It took about eight months for Slack to grow from nothing into a billion dollar company. But is the rise of group-chat apps putting organizations at risk?
At its core, Slack allows individuals and organizations to create a litany of chat rooms to collaborate on projects and post animated GIFs. For companies that had spent previous decades inundated with email, Slack felt like a liberating glimpse into the future of enterprise communication.
However, SpiderOak President Mike McCamon can’t help but see a giant fly in Slack’s ointment. “The informality of communication on collaboration tools is terrifying,” McCamon said. “Even young people today know that when you type an email, you need to think about what you put in an email because that lives forever. But they don’t think about chat like that. It’s going to be a goldmine [for lawsuits and blackmailers].”
McCamon knows a thing of two about cybersecurity. For over a decade, SpiderOak has been building encrypted communication products for anyone paranoid enough to think that someone might be spying on their communications. In 2014, former NSA contractor and international man of mystery Edward Snowden urged people to stop using Dropbox and switch to SpiderOak’s cloud storage system instead.
McCamon points to what happened after the hack at the Democratic National Committee as a worst-case scenario revealing how collaboration platforms like Slack could create major liabilities for organizations.
While the intrusion method used by attackers to gain access to the DNC‘s computer systems are unknown—or, at least, haven’t been revealed to the public—it’s likely that someone with access to the DNC’s systems was targeted in a spear-phishing attack, which is when a user is tricked into clicking on a link or downloading an attachment that downloads malware onto their computer. That malware is then used to take control of the user’s device and gain access to the online systems to which that users had access.
“The informality of communication on collaboration tools is terrifying.”
In the case of the DNC, the politically motivated attacker—a hacker going by the name Guccifer 2.0, who steadfastly insists he has no connection to the Russian government—targeted the party’s email system and continues to release a trove of embarrassing internal emails to the public that resulted in the resignation of much of the DNC’s senior leadership.
For readers who use both regularly use both email and collaboration tools like Slack, think about the different types of conversations you have on each platform. If an attacker looking to inflict maximum damage to your reputation had access to each one, which would provide more potent material?
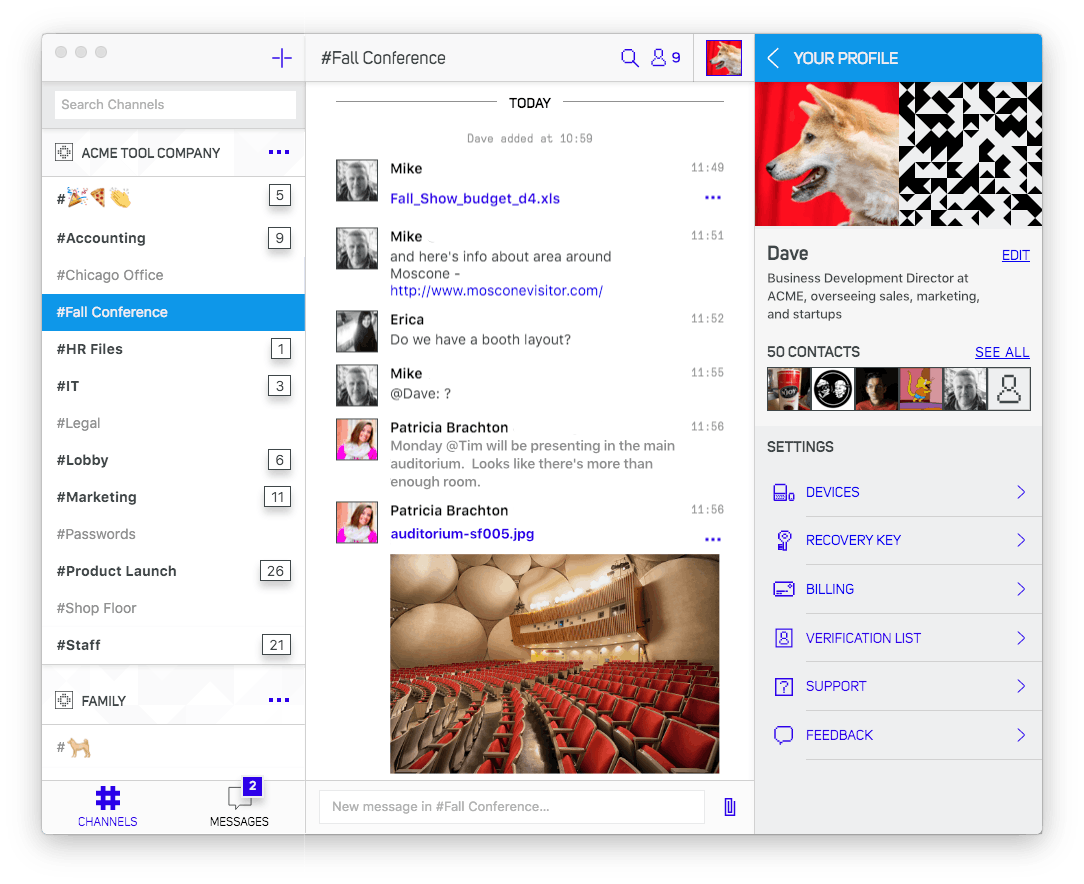
SpiderOak is based in Kansas City, Missouri, but the majority of its employees are scattered across the globe. They saw how a collaboration tool like Slack could make their lives easier, but, as people who build cybersecurity products for a living, they couldn’t help but be worried about the implications of moving to Slack. McCamon’s team at SpiderOak created Semaphor to solve that very problem: how to get the functionality of Slack while doing everything possible to keep hackers out.
