The hacking world’s attention was captivated Monday morning when a group called the Shadow Brokers claimed to have hacked the National Security Agency’s Equation Group, a team of American hackers that have been described as both “omnipotent” and “the most advanced” threat cyberspace has ever seen.
While ranting against “wealthy elites,” the Shadow Brokers are now auctioning off what they claim to be a small but incredibly potent set of Equation Group’s cyberweapons to the highest bidder.
The bidding for the potential cyberweapons has officially begun considerably lower than the asking price. The Shadow Broker’s Bitcoin address shows a kick-off bid of 0.0355 BTC, equivalent to less than $20.
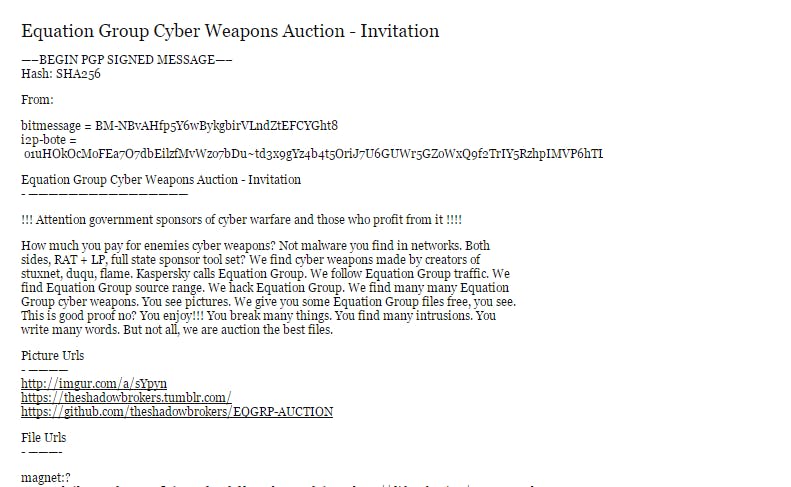
“We follow Equation Group traffic,” the Shadow Broker website claims. “We find Equation Group source range. We hack Equation Group. We find many many Equation Group cyber weapons. You see pictures. We give you some Equation Group files free, you see. This is good proof no? You enjoy!!! You break many things. You find many intrusions. You write many words. But not all, we are auction the best files.”
The English is broken, the promises are huge, and the initial reaction was dead silence.
After a Monday morning of closer examination, however, cybersecurity experts are now opening up to the idea that this actually could be the real deal: A small (the auctioned data clocks in at 131MB) but stunning set of stolen data straight from the NSA.
The incident is so new that it still evokes major skepticism. Even now, more information is needed.
“I haven’t tested the exploits, but they definitely look like legitimate exploits,” Matt Suiche, founder of UAE-based cybersecurity startup Comae Technologies, told the Daily Dot.
The revelation of this potential hack against the NSA comes on the heels of a substantial cyberattack against the Democratic National Committee and the personal accounts of over 100 Democratic Party officials and groups.
No one has yet definitively and on-the-record placed blame for those attacks, but many reports say American intelligence are pointing the finger right at Moscow. Serious and definitive attribution for cyberattacks at the highest level is extremely difficult and often impossible, making any blame a highly politicized act.
The timing of this Shadow Brokers–NSA revelation quickly following the DNC hack has many people wondering if and how the Shadow Brokers fit into the increasingly tense Washington–Moscow geopolitical game being played out as America’s 2016 election approaches, while Russia acts to push back against what many in the Kremlin reportedly see as decades-old American and NATO arrogance and aggression.
There has been no visible blame or retaliation for the DNC hack. But what about what’s happening behind the scenes? We don’t know, but observers say the speculation—let’s be clear, we are very much in the realm of speculation right now—sets the stage for a 21st century cold war.
https://twitter.com/pwnallthethings/status/765182756708032512
https://twitter.com/botherder/status/765213701070815236
“There are a lot of people in Ft Meade shitting bricks,” Nicholas Weaver, a computer scientist at the University of California, Berkeley, tweeted as he reviewed the alleged hackers’ claims. Ft. Meade is the NSA’s famous headquarters.
Here’s how the Shadow Brokers grabbed the spotlight.
