that Sequoia Voting Machines could be hacked in seven minutes. Only four years before that, allegations arose that electronic voting machines made by Diebold in Ohio were fraudulently tilting that state to President George W. Bush.
This isn’t even the first time that electronic voting machines were found to be insecure and woefully outdated.
Needless to say, any hacker who was already inclined to tamper with election results in an electronic voting machine would have probably known in advance that they were very easy to crack. “If an election was held using the AVS WinVote, and it wasn’t hacked, it was only because no one tried,” observed Jeremy Epstein, a security expert who specialized in e-voting, in a post with Freedom to Tinker. “The vulnerabilities were so severe, and so trivial to exploit, that anyone with even a modicum of training could have succeeded.”
There is literally no way of knowing whether elections held in states with questionable voting machines were actually conducted honestly.
The revelations about Virginia’s voting machines is only the American government’s latest embarrassing cybersecurity incident. Last month, it was revealed that hackers (most likely Russian) managed to break into the White House and State Department networks, giving them access to sensitive information, such as the president’s schedule. This allowed them to “own” the State Department’s system for months.
Back in December, various cybersecurity experts called out the Federal Bureau of Investigations‘ shoddy case for attributing the Sony hack to the North Korea, as that the evidence the FBI had released to the public was far from conclusive. Even earlier than that, the Syrian Electronic Army managed to hack into the systems of U.S. defense contractors (though not the American government itself), as well as those used by various European and Middle Eastern governments.
In response to developments such as these, Central Intelligence Agency Director John Brennan recently announced a major reorganization within his agency, from shifting departmental responsibilities to creating a Directorate of Digital Information to oversee the CIA’s expansive cybersecurity efforts. “Our ability to carry out our responsibilities for human intelligence and national security responsibilities has become more challenging in today’s digital world,” Brennan explained to Reuters. “And so what we need to do as an agency is make sure we’re able to understand all of the aspects of that digital environment.”
There is literally no way of knowing whether elections held in states with questionable voting machines were actually conducted honestly.
This brings us to one major policy change that could prevent this debacle from occurring: Because the hacking of voting machines poses a direct threat to America’s democratic institutions, agencies responsible for protecting national security should be charged with guaranteeing their integrity. The preservation of the ballot box should be considered as much of a national security priority as the gold at Fort Knox or the weapons at Los Alamos.
Indeed, it is an even higher priority—while currency and bombs can enrich or empower a democratic government, only sound voting practices can ensure that democracy itself is healthy.
Another option would be to return to paper ballots, punch cards, and mechanical lever machines. For all the grief caused during the 2000 presidential election over butterfly ballots and hanging chads, the fact that votes were tabulated on physical objects at least provided investigators with tangible materials to sift through.
As the revelations in Virginia have clearly illustrated, one of the biggest downsides of electronic voting is that it is impossible to ever know for sure after the fact whether the process in a given election was tainted. If there is anything that could undermine faith in American democracy more than certainty that an election was stolen, it would be the knowledge that elections are probably stolen all the time and we’d never be any the wiser. Although you can tamper with paper results, they are nothing if not immune to hacking.
Either way, it is absolutely essential that cybersecurity become a front-and-center issue in future elections. Ironically, this could benefit of one candidate in particular—Hillary Clinton, whose decision to create a personalized email as secretary of state suddenly seems a whole lot smarter than her critics might be willing to admit. While our future political leaders don’t need to be especially tech savvy, we should expect them to be ahead of the curve when it comes to identifying potential national security threats and protecting us from them.
When it comes to electronic voting, this will require them to think outside the box when it comes to preserving the integrity of our electoral process. What cannot continue is the overwhelming public indifference to this dilemma.
Matt Rozsa is a Ph.D. student in history at Lehigh University, as well as a political columnist. His editorials have been published in the Daily Dot, Salon, the Good Men Project, Mic, MSNBC, and various college newspapers and blogs. I actively encourage people to reach out to me at matt.rozsa@gmail.com.
Photo via John Morton/Flickr (CC BY SA 2.0)