A security researcher recently demonstrated a vulnerability to malicious code in Apple Macs that he claims is both undetectable and irremovable.
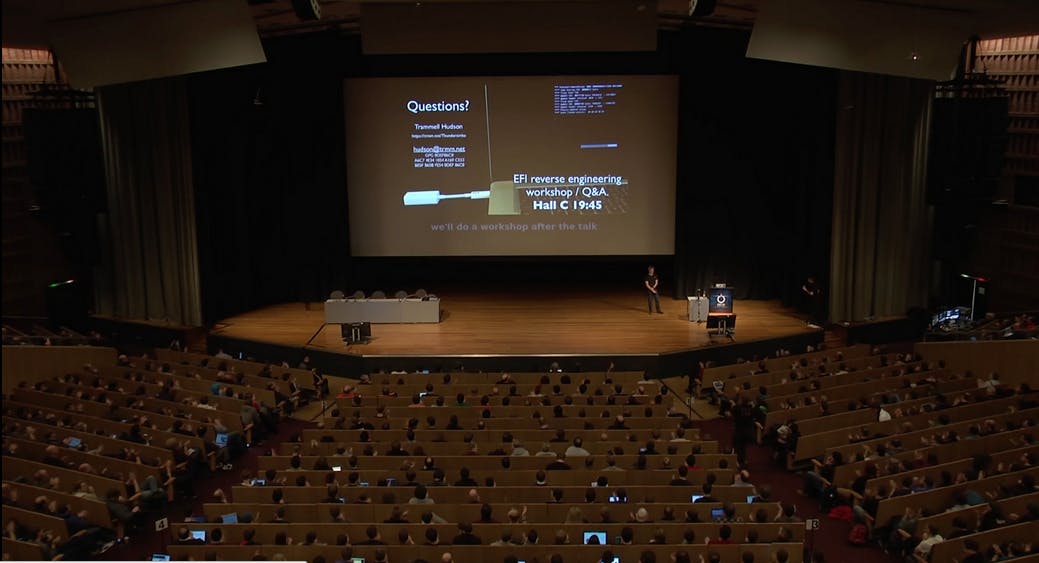
Trammell Hudson, who works for hedge fund Two Sigma Investments, announced his discovery during a presentation to the Chaos Computer Club (CCC), one of Europe’s largest associations of hackers.
Hudson later posted an annotated version of his presentation on his blog.
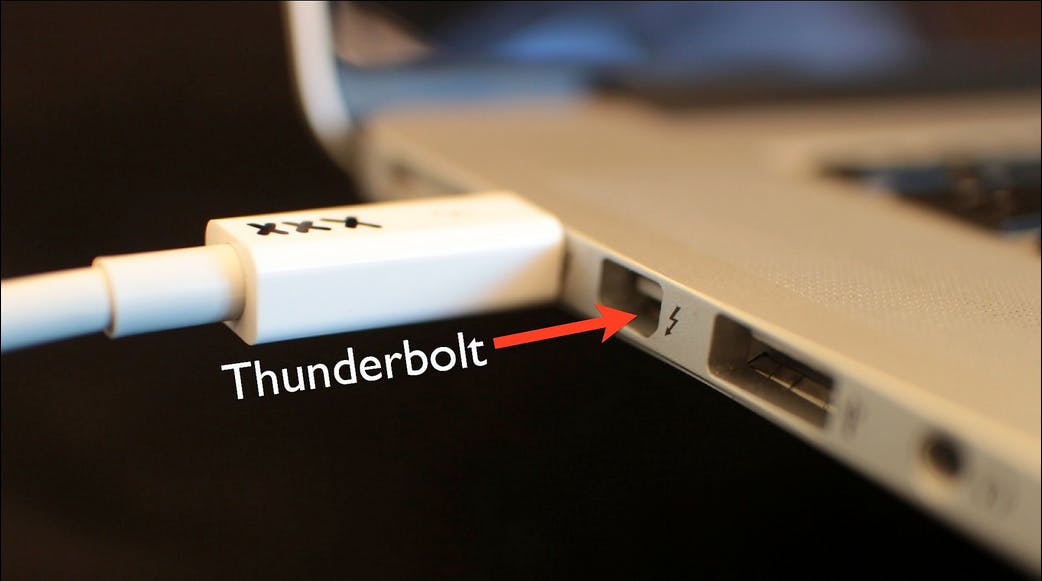
The hack, called “Thunderstrike” for its ability to be transmitted via the Thunderbolt port, installs malicious code onto the Boot ROM of the system and cannot be removed, even by replacing the computer’s hard drive.
“Since it is the first OS X firmware bootkit, there is nothing currently scanning for its presence,” writes Trammell. “It controls the system from the very first instruction, which allows it to log keystrokes, including disk encryption keys … and bypass firmware passwords. It can’t be removed by software since it controls the signing keys and update routines. Reinstallation of OS X won’t remove it. Replacing the SSD won’t remove it since there is nothing stored on the drive.”
Hudson notes on his blog that he first discovered the problem when his employer was considering the use of MacBooks. The employer asked Hudson to use his reverse-engineering background to investigate security concerns it had with the Apple product.
Hudson’s first step was dismantling the laptop in order to gain access to the boot ROM, a tiny chip that contains the code necessary to get a computer running when first turned on. Once he had gained access to the boot ROM, Hudson loaded it with malicious code, in what is known as a bootkit attack. He was then able to circumvent checks that would normally render such an attack unsuccessful.
Even more damaging, Hudson later found that disassembly of the laptop was not required for transmission of the virus. Instead, he writes, any Thunderbolt-compatible device can be used as a delivery mechanism by following a few simple steps:
“Given a few minutes alone with your laptop, Thunderstrike allows the boot ROM firmware to be replaced, regardless of firmware passwords or disk encryption. Thunderstrike in its current form has been effective against every MacBook Pro/Air/Retina with Thunderbolt that I’ve tested, which is most models since 2011.”
Hudson claims that he first approached Apple about the problem in 2013 and that the company is now almost ready to introduce a “partial fix” that could prevent some instances of modification to the boot ROM, but not all. This patch would only prevent certain forms of attack by Thunderbolt port and would not protect a computer from the longer, physical dismantling method initially tested by Hudson.
For now, Hudson recommends a combination of hi- and low-tech approaches to preventing someone from carrying out the attack on your computer.
First, he recommends writing over the ROM with your own code to disable remote hacks via Thunderbolt—something 99.9 percent of us are likely to consider laughably complicated. Here’s Hudson’s MacGyver-esque (and quasi-conspiratorial) suggestion for preventing physical access to your computer’s insides: Just paint the screws on your case over with glittery nail polish and take pictures of the unique pattern left in the seal. This way you can tell if your laptop has been tampered with.
H/T The Telegraph | Photos via trmm.net