Working from home, chatting with a coworker over lunch, or chasing a thief who steals your phone: These are normal-people things, not traitor things, right? But wait, watch out! If you work for the Department of Defense, lots of everyday activities could be potential aids to the enemy in the war on cybercrime.
And that’s just the start of the list of things that can “give points to the adversary,” according to the Cyber Security Awareness Challenge.
The online game, which walks you through a list of security protocols as though it were your first day on the job, is the “unclassified” version released for DOD and general federal employees by the Defense Information Systems Agency. Launched in October of 2012 as part of Cybersecurity Awareness Month, the game quizzes you on how well you understand security protocols and regulations, ranging from tips on creating secure passwords to a list of the kinds of information considered “classified.”
The quiz grants you trophies for nothing less than correct answers to every question in each section. And if you get anything wrong, congrats—you’ve just aided and abetted the enemy.
But the real message of the challenge is plainly, “We’re not here to make friends.” Throughout your simulated work day at the DOD, you’re encouraged to rebuff friendly coworkers, be unkind to strangers, and rat on fellow employees.
At one point, you’re reprimanded if you try to chat with your coworker over lunch—talking about work outside of work is a little like Fight Club in DOD-land. Forget music-sharing, downloading, or playing Bejeweled on your down time. Even taking home a work laptop is out unless it’s been specially cleared by the omniscient eye of Security.
And when that WikiLeaks reporter calls? Forget it. You’re an official spokesperson for the government, and you can neither confirm or deny.
By the time the guy wanting to use your smartphone to check his email gives you a disgusted look after you say no, you’ve realized that he speaks for everyone around you. Man, you’re a jerk.
Fortunately, your new dose of low self-esteem comes just at the moment you’re identifying “Insider Threats”—namely, people you work with who could pose security risks. The Threats are people who are more likely to take confidential information and do something criminal with it. Risk factors, according to the DOD, are things like hot tempers, sudden financial windfalls, and open dissatisfaction with the government.
Oh, yeah, and depression and antisocial behavior. Thanks for that extra kick in the nads, DOD!
The simulation asks you to judge and rate each of your coworkers for their potential number of risk factors. One, an Indian-American named “Hema,” is dubbed a high threat because she returns to India every six months to visit her parents. This is true for Hema even though most U.S. travel visas only allow students and workers to stay in the country for six months at a time.
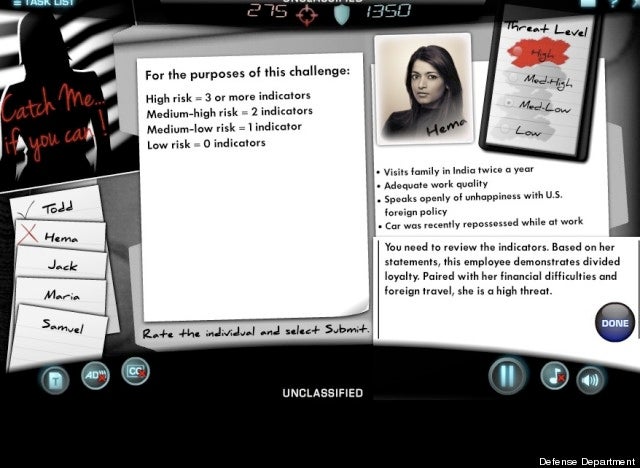
Screengrab via Information Assurance Support Environment
Meanwhile, other sections of the quiz seem to deny any understanding of how most humans work. One forces you to delete only information from your Facebook page that can’t be used to gain access to your identity by cybercriminals. But don’t try to delete your silly-sounding email from the site, or you’ll give points to the other side.
And if you try to click on even normal website links from harmless-enough places like a discussion forum on a government website, too bad—you’ve just handed points to the enemy. Are any links on the Internet safe to click on? Probably, but you should check with security first, just to be safe.
At other turns during the game, you’re expected to report your supervisors to security when they fail to follow proper protocol procedures themselves.
Contacting security is the answer to everything from getting weird phone calls to having your phone stolen. But wait, aren’t you and you boss supposed to be security? Who watches the watchmen in this game?
The “adversaries,” apparently.
If you don’t want to sit through the extended game, you can take a different, brief quiz with many of the same concepts at the Pennsylvania state cybersecurity website.
Just remember: Screw up, and the terrorists win.
Screengrab via Information Assurance Support Environment