Launched a few weeks ago, Semaphor has about 5,000 users. McCamon realized that if SpiderOak had this need, there would certainly be other organizations that want something similar to Slack except built from the ground up with the philosophy of minimizing every possible avenue though which data could leak.
The idea at the core of Semaphor is maximizing the efficacy of encryption, the process of scrambling the contents of a message using a complex algorithm so that only the intended recipient is able to unscramble and read it.
“We want minimize attack vectors,” he said. “Our engineering team looks at this like, ‘how do we build a tool that lets me have the same experience I would have if I were in a room in person?’ There’s no way that information can leak. It’s only the people in the room that know what’s happening. It’s like having a meeting in person but allow me to do it online.”
Every Semaphor channel is encrypted independently from all the others, and that encryption happens on each user’s local device. This practice ensures that users are only able to access the contents of the channels to which they’ve been invited. If your organization has 20 Semaphor channels, but you’re only privy to five, an attacker who compromises your system with malware will be locked out of the other 15.
“It’s only the conversations that you’ve been having,” McCamon explains. “It’s nothing else in the organization. There are no keys to the kingdom that let you get in and get everything.”
The flip-side of the encryption coin, according McCamon, is identity. Not only does the conversation itself need to be secure, but the people on either side need to be confident they’re actually talking to the person they think they’re talking to. To that end, SpiderOak is working on building a “web of trust” into the platform.
This verification system, which is still in the development phase, will work like this: Every Semaphor user has a QR code on his or her mobile device. When two users meet face-to-face, they can scan QR codes, thereby verifying each others’ identities. “The idea is that over time we’re going to build ways into the interface to see who has high verification and who has low verification,” McCamon said. “It will create anxiety when people interact with other people that have low verification.”
That peer-to-peer verification happens entirely within the Semaphor app, which is a standard feature. Semaphor is built to be as much of an entirely self-contained ecosystem as possible, because, every time the app passes a function off to a third-party, it creates a potential vulnerability. For example, Semaphor discourages sending channel invites through email—instead advising enterprise customers to set up a internal, password-protected web page that contains a link allowing a user to join a channel. That way, the danger posed by a compromised email account is significantly reduced.
This devotion to security does have drawbacks. There’s no version of Semaphor that can run in a user’s web browser—a feature found in competing services like Slack and Hipchat that makes signing in from someone else’s device much easier. If someone wants to use the program, they’re going to have to download it on their device.
Semaphor also doesn’t really have the ability to do third-party integrations. One of the coolest things about Slack is that it can run applications inside of its platform. Simply type “/giphy puppies” into Slack’s command line and Giphy will bring in a randomly selected animated GIF of puppies right into your chatroom.
“We don’t do that and here’s why: It creates information leakage,” says McCamon, who noted that Semaphor does support animated GIFs (but they have to be posted into a channel by a user directly). “Our servers don’t know that that’s a link [because the whole channel is encrypted], so we can’t go download it for you and then package it up to deliver to you, because we’d have to be able to read your messages to see that. Which means that every time Slack is doing that, there’s something that’s reading those message. It reads the URL and then pulls that metadata, that’s how that works.”
Just like Semaphor keeps access to channels on a need-to-know basis, SpiderOak does the same thing internally. All of the conversations that occur on Semaphor are encrypted with keys the company has no access to. If an attacker were to gain access to every corner of SpiderOak’s corporate systems, it wouldn’t let them read the conversations of the firm’s customers. Similarly, if a law enforcement agency were to order SpiderOak to turn over customer conversations, all the company would be able to provide is garbled gibberish.
The legal battle over Gawker’s decision to publish a sex tape that featured former professional wrestler Hulk Hogan reveals the types of scenarios in which internal communications can be made public. Gawker Executive Editor John Cook was forced to take the stand and defend a series of crude jokes Gawker employees made about Hogan’s penis on their internal work chat years earlier.
It did not seem like a pleasant experience.
Attorney: Would you characterize this as making jokes about Mr. Hogan?
— Anna Phillips (@annamphillips) March 8, 2016
Cook: I would characterize it as workplace humor. #hulkvsgawk
Cook is now having to explain why he posted a picture of an uncircumcised penis in the workplace chat threat. Oy. #HulkVsGawk stream
— Anna Phillips (@annamphillips) March 8, 2016
Semaphor allows administrators of each channel to set retention policies. If an admin doesn’t want conversations more than three months old to be accessible, Semaphor will automatically encrypt conversations after 90 days and then shred the decryption key. If Gawker had been using Semaphor and turned on that feature, Cook’s joke about the little Hulkster would have been lost to history rather than a matter of public record.
Slack, which did not respond to a request for comment, does have a similar data retention feature, and it’s something that everyone using collaboration tools should think about turning on.
“Any electronic records that are relevant to a particular claim are discoverable in civil cases in the United States,” Dori Hanswirth, the head of the media litigation practice at Hogan Lovells told Bloomberg earlier this year. “There is no, ‘well, I was just being funny with my friendly co-workers’’ exemption to what would be discovered. If it’s out there … there’s a chance that it will end up in the hands of some legal adversary of your company. There is no protection against it.”
Slack’s sudden ubiquity should give a lot of organization pause. It’s certainly a useful tool, but like any other digital technology, it comes with risks. With Semaphor, SpiderOak believes there’s room in in the market for another option that goes out of its way to minimize those risks. The question is: Are those security risks big enough for people to make to switch?
Correction: A previous version of this article incorrectly identified Mike McCamon as SpiderOak’s CEO. He is the company’s president.
Contact the author: Aaron Sankin, asankin@dailydot.com