U.S. intelligence agencies on Thursday released a detailed report laying out evidence showing that Russia’s government orchestrated cyberattacks meant to tamper with America’s presidential election.
The 13-page Joint Analysis Report (JAR), released by the FBI and the Department of Homeland Security (DHS), details the technical methods two Russian intelligence agencies used to “compromise and exploit networks and endpoints associated with the U.S. election, as well as a range of U.S. Government, political, and private sector entities.”
The report coincides with the White House announcement that it has ejected 35 Russian intelligence diplomats and imposed sanctions on nine Russian officials or entities.
The Obama administration imposed sanctions on four officers of the Russian military intelligence agency—the Main Intelligence Directorate, or GRU—whom the U.S. believes orchestrated cyberattacks against the Democratic National Committee (DNC) and John Podesta, former campaign manager for Democratic nominee Hillary Clinton. The U.S. has also sanctioned the GRU itself, as well as Russia’s civilian intelligence agency, the Federal Security Service, or FSB. The U.S. also imposed sanctions on three companies the White House says aided GRU’s cyberattacks.
U.S. intelligence dubbed the Russian cyber campaign “Grizzly Steppe” in its report, which repeatedly refers to the attacks on the DNC and Podesta but does not mention them by name.
Emails stolen from the DNC, the Democratic Congressional Campaign Committee (DCCC), and Podesta were published online by various outlets, including WikiLeaks, which has denied Russian operatives were its source for more than 50,000 Podesta emails.
President-elect Donald Trump has repeatedly denied that U.S. intelligence agencies know Russia hacked Democratic entities, calling the claims “ridiculous” and urging Americans to “get on with our lives.” On Thursday evening, Trump reiterated the latter sentiment while agreeing to meeting with intelligence agencies for a briefing on the Russia-led cyberattacks.
“It is time for our country to move on to bigger and better things,” Trump said in a short statement. “Nevertheless, in the interest of our country and its great people, I will meet with leaders of the intelligence community next week in order to be updated on the facts of this situation.”
The JAR contains a variety of intelligence jargon. Here’s a quick glossary:
- RIS: Shorthand for both the GRU and the FSB, Russia’s military and civilian intelligence agencies, respectively.
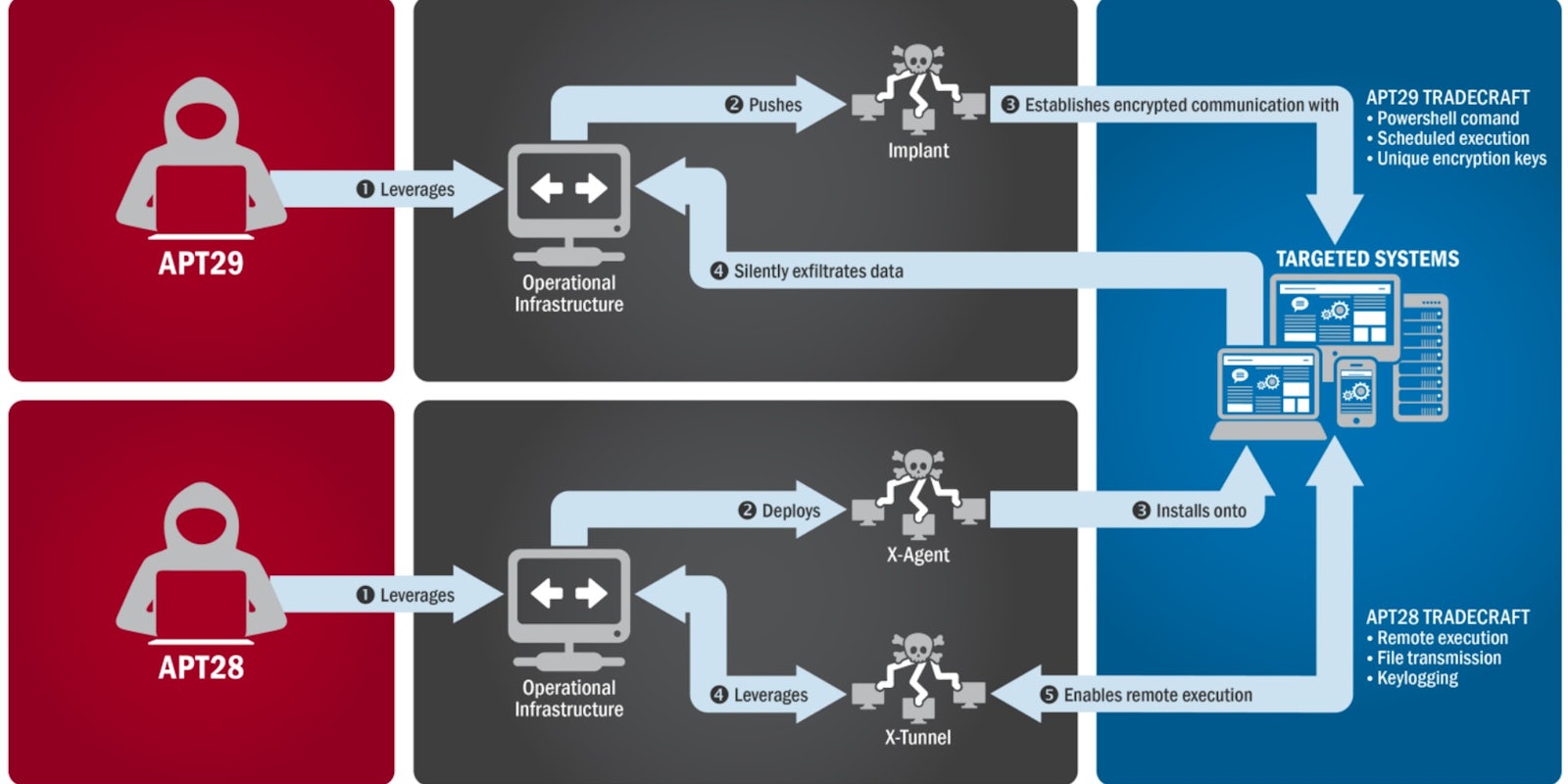
- APT28: A GRU-run hacking group the U.S. says breached the DNC and Podesta and provided documents to WikiLeaks.
- APT29: An FSB-run hacking group said to have infiltrated the DNC’s system for over a year.
- RATs: Remote Access Tools, or viruses used to infiltrate targets.
- Spearphishing: A targeted technique used to trick specific users into handing over sensitive information or downloading malware; APT28 is said to have used a spearphishing email to gain Podesta’s Gmail credentials.
The full JAR is below:
Update 8:30pm CT, Dec. 29: Added Trump statement released Thursday evening.