If Donald Trump becomes president of the United States, many will undoubtedly point their regular-sized fingers at the leak of nearly 20,000 emails stolen from the Democratic National Committee as the precise moment things went south for Hillary Clinton.
The emails, obtained by a hacker going by the moniker Guccifer 2.0 and put online in a searchable database by the radical transparency organization WikiLeaks, showed party officials actively working to promote the Clinton campaign as the expense of the insurgent effort mounted by Vermont Sen. Bernie Sanders. The leak enraged many Sanders supporters, who already viewed the entire primary process as slanted against them, and hardened their will to either vote for a third-party or stay home on Election Day rather than casting ballots for Clinton.
This type of hack—which, the New York Times reported Wednesday, may have targeted more than 100 people and organizations associated with the DNC—will not be the last of its kind. Unless organizations—including your own—start demanding it on every email system they use, a lot of other companies, nonprofits, and government organizations are going to serve as new cautionary tales about not demanding more out of their technology.
At its core, what happened at the DNC isn’t fundamentally all that different than what happened to Sony 2014—hackers with an axe to grind breached the company’s servers and released all of the information contained therein to the world.
Think about the last 500 emails you sent to your coworkers. Imagine if someone who wanted to see your company crash and burn had access to those emails and could frame them such that they appeared in the worst possible light when presented to a content-hungry public. That sort of transparency can lead to positive outcomes, like revelations about the realities of the gender pay gap in Hollywood, but the risk that exists for every corporation, nonprofit, and governmental agency on the planet is very real.
As long as computer systems are connected to the internet, those computers systems are going to hacked. That’s just kind of the deal. However, not all email systems are created equal. If the DNC’s email system had one specific feature that just so happens to be included on the email system used by Guccifer 2.0, there likely would be no gargantuan DNC email leak.
That feature, email inbox encryption, would have prevented what likely started as a relatively isolated attack from spreading into every nook and cranny of the DNC’s email system. It’s a feature that had the potential to be a deciding factor in the selection of the next leader of the free world but isn’t universally available among email providers.
When Guccifer 2.0 communicated with the Hill for a story the political news outlet was writing about the hack, he did so using an email service called ProtonMail.
Created in 2013 by a group of former engineers at CERN, the European nuclear research organization that runs the Large Hadron Collider and the birthplace of the World Wide Web, ProtonMail is a Switzerland-based webmail service that puts a high priority on privacy though the use of strong encryption while striving to make the user experience as simple and straightforward as Gmail.
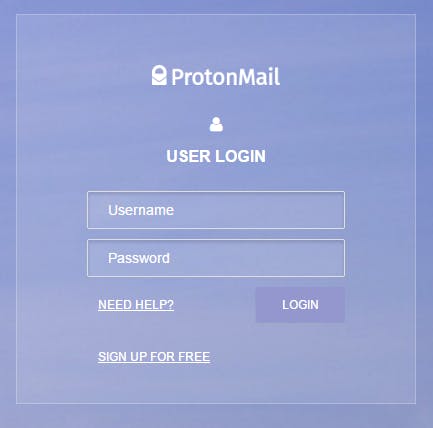
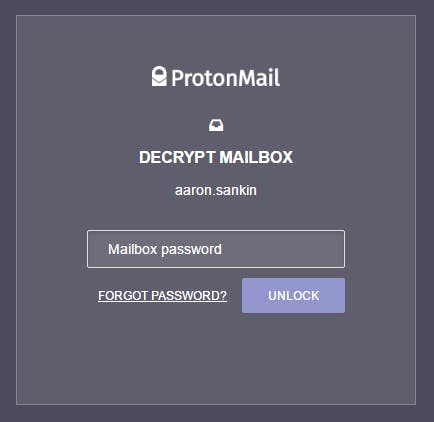
When a user logs into their ProtonMail account, it asks for their username and password.
After completing that first layer of security, ProtonMail then instructs users to enter another password to decrypt their inbox.
ProtonMail automatically encrypts the contents of every user’s inbox by default—meaning it uses a computer algorithm to temporarily scramble all the messages in the inbox into unreadable gibberish. In the DNC hack, the attacker was able to find a single weak point in the system and then freely bounce around from one inbox to another, reading anything they so desired. If the DNC’s inboxes were fully encrypted, an attacker could gain access to everything on the server but would largely come away with nothing more than endless strings of seemingly random characters.
Using a “brute force” method of repeated guessing, another algorithm could unscramble the messages, but that process would take thousands of years.
