Facebook exposes significant amounts of your personal data, including status updates, photos, location data, and work history, to anyone who knows your phone number.
Reza Moaiandin, technical director at U.K.-based SEO firm Salt Agency, discovered what he calls a “security loophole” on Facebook that allowed him to collect public data on American, British, and Canadian users by running an anonymized database of phone numbers through a Facebook API.
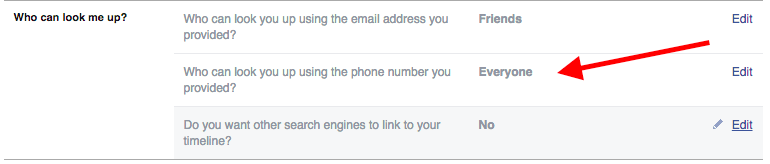
That data was accessible because Facebook’s “Who can look me up?” setting, which determines who can find you using your phone number, is set to “Everyone” by default. Unless you change that setting, if someone found your phone number anywhere on the Internet, they could see certain aspects of your profile even if they had no connection to you.
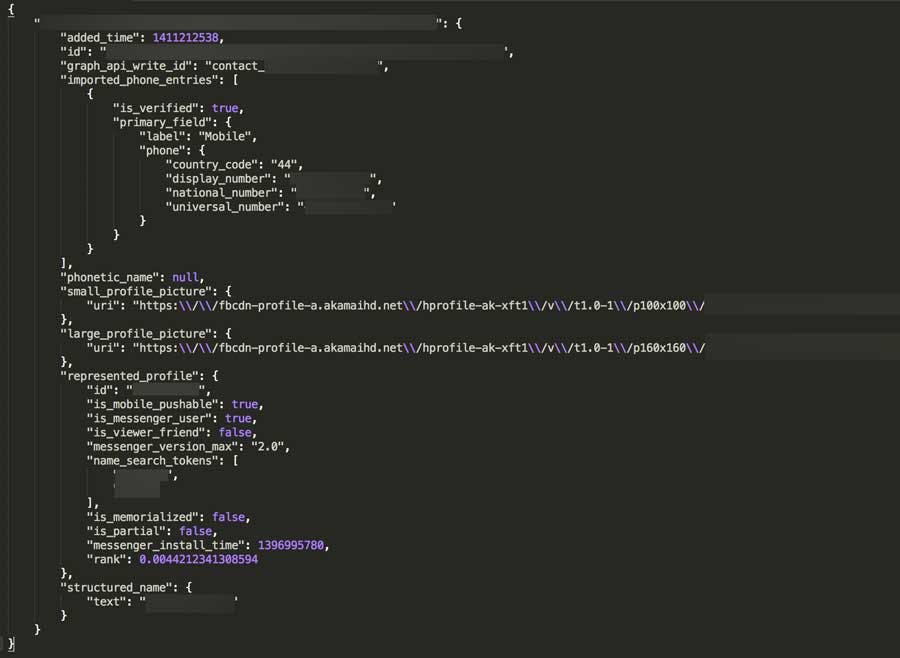
Moaiandin used a script that produced thousands of random phone number combinations from three different countries and then sent those numbers to Facebook’s GraphQL. If a phone number was linked to a Facebook account with the default privacy setting, Moaiandin’s program spit out personal public data about that person.
So why does this matter if the data is already public?
“A person with the right knowledge can harvest the non-private details of the users who allow public access to their phone numbers, enabling the harvester to then use or sell on the user details for purposes that the user may not be happy with,” Moaiandin explained in an email with the Daily Dot.
Data harvesters can sell personal information they’ve scraped from social and e-commerce sites, either for fake Likes on social media or for more nefarious purposes like identity theft.
Facebook, for its part, does not consider this discovery to be a bug. Moaiandin said that he reached out to Facebook twice before the company said “we do not consider it a security vulnerability” because all the data collected is public.
Facebook also said that it does have controls in place to monitor API abuse, including rate throttling, which would limit the requests from one user. Moaiandin, however, didn’t hit that rate limit, and he said that it’s possible to get around such restrictions by creating multiple fake accounts.
Facebook would not tell the Daily Dot what its rate limits are, and the developer documentation doesn’t list precise limits either. It does explain that there are three different types of throttling for Graph API calls. Theoretically, this would help to prevent the kind of mass collection of data that Moaiandin described.
Facebook is not worried about this so-called loophole. A spokesperson sent the following statement to the Daily Dot.
The privacy of people who use Facebook is extremely important to us. We have strict rules that govern how developers may use our APIs to build their products, and in this instance all the information being returned is already designated to be Public.
Everyone who uses Facebook has control of the information they share, including information on their profile and who can look them up by phone number. Our Privacy Basics tool has a series of helpful guides that explain how people can quickly and easily decide what information they share and with whom they want to share it.
Although this information is public already, this technical workaround makes it easy for people to collect data en masse. It’s a tricky balance, however, because Facebook needs to provide public data to developers so that users can access things like apps and other services built using the company’s APIs.
Moaiandin explained how Facebook could further secure the data he found to prevent copycats with more sinister motivations.
“Facebook should pre-encrypt its private API communications so its [sic] more difficult to find these security loopholes and potentially look into strengthening their API rate limits and security algorithms,” he said.
To avoid winding up in a data dump like this one, you can go to your Facebook privacy settings and change the privacy setting that allows people to search for you by phone number from “Everyone” to “Friends.”
While Facebook might not be concerned with Moaiandin’s discovery, the potential data grab illustrates once again how crucial it is to be aware of your privacy settings.
If you haven’t taken a look at your settings recently, now might be a good time to do a privacy checkup. Make sure that the only material you’re sharing publicly is information you’d be comfortable seeing on a list of Facebook users.
H/T The Guardian | Illustration by Max Fleishman