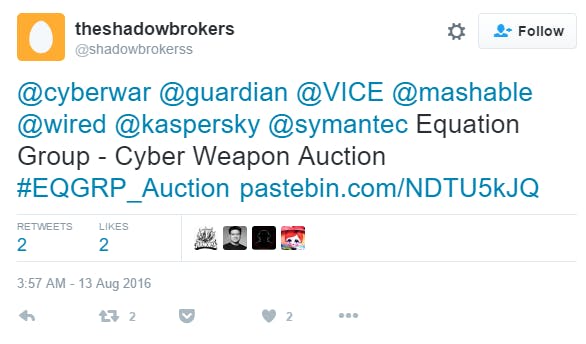
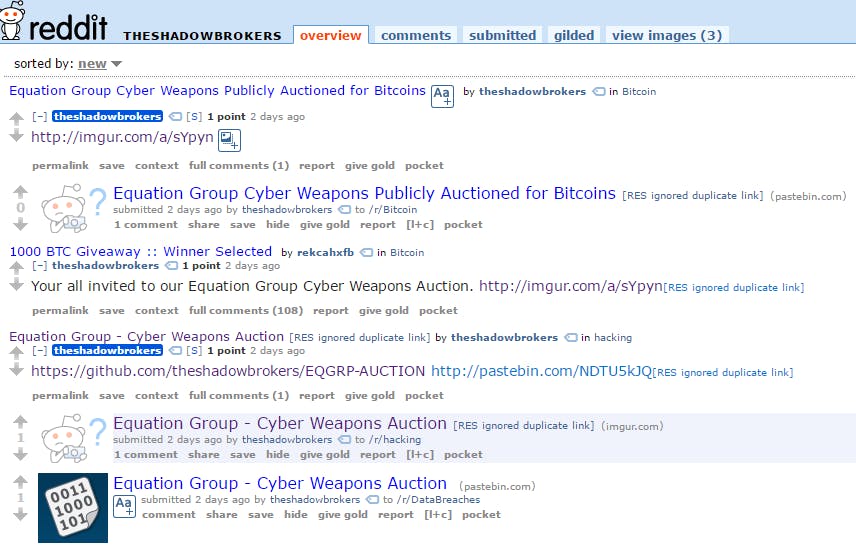
Beginning on Saturday, the group registered Tumblr, Reddit, Twitter, and Github accounts and began promoting themselves. They tweeted popular media accounts, posted to specialty subreddits, and posted a huge auction price in an apparent attempt to build buzz around their work.
Not much attention was paid to the Shadow Brokers until early Monday morning when Mikko Hypponen, a popular cybersecurity executive at F-Secure, tweeted the group’s Tumblr page.
The group badly wanted American eyeballs. On Monday—the best day to break news for a chance to dominate the week’s news cycle—they got it. Now they want to go off to the races.
The name “Shadow Brokers” may come from the hugely successful science fiction video game Mass Effect. In that universe, the Shadow Broker is the head of an organization that auctions valuable information. The parallels are obvious. It should be noted too that in a sequel, the highly secretive Shadow Broker is the victim of data breaches about himself.
The Shadow Brokers offered up screenshots and some free files to prove their bonafides before asking as much as 1 million bitcoins worth over $565 million to dump the entire collection for free to everyone.
“The ‘free files,’ if not legitimate, are extremely elaborate for a fraud,” Matt Tait, CEO of Capital Alpha Security, said. “Although, that said, if the intention is to solicit donations that might be ‘worth it’ for the hacker.”
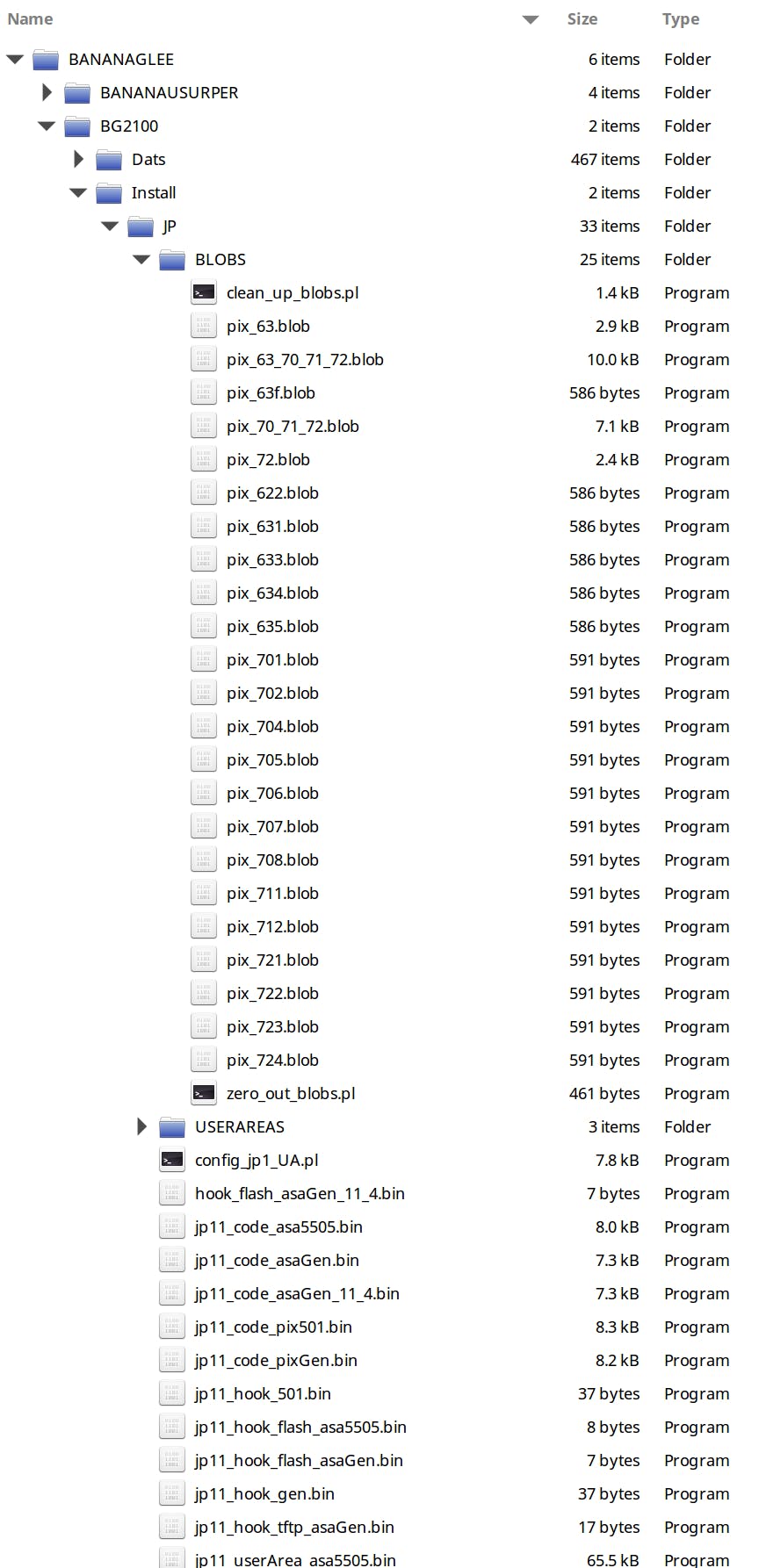
The files offered by the group reference code names used in the NSA’s Advanced Network Technology (ANT) catalog that was leaked by Edward Snowden, a fact pointed out by Thomas Rid, a professor in the Department of War Studies at King’s College London.
The full Snowden leaks are not currently available to the public. However, once journalists and experts with full access begin cross-referencing those documents with this alleged breach, we may be much closer to determining the legitimacy of these claims.
