Where should you get your Mac applications from? The Mac App Store, most people will respond, where Apple thoroughly examines every program for security and privacy issues before publishing it.
And to be fair, the App Store is probably the most secure place to find applications for your Mac. But “most secure” doesn’t mean “absolutely secure.”
According to the findings of security researchers at Malwarebytes and Digita Security, several apps in the Mac App Store are spying on users, and at least one of them has made the top-ten charts, meaning it has probably been downloaded millions of times.
Adware Doctor
According to a blog post by Malwarebytes Labs, researchers have found several apps that were manifesting malicious behavior, collecting sensitive user information such as browsing history and the list of downloaded software, and are sending them to servers controlled by the developer. Some of these apps are sending their data to servers in China, where privacy and security rules are not as strict as in the U.S. and Europe.
Adware Doctor, the most popular of the malicious apps found, was at some point the fourth most popular paid app in the App Store. Ostensibly, it introduces itself as the best app to remove a variety of common adware. But while the app is running, it collects browsing history from Safari, Firefox, and Chrome, as well as a list of all running processes and the software you have downloaded.
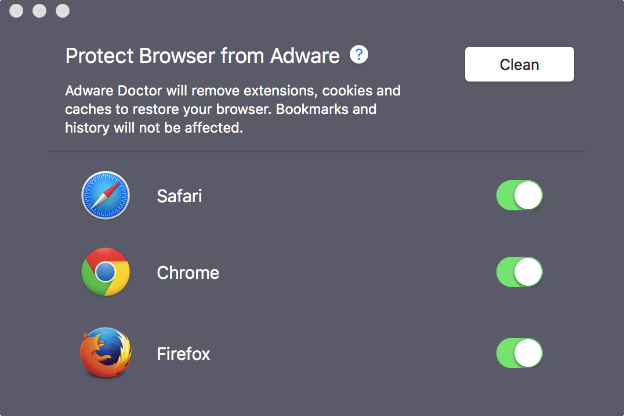
Adware Doctor then compresses the data into a zip file and sends it to a server in China. The malicious behavior of Adware Doctor was first discovered by independent researcher Privacy 1st and later confirmed by security researchers Patrick Wardle of Digita Security and Thomas Reed of Malwarebytes.
Malwarebytes has been investigating Yongming Zhang, the developer of Adware Doctor, for several years. In 2015, Zhang released the first version of his app, then-called Adware Medic, which Malwarebytes’ Reed quickly detected and reported to Apple. Adware Medic was removed, but soon after Adware Doctor was published.
“We’ve continued to fight against this app, as well as others made by the same developer, and it has been taken down several times now, but in a continued failure of Apple’s review process, is always replaced by a new version before long,” Reed writes.
A trend of malicious apps
Adware Doctor is not the only Mac App Store item to spy on users. Reed lists a number of applications he has been tracking, which aren’t as popular as Adware Doctor but no less malicious.
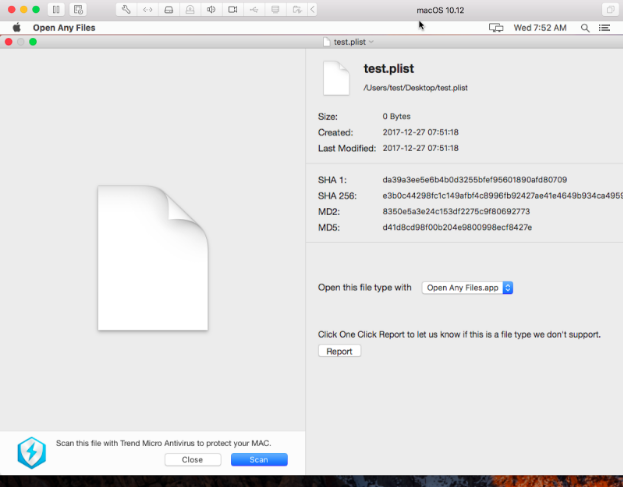
Open Any File, one of the applications Reed reports about, claims to be an app that can open any file that the user doesn’t have a proper app for. In the background, however, the app collects the user’s Chrome, Safari, Firefox, and App Store browsing and search history, packs it into a zip file and sends it to a server that belongs to Trend Micro, a security company.
Reed reported the app to Apple in December 2017, but it is still present on the App Store. “Recently, Open Any Files stopped exfiltrating this data, but we have retained the evidence from our observations,” he says.
Dr. Antivirus and Dr. Cleaner, two other utility applications currently in the App Store, collected the same browsing history data as Open Any Files. Dr. Antivirus also collected a list of all applications installed on the user’s Mac.
“It could be argued that it is useful for antivirus software to collect certain limited browsing history leading up to a malware/webpage detection and blocking. But it is very hard to argue to exfiltrate the entire browsing history of all installed browsers regardless of whether the user has encountered malware or not,” Reed says.
A violation of Apple’s developer guidelines
The Mac App Store imposes restrictions on how apps can access the filesystem and require developers to request permission from users before accessing their files. But since the developers have hidden their malicious behavior behind utility applications, it’s easy for users to be tricked into granting permission, especially since they’ve downloaded the apps from the App Store, which implies they should be trustable.
“All of these apps [get user approval before they can access the broader file system], so this is not technically a sandbox bypass,” says Reed, referring to the MacOS feature that prevents applications from accessing data other than their own. “They ask for permission to access the user’s home folder, and if the user gives it, they have legitimate access to those files.”
However, what they’re doing with that access is definitely not within the spirit of why they asked for the permission, he adds.
And a clunky bug reporting system
Reed has been tracking and reporting malicious software in the Mac App Store for years, and he believes that Mac App Store’s issue tracking system really needs to improve. “The biggest problem is that there is no method I’m aware of for reporting these kinds of issues to the App Store team. I’ve reported issues to product security, but that’s technically a different team,” Reed says.
Reed has also reported the found issues using the reportaproblem.apple.com, the portal where users file problems with their purchases from iTunes and the iOS and Mac App Stores. But that too has yielded no result.
“The worst problem has actually been with Adware Doctor. That app has been on my radar for nearly three years. We’ve reported it to Apple several times, and although it’s been removed at least once (when we reported it for trademark infringement over its previous name, Adware Medic), it’s still in the store today,” Reed says.
The Daily Dot reached out to Apple for comments, but haven’t received a reply at the time of this writing. Shortly after Reed and Wardle published their reports, Apple removed Adware Doctor from the Mac App Store.
Why you should be more vigilant in using the App Store
“Unfortunately no,” Reed said when we asked him if there was any way users could identify malicious behavior similar to what was found in Adware Doctor and the other apps.
“One would be hard-pressed to know these apps were doing anything wrong without having the skills to analyze the behavior of the apps. It’s especially difficult when an app has a large number of positive ratings. The average user has no way to know that many of those are fake.”
While the Mac App Store still remains the most secure place for downloading apps, it “is not the safe haven of reputable software that Apple wants it to be,” in Reed’s words. This means you should still be wary of the apps you purchase and the permissions you give those apps, and possibly do a little web research about any known issues.
“I strongly encourage you to treat the App Store just like you would any other download location: as potentially dangerous,” Reed says. “Be cautious of what you download. A free app from the App Store may seem perfectly innocent and harmless, but if you have to give that app access to any of your data as part of its expected functionality, you can’t know how it will use that data.”


