After reporter Glenn Greenwald, who worked with former National Security Agency contractor Edward Snowden to reveal the details of various U.S. surveillance programs, left the Guardian last year to start his own publication, news junkies and privacy advocates following the Snowden saga weren’t sure what to expect.
Now we know what Greenwald’s been up to.
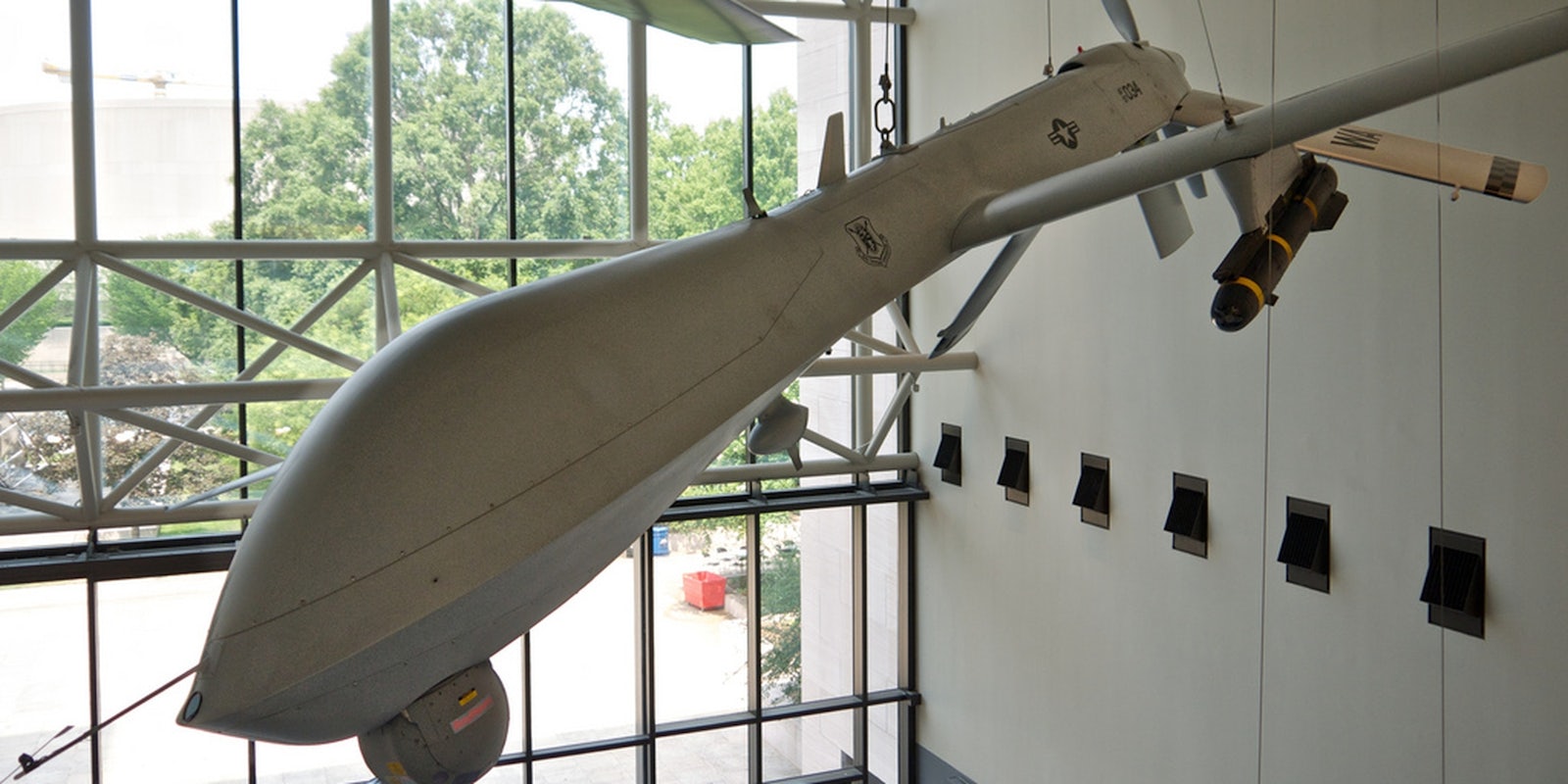
New details have emerged about the NSA’s involvement in unmanned combat drones committed to the assassination of terrorism targets abroad. The story was published as the premiere article of the Intercept, a publication founded by First Look Media and dedicated to Snowden’s leaked materials.