The file names make specific, pointed, and very real-looking references to, for instance, previously unknown exploits against Cisco Adaptive Security Appliance Software, which is designed to protect corporate networks and data centers. Cisco did not respond to a request for comment by press time.
“Most of the dump contains Firewall exploits,” Suiche explained.
https://twitter.com/msuiche/status/765184743029825536
Despite initial skepticism about Shadow Brokers’ enormous claim, the proof files seem to be winning experts over to at least the possibility that this theft and auction is the real deal. There remains no definitive proof.
Unlike other some hackers, such as self-proclaimed DNC hacker Guccifer 2.0, the Shadow Brokers remained quiet after their initial social media burst. There’s no telling if that silence that will last.
The Bitcoin auction, which may end up garnering a lot of talk in the coming days, is a particularly strange aspect of this unfolding story.
If it were real, the Shadow Brokers could use, for instance, multisignature transactions and a trusted escrow to hold the money. Instead, they’re asking bidders to blindly throw money at them and hope it’s not rigged and scammed. The whole auction is widely being dismissed as a ruse or distraction.
What’s being paid more respect is the alleged hack and theft itself. No one is quite sure yet if this if this is an extremely elaborate fake or a real hack and (albeit small) leak of cyberweapons from the most potent cyberwar-fighting machine ever unleashed online, the NSA.
The breach may be as much as a few years old based on the code names it references.
https://twitter.com/DAlperovitch/status/765213022398783488
Regardless, that would still send a crystal clear message to America’s hackers: We can beat you and break you, too.
The NSA has not responded to a request for comment.