Americans were aghast to learn on June 5 that the National Security Agency (NSA) was tracking every phone call made on every major carrier in the country. What’s more shocking, though, is that the agency has been able to keep that practice alive for almost a dozen years.
Just a month after the attacks of Sept. 11, 2001, the NSA began compiling vast amounts of Americans’ metadata—timestamps and records of who called, texted, or emailed whom.
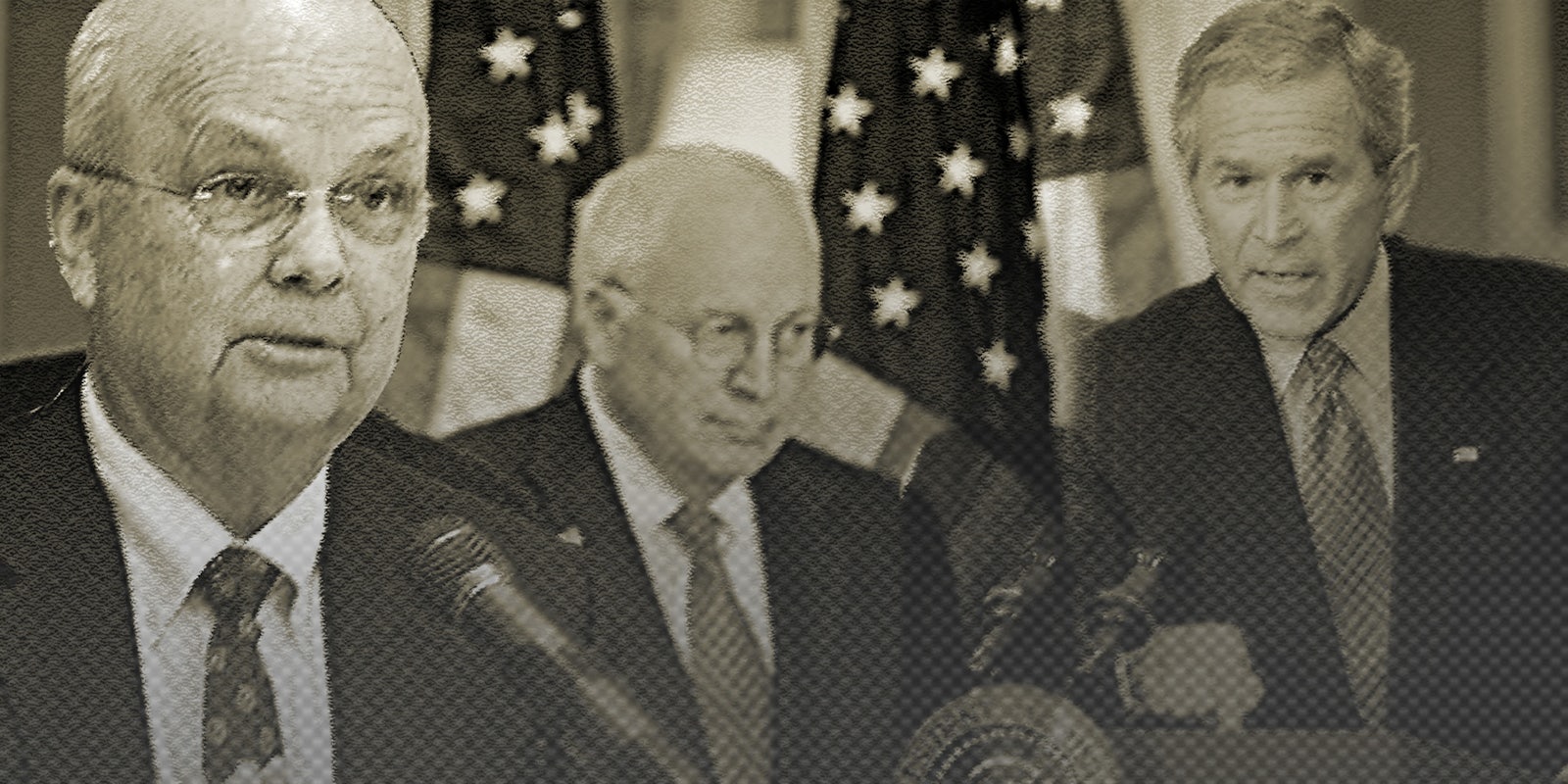
That’s according to a candid NSA memo, written in 2009, that was leaked by the Guardian on June 27. Presumably, it’s part of the massive trove of such documents whistleblower Edward Snowden passed to the paper. It’s marked Top Secret and comes from the desk of the NSA’s Office of the Inspector General. It provides a fascinating, explicit timeline for how the agency’s leader, then-Director General Michael Hayden, got rapid legal authorization, with little oversight, for the NSA to broaden its abilities. Unlike the NSA’s stilted public statements, the memo is written clearly and linearly, almost as a narrative.
According to the memo, it took just three days after the terrorist attacks of September 11 for the NSA to get involved. On September 14, Gen. Hayden, at the time director of the NSA, approved an order for U.S. intelligence agencies to target phone numbers that came from countries associated with terrorism. Only specific, approved numbers could be tracked for calls that came from the U.S., but there appeared to be no such restrictions on calls to the country.
The NSA’s General Council deemed Hayden’s actions to be legal in accordance with Executive Order 12333, passed by President Ronald Reagan in 1981, which broadened scope of the NSA’s powers and responsibilities.