“I have no doubt that if the DNC was using ProtonMail’s encrypted email or some other form of end-to-end encryption in their communications, it would have been far less likely for their emails to be completely compromised,” says ProtonMail co-founder Andy Yen. “Most cybersecurity defenses these days are designed to keep attackers out, which, history has shown, isn’t a viable strategy. Compromises are a matter of when, not if.”
Yen says the key is “keeping only encrypted data on the servers,” which would better “resist compromises” and potentially prevent large-scale access to emails. If a breach did happen on this kind of system, it’s more likely “to result in leaks of single accounts and not the entire system,” Yen adds. “End-to-end encryption is critically important for providing better security for the world’s digital infrastructure.”
Most email systems do allow some form of encryption, usually in the form of comparability with another application, such a Mailvelope, which allows users to encrypt messages in transit using the PGP encryption scheme, or other applications that add PGP encryption on top of the email service itself.
While email encryption has gotten considerably more user-friendly over the years, it’s still fairly complicated. NSA leaker Edward Snowden spent months unsuccessfully trying to give journalist Glenn Greenwald the classified documents he took from the intelligence agency’s servers because Greenwald didn’t figure out how to send and receive encrypted emails using PGP.
Encrypting inboxes by default lowers the barrier to entry. An email sent from a Gmail account to a ProtonMail account could still be intercepted and read in transit, but it’s safe in the ProtonMail user’s account.
“Most cybersecurity defenses these days are designed to keep attackers out, which, history has shown, isn’t a viable strategy.”
“Many people work on subject matter that makes them targets for hackers, both international and domestic, and this DNC hack is an example of how private conversations can become embarrassingly public,” says Rebecca Jeschke of the Electronic Frontier Foundation, a digital rights group that advocates for the widespread use of encryption across the internet. “Encryption would have made this hack much harder and increased the chances that this correspondence never made the national news.”
Individual email encryption adds a strong level of security, but it’s important to note that if the DNC or Sony were running their internal email systems on Gmail, through Google Apps for Work, it’s extremely unlikely an attacker who compromised one account could have infiltrated the rest of the company’s email inboxes. While Gmail doesn’t run individual email inbox encryption like ProtonMail does, all of the information is kept protected, according to the company. “From the moment an incoming mail is ‘in Google’ — whether at rest, in transit between data centers, or in transit within a data center — it is always encrypted,” a Google spokesperson told the Daily Dot.
If the DNC had just used Gmail, instead of trying to run its own email system without the appropriate level of security, the leak likely wouldn’t have happened, at least not with nearly the same level of damage.
Even so, email providers that use individual encrypted email inboxes insist there’s an advantage to encrypting the messages in each user’s account individually.
“There is vastly greater security associated with having individually encrypted mailboxes,” says Robert Beens, CEO of the encrypted email service StartMail, which doesn’t even keep a record of a user’s password on its servers as a way to increase security. “To unlock … just a single user’s vault, an attacker would typically have to individually try many trillions of possible passwords—each one using cryptography that takes time. Whereas with a centralized key (a less secure technique that we do not employ), an attacker who found that single key could potentially see everyone’s data. That’s why we provision a separate ‘user vault’ for each user’s mailbox and encrypt each one separately.”
StartMail also has a built-in system to increase security for everyone its users contact, including those without StartMail accounts. One of the first things that tipped off the DNC that its system may have been compromised was the notifications popping up on the Yahoo email account of Democratic consultant Alexandra Chalupa, who was working on opposition research about Trump campaign manager Paul Manafort. “We strongly suspect that your account has been the target of state-sponsored actors,” the notifications read.
