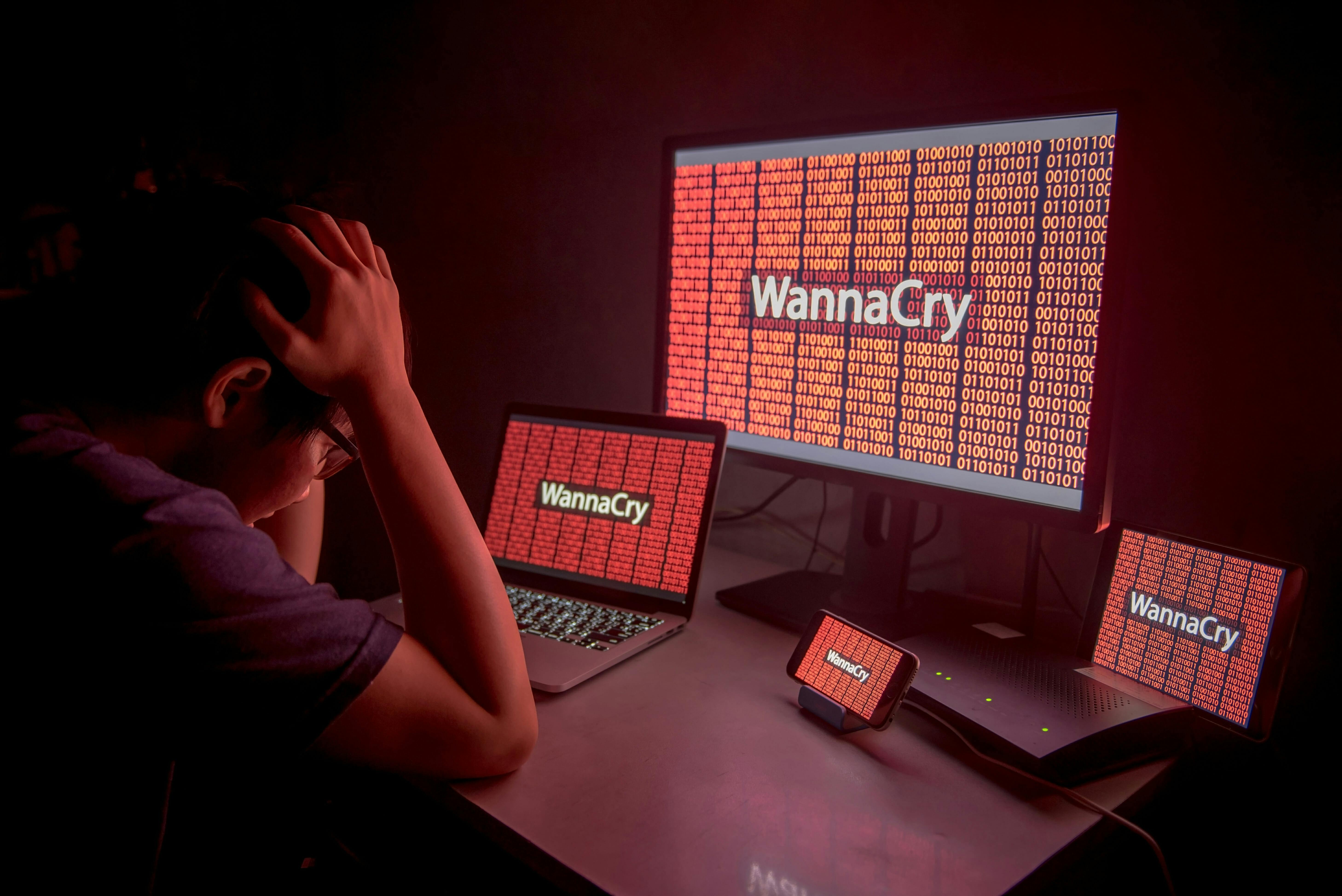
The recent spread of the WannaCry malware offered a grim reminder of the mounting threat of ransomware attacks. Over the past years, ransomware attacks have turned into a lucrative business, raking in millions of dollars for cybercriminals. The degree of efficiency, success rate, and low skill requirements of ransomware attacks are making them more popular than other money-making schemes, such as stealing credit card numbers and bank account credentials.