Twelve days later, on Sept. 26, 2012, Hayden declared that any call between Afghanistan and the U.S. was “presumed to be of foreign intelligence value” and could be sent to the FBI. The NSA memo says, bluntly, that Hayden was “aggressive” in his reading of the order:
“[T]he targeting of communication links with one end in the United States was a more aggressive use of E.O. 12333 authority than that exercised by former Directors. General Hayden was operating in a unique environment in which it was a widely held belief that additional terrorist attacks on U.S. soil were imminent.”
However, on Oct. 2, Hayden told the House Intelligence Committee about this plan to start exploiting Reagan’s executive order. He also told his boss, CIA Director George Tenet, who oversaw all U.S. intelligence agencies acted as a liaison between Hayden and Vice President Dick Cheney. According to the memo:
“Mr. Tenet relayed that the Vice President wanted to know if NSA could be doing more. General Hayden replied that nothing else could be done within existing NSA authorities.”
So Hayden began focusing in on a specific role for the NSA to play: Tracking communications between the U.S. and the rest of the world. The memo quotes an unnamed technical director explaining the agency’s thinking:
“Here is NSA standing at the U.S. border looking outward for foreign threats. There is the FBI looking within the United States for domestic threats. But no one was looking at the foreign threats coming into the United States. That was a huge gap that NSA wanted to cover.”
The NSA aimed to use the Foreign Intelligence Surveillance Act (FISA), created to track foreign powers, was authored in 1978, and signed into law by President Jimmy Carter. Being written so long ago, FISA didn’t explicitly authorize anyone to track Internet communications.
The NSA determined that FISA “did not allow sufficient flexibility to counter the new terrorist threat,” noting that the language of the law would require them “to obtain court orders to target email accounts used by non-U.S. persons outside the United States.”
The agency decided that such a process—going to a court for each target—didn’t allow the agency to track terrorists at a reasonable speed and that even getting emergency orders wouldn’t be sufficient.
They needed another way.
…
Sometime before October 2001—the memo doesn’t provide specific dates here—Hayden began talks with White House officials. He wanted to know how he could start getting Americans’ communications—whether actual content or metadata (meaning the details of communications but not their content)—without a court order. It was Hayden, according to the memo, who suggested to Cheney that:
“[C]ommunications metadata did not have the same level of constitutional protection as content and that access to metadata of communications with one end in the United States would significantly enhance NSA’s analytic capabilities.”
On Oct.4, President Bush signed his first of many authorizations for the NSA to, without a warrant or court order, search the content of any international target’s phone and Internet communications, as well as related metadata. It lasted for a 30-day period and gave broad parameters for whom the NSA could target: Not only was the NSA authorized to track anyone it thought was in Afghanistan or was preparing for an act of terrorism, but also any communications between two non-U.S. citizens, as long as both parties weren’t within U.S. borders.
Why a secret authorization? The House Intelligence Committee proposed amending FISA to the NSA’s request. The NSA wrote to Bush’s counsel asking if they could negotiate an emergency bill, but there’s no record of a response.
There is, however, this admission by the NSA: “Anecdotal evidence suggests that government officials feared the public debate surrounding any changes to FISA would compromise intelligence sources and methods.”
…
Bush’s authorization opened Pandora’s box.
On Friday, Oct. 5, Hayden took “immediate steps” to implement it. That meant creating a 24-hour Metadata Analysis Center (MAC), complete with 50 servers and a $25 million operating budget
Over the weekend, the NSA called a group of about 90 personnel to report to work. On Monday, Hayden told those operatives a few select details about their new mission. They knew it came from the president, that it was a temporary job, and that they would create an early warning system to prevent terrorism. They would do what Bush’s authorization allowed, Hayden told them, “and not electron or photon more.”
Hayden later said he never actually asked the NSA counsel for help in interpreting Bush’s order, as he thought it was confidential legal advice to Bush. The NSA’s inspector general called that legal situation “odd,” adding it was “strange the NSA was told to execute a secret program that everyone knew presented legal questions, without being told the underpinning legal theory.”
It took 30 days for the MAC to become fully operational. Before the end of the month, American companies began sending their users’ communications to the agency. By November, after Bush’s second authorization, they were sending metadata, too.
…
By June of 2013, that process had become fully formalized. The Guardian released leaked documents that showed that every day, Verizon sends the metadata of phone calls to the NSA. The Washington Post followed up with the revelation that, at least since 2006, the agency has been getting that information from other phone companies, too. That’s thanks to FISA getting revamped in the PATRIOT Act to allow metadata collection from all American companies, including Bell South and AT&T.
Once they were public, President Obama admitted the U.S. engages in those practices and even defended them. He told Charlie Rose that if “you are a U.S. person, the NSA cannot listen to your telephone calls and the NSA cannot target your emails” without a warrant.
He continued:
“There are two programs that were revealed by Mr. Snowden—allegedly, since there’s a criminal investigation taking place and that caused all the ruckus. Program number one is called the 215 program. What that does is it gets data from the service providers—like a Verizon—in bulk. And basically you have call pairs. You have my telephone number connecting with your telephone number. There are no names, there’s no content in that database. All it is, is the number pairs, when those calls took place, how long they took place. So that database is sitting there.”
On Friday, Director of National Intelligence James Clapper admitted the metadata collection program has been renewed for another three months. “[T]he DNI has decided to declassify and disclose publicly that the Government filed an application with the Foreign Intelligence Surveillance Court seeking renewal of the authority to collect telephony metadata in bulk, and that the Court renewed that authority,” Clapper’s office announced.
Your telephone data is still, to this day, being collected. It’s just sitting there.
Photo via Wikimedia Commons, remix by Jason Reed