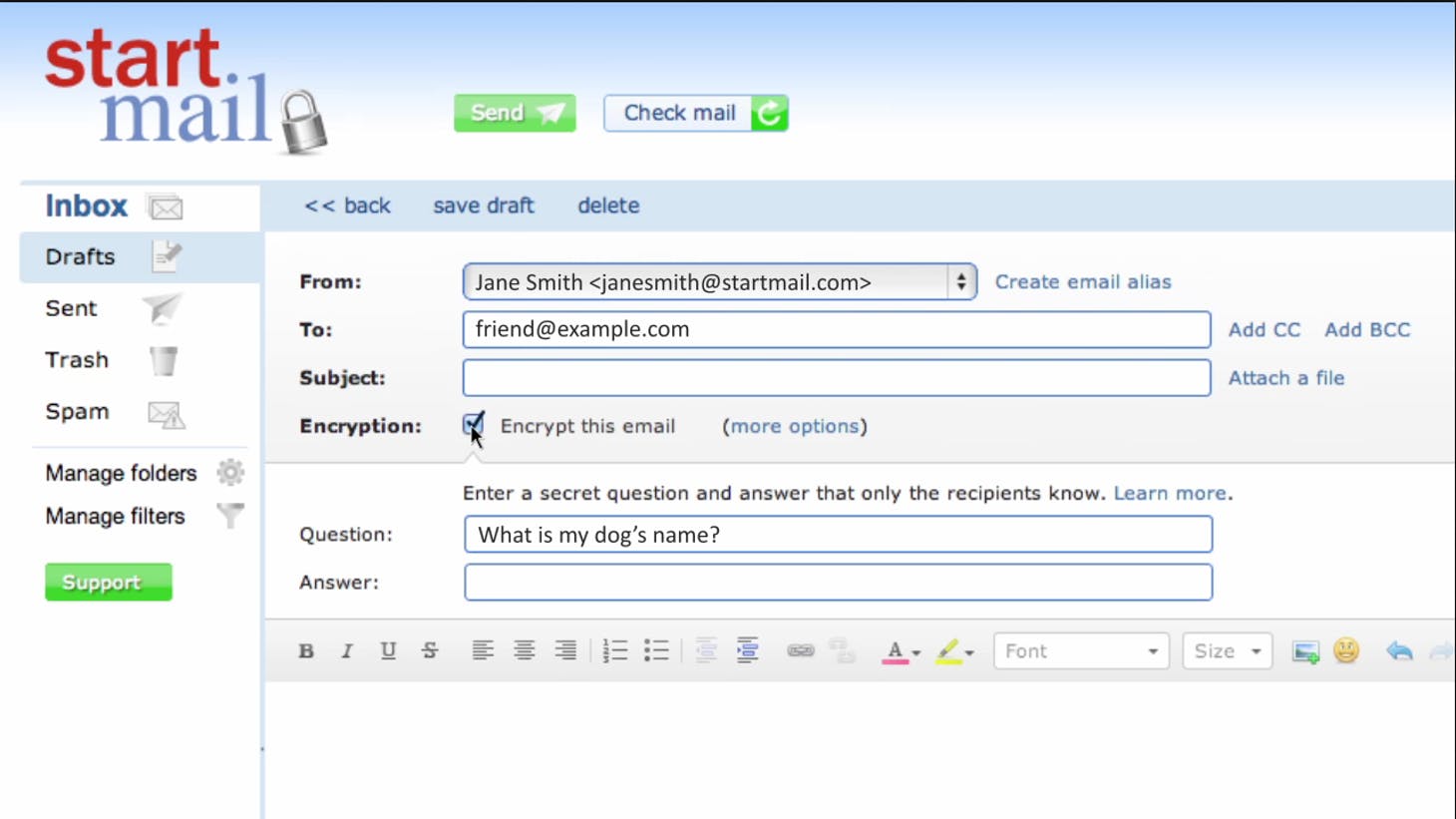
StartMail uses a feature called Q&A encryption that allows users to create a question-and-answer pair that locks and then unlocks encrypted messages. If a sender using StartMail turns on Q&A encryption with the question “How big are Donald Trump’s hands?” the recipient can decrypt that message as long as they know the pre-determined answer—such as, “totally normal-sized, thank you very much.”
The key here is the Q&A encryption works between StartMail users and users of any email service. If the DNC had insisted on using StartMail’s Q&A encryption in its communications with Chalupa, hackers who compromised the consultant’s Yahoo account wouldn’t have been able to read the messages they exchanged without also guessing the answer to the question.
Ladar Levinson has been working on thorny problems around increased email security for over a decade. His pioneering encrypted email service Lavabit was popular with privacy-minded nerds until he shuttered it in 2013, after the U.S. government forced him to hand over the ability to decrypt all his users’ messages as part of its investigation into Lavabit’s most famous user—Edward Snowden.
“All of these other systems we’ve developed over the past 40 or 50 years [to bolster email security]—control lists, usernames and passwords, firewalls—if you trick them and get access to the raw data, the entire system breaks down,” Levinson says. “Whereas, with encryption, even if you trick the system into giving you the data, unless you can also steal the encryption key, that data is useless.”