Citing top-secret NSA documents and statements by former military personnel, the Intercept revealed the Central Intelligence Agency (CIA) and U.S. military’s ever-increasing reliance on NSA metadata collection to justify drone strikes.
What’s more, a former member of the Joint Special Operations Command (JSOC), charged with “identifying, capturing, or killing terrorist suspects,” told the Intercept that relying on the NSA’s intelligence was “absolutely” responsible for the deaths of innocent people. The source, who previously operated drones for the U.S. military, spoke to journalists on the condition of anonymity.
The source also claimed an NSA tracking program called “Geo Cell” identifies targets based on the location of mobile devices and SIM cards. “Once the bomb lands or a night raid happens, you know that phone is there. But we don’t know who’s behind it, who’s holding it,” the source said, implying the technology is only reliable for tracking the location of a phone, not the person holding onto it. He estimated that 90 percent of the intelligence used to justify drone strikes originated with NSA phone-tracking technology.
The former drone operator also admitted to taking part in strikes when the target was identified, but others killed by the strike were unknown. The victims of so-called “collateral damage” might have been terrorists, “or they could have been family members who have nothing to do with the target’s activities.”
Drones equipped with special NSA geolocation systems, code name GILGAMESH, locate SIM cards or devices the U.S. Military believes are in the possession of terrorist suspects. They can then track devices to within 30 feet of their actual location, NSA documents reveal. An anonymous source claims the majority of metadata errors resulting from this collection process have occurred in Pakistan, Yemen, and Somalia, where U.S. forces have fewer intelligence sources on the ground.
The CIA used a similar system, code-named SHENANIGANS, to map the Wi-Fi networks of every major town in Yemen, according to an operator quoted in classified documents. The operation, which was previously undisclosed, “utilizes a pod on aircraft that vacuums up massive amounts of data from any wireless routers, computers, smartphones, or other electronic devices that are within range.”
The increasing number of civilian deaths from drone strikes may be attributed to the evolving tactics of terrorist targets who are attempting to dodge surveillance. Brandon Bryant, another former drone operator, told the Intercept that targets were switching phones, or placing used SIM cards in other devices. Bryant left the the Air Force in 2011 and has since been an outspoken critic of U.S. drone operations.
White House authorization required to target a terrorist suspect with a drone strike remains active for only 60 days before requiring a review. In order for a strike to take place, CIA and U.S. military operators must have at least two sources of intelligence to corroborate the location of the authorized target. The anonymous source claims this situation places increased pressure on commanders to engage targets, even when a high risk of civilian deaths is involved.
Another top secret NSA document sheds light on the agency’s role in the 2011 drone strike that killed U.S. citizens Samir Khan, Anwar al-Awlaki, and Awlaki’s 16-year-old son, Abdulrahman.
The extrajudicial assassination of American citizens has been controversial for President Obama. However, the White House has refused to comment on the decision to launch a drone strike against Abdulrahman, who was believed to be searching for his father, not engaged in terrorist activities.
Greenwald, who was originally chosen by Snowden to receive the documents, collaborated with journalist Jeremy Scahill on the release.
In April 2013, Scahill published a book, which later became a documentary, titled Dirty Wars: The World Is a Battlefield, in which he detailed the U.S. government cover-up of five civilian deaths, including three women, during an American special operation in Afghanistan known as the Khataba raid. Much of Scahill’s work has focused on the Obama administration’s Assassination Program, as well as JSOC.
“Whether or not Obama is fully aware of the errors built into the program of targeted assassination, he and his top advisors have repeatedly made clear that the president himself directly oversees the drone operation and takes full responsibility for it,” Scahill and Greenwald concluded.
The Intercept’s debut article, like Scahill’s Dirty Wars, paints the U.S. drone program as taking an arbitrary approach to the targeting of noncombatants in the global war on terror—the cost of which are the faceless remains of untold, perhaps blameless, victims.
H/T The Intercept | Photo via Don DeBold/Flickr