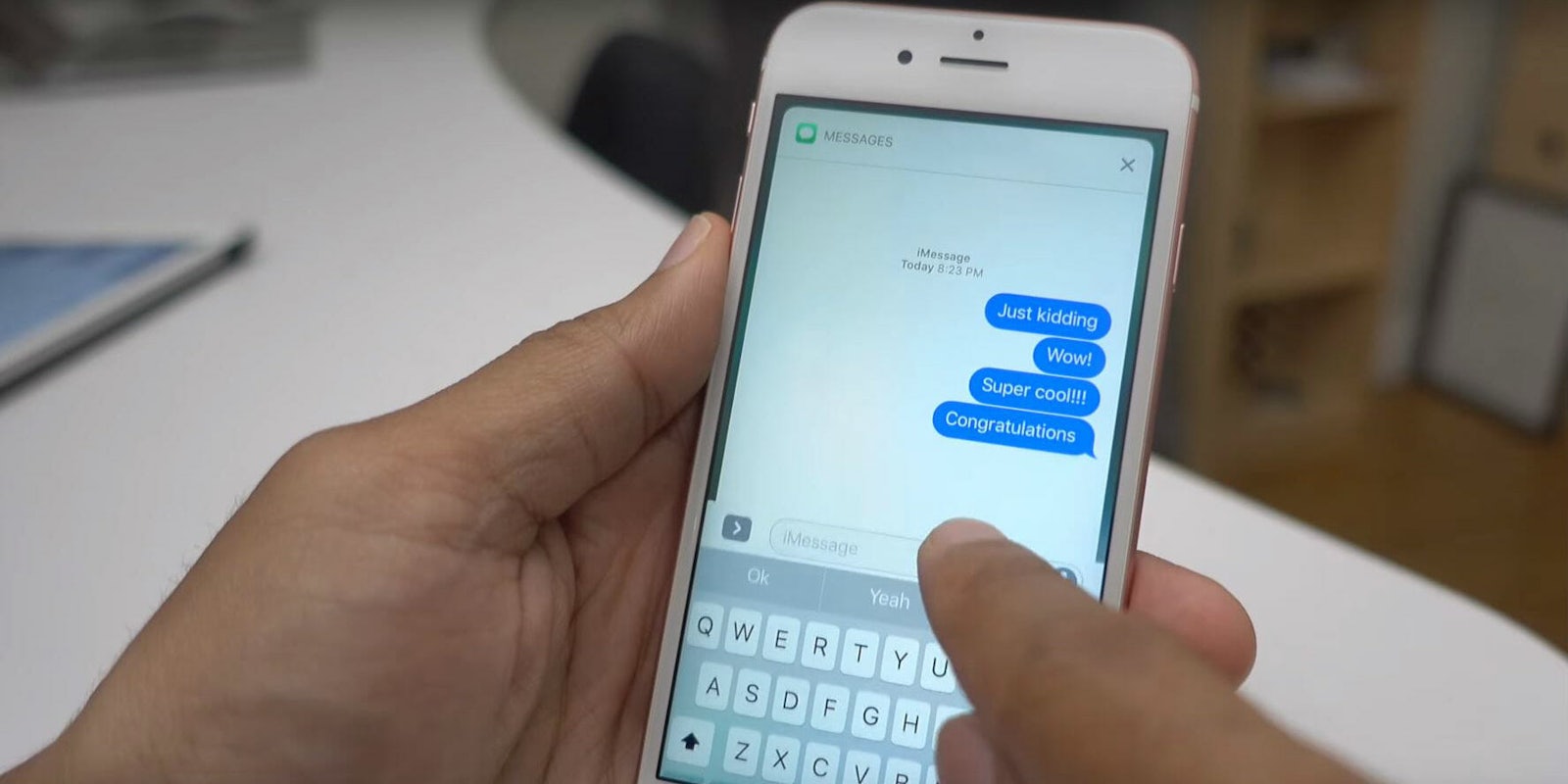
A new “chaiOS” bug was discovered in Apple operating systems this week, and it causes the iMessage app to crash. Using a simple web address, pranksters can overload the app with a long string of text, forcing it to freeze and reboot. The nasty bug works even when the recipient doesn’t open the full link.
It can cause the application to crash just from the pressure put on by the link preview, Tom’s Guide reports. If the app doesn’t crash before then, it takes users to a GitHub page that initiates the bug. Users have reported freezing, crashes, restarts, and resprings (when iOS restarts its UI, a process that takes about 10 seconds).
It’s been a rough couple of months for iPhone owners. First, Apple admitted it was slowing down phones to prevent them from shutting off. Then Intel’s Spectre and Meltdown fiasco cast doubt on the security of practically every modern computing device in existence. A fix was discovered, but all it did was convert privacy concerns into anger about performance slowdowns. Not to mention the ridiculous bug that caused auto-correct to replace the letter “i” with “A [?].”
This new type of attack is called a “text bomb” and in this case, it can affect iPhones, iPads, and Macs. It seems to have been created by Abraham Masri, an iPhone jailbreaker who shared the link on social media and warned of its abilities, urging people, “Don’t use it for bad stuff.” It now appears Github banned Masri, effectively taking down the link. Masri says he has no intention of reposting the link but other users already claim to have recreated it. He explained why he posted it in the first place in a follow-up tweet.
“The bug I released was to get @Apple’s attention. It’s just an html file. @Github always hosted jailbreaks (even .ipa files) that might’ve included malware. I don’t understand why you’d ban my account. Btw, I always report bugs before releasing them,” he wrote.
https://twitter.com/cheesecakeufo/status/953692349623947264
Advice for protecting yourself from this type of bug is simple: Don’t press on links you’re not familiar with, even if they’re sent from someone you may know. Things get tricky if you do. Some users say their iMessage app didn’t restart itself after it shut down and force-quitting wasn’t an option. Twitter user @D3mRid3rOS replied to Masri’s text with a Safari link designed to fix the problem, but we’re not convinced it won’t end up harming your device. Henry Casey at Tom’s Guide said the link saved his phone but noted “a plethora of ads for online gambling.”
From what we can tell, this type of bug does not put your personal information in jeopardy nor does it put your device in danger of being hijacked. While this infuriating vulnerability is easy to avoid using common sense, it’s unnerving nonetheless. A single link shouldn’t be able to paralyze one of the most popular iPhone apps.
We have informed Apple of the vulnerability and will update this article if we learn more. In the meantime, be on the lookout for a software update that patches the bug.