What is ransomware?
Ransomware is a malware that encrypts the files on your computer, making them inaccessible. It then asks you to pay a certain sum to the attacker in order to receive the key to decrypt and regain access to the files.
The target of ransomware attacks can be anyone, from hospitals to police departments to online casinos and unfortunate individuals. If you want to avoid having to choose between letting go of your files and forking over hundreds of thousands of dollars to cyberthieves, here are a few steps that can protect you against ransomware.
Ransomware protection: 4 essential steps
1. Keep everything patched and up to date
Like most malware, ransomware relies on vulnerabilities in your software and operating system to carry out its misdeeds. The WannaCry ransomware exploited a security hole in the Windows operating system to spread across networks.
Vulnerabilities can be in anything, including your browser, email application, web server, and practically any other software that connects to the internet. Vendors regularly issue patches for their software, which you should always install as soon as possible.
Again, drawing lessons from the WannaCry episode, Microsoft had issued a patch for the vulnerability a month before the attack, but unfortunately, hundreds of the thousands of computers hadn’t installed it.
If you have an antivirus—which you should, by the way—make sure that it’s set to automatically install the latest virus definitions.
If you’re using an outdated operating system that is no longer supported by the vendor, seriously consider upgrading to a newer version.
2. Minimize your attack surface
As long as you’re connected to the internet, there’s no such thing as absolute security. Even air-gapped systems (networks and computers that aren’t connected to the internet) aren’t absolutely secure.
An up-to-date antivirus won’t protect you against the thousands of unknown viruses that are dished out every day, and a patched system won’t stop a zero-day attack (an attack that exploits a vulnerability that isn’t publicly known).
Therefore, to improve your chances in fending off the more devious kinds of attacks, you should plug the holes in your network. All major operating systems come with easy-to-use firewalls. Make sure your firewall is turned on, and only open ports that you absolutely need.
Also, turn off software and operating system features that you don’t need. That includes file-sharing services and excessive browser plugins such as Flash and Java, which are riddled with security holes.
Another important measure that can reduce your attack surface is keeping your work on a limited account as opposed to an administrative account. By avoiding an administrative account, you’ll be limiting the access of the malware in case it strikes.
READ MORE:
- What’s the most secure operating system?
- How to encrypt an iPhone in seconds
- Here are the 13 best deep web search engines
3. Manage your trust
Attackers often use phishing and spear phishing emails to deliver ransomware. Phishing is a type of social-engineering scam that involves targeting victims with legitimate-looking messages that contain malicious links or infected attachments. Since the targets think the email comes from a trustworthy source, they’ll download and open the attachment, which will then deliver the malicious payload.
In this regard, be very careful with the emails you receive, and don’t open any attachments unless you’re absolutely certain of the source. In case there’s any doubt, use other means such as phone or social media to verify the authenticity of the message with the sender.
You should be absolutely wary of some file formats, including macro-embedded MS Office documents (.doc, .xls), compressed archives (.zip, .rar) and executables (.exe, .bat). Cybercriminals have a history of using Word macros to stage ransomware attacks.
4. Have a good backup plan
No matter how tough your defenses are, you should always prepare for when the worst comes to pass. While there have been cases where ransomware encryption has been reversed, for the most part, nothing short of paying the attackers will decrypt your files.
That’s why you should always keep backups of your files. For files that will not be modified, such as family pictures and videos, you can use DVDs. For others, you should use other removable media.
External drives work well, but they will be of no use if they’re connected to your computer when it becomes infected.
One trick I find useful is to enable full-disk encryption (FDE) on backup drives and removable storage that I don’t regularly use. FDE encrypts the entire contents of the drive and only makes it accessible when the associated passcode is entered. Ransomware won’t be able to access FDE drives that haven’t been unlocked at the time of infection.
Cloud backups are good too as long as you don’t map them to local drives because ransomware will iterate through all your local drives and encrypt their content, whether they’re on your hard drive or in the cloud.
And beware of storing your archives in shared folders. Some breeds of ransomware will scan your network and find unmapped shared folders and encrypt their content too.
Ben Dickson is a software engineer and the founder of TechTalks. Follow his tweets at @bendee983 and his updates on Facebook.