Levinson has spent the past few years working on a new encrypted email system called DarkMail, which he hopes to get into the alpha stage in the coming months. DarkMail does not use a second, separate password to decrypt inboxes. Instead, it ties the decryption key to a single password that is also used to log in to a user’s account—but the fundamental principle remains the same: Access to the email server would be useless without also having to access every individual user’s personal password.
To a certain degree, a lot of the most stringent security features for email systems decrease the functionality of those systems. Take, for example, password resets. On a standard email system, when a user forgets his or her password, it’s a simple, straightforward process. When email is encrypted to maximum security, there are no password resets because, if user passwords were kept somewhere on the server, they could be compromised by an attacker. Under that setup, if a user shows up without a password in hand, they’re likely out of luck.
“Edward Snowden had an encrypted email account with Lavabit, and he actually forgot his password once upon a time,” Levinson recalls. “We could verify his identity because he was a paying customer, but when we reset his password, he lost access to all of the messages that were already in his account. That’s one of those issues that most users don’t expect and don’t want. But, when you add encryption, it becomes an immutable fact.”
StartMail gets around this password recovery problem by through the use of handful of different recovery mechanism, like making users to store a separate recovery code on their own systems or requiring multiple people to authenticate an account recovery request. All of these recovery methods decrease security because they put more responsibility on individual users to manage their own privacy rather than leaving it to the trained professionals who set up and manage StartMail’s servers.
There’s also the problem of scale. Building an encrypted email system isn’t easy. Doing it correctly requires a wide variety of disparate coding skills, and the whole endeavor gets even more difficult as the project gets bigger and bigger. “Where mail becomes very complicated is at scale,” Levinson explains. “It’s one of these things that very few people understand unless they’ve lived through it. If you have enough volume and enough users that it can’t be combined to a single server, that’s when your scale problem comes in. I learned it first-hand the first year I operated Lavabit.”
When Levinson started Lavabit, which was then called NerdShack, he saw new email providers popping up on a near-daily basis and then shutting down within a year. Once they got a certain size, the technical workload of maintaining them meant having to scale to multiple systems where they would have to start charging users or shut their doors entirely.
The solution for a lot of providers is to lean on the cloud infrastructures built by web giants like Google or Amazon, but that comes with its own set of issues. “Given what we know about the NSA snooping programs and their ability to tap into Amazon and Microsoft via court orders or National Security Letters, we simply cannot use a cloud based provider and still have any expectation of privacy,” Yen says. “This forced ProtonMail to build our own secure email cloud using hardware that we own outright and exclusively manage in four data centers in Switzerland. Because ProtonMail has millions of users actively using our encrypted email service, the amount of storage and compute power required is massive. We’re essentially building out infrastructure like Gmail, complete with a 24/7 operations center.”
Companies like Google are only able to offer email for free to millions of people around the world because they have other ways to monetize the service. Google, for example, mines emails for keywords and then serves ads to users based on the content of those emails. While Google could theoretically to do the same with fully encrypted emails, it would likely be considerably more difficult.
“Edward Snowden had an encrypted email account with Lavabit, and he actually forgot his password once upon a time.”
When Levinson ran Lavabit, he made a few cents a day on advertisements. But, since those ads weren’t based on data mining, they were entirely random. The real money in online advertisement is in targeted ads that speak directly to the interests and preferences of each individual user. Even at an enormous scale, it would difficult to support service like Gmail based entirely on ads that aren’t informed by a plethora of user data.
That’s why getting customers to pay for an email service is the only way to ensure strong security protections. Both ProtonMail and StartMail offer their email service, for a fee, to organizational clients like corporations, nonprofits, and governmental agencies. For organizations that want to ensure security and privacy for their members, using one of these email providers is an important question.
That said, companies simply looking to avoid what happened to the DNC could also just run their email system off of the Gmail infrastructure, which would have prevented the full extent of the DNC hack as well.
When it comes to security, email systems are often imperfect beasts. “The protocols [for email] were developed in the 1970s. Back then, you were talking about a dozen universities and all the system administrators knew each other and went to each other baby showers and weddings,” Levinson says. “There was a lot of trust back then. So, security wasn’t just an afterthought, it wasn’t thought about at all. Over the years, extensions have been bolted onto email to improve its security. But, because they’re bolted on, they’re both difficult and they are optional, because every system had to be backwards compatible all the way back to the 1970s, compatible with systems that may not implement a given security extension.”
A lot of email systems have solved these security problems, as least partially, but some of these solutions provide more security than others. For organizations looking at setting up their email system, simply asking the question of whether a given setup will protect them from a DNC-style hack needs to be one of the first things on their list.