Hackers have a new hands-off approach to stealing money out of ATMs.
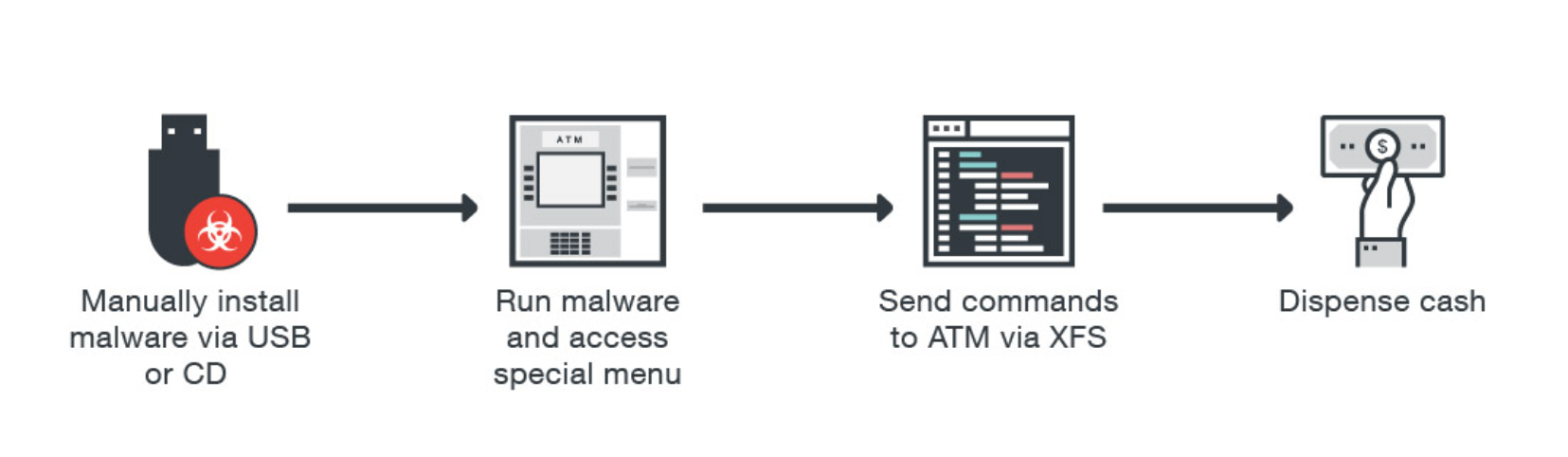
A report from Trends Micro says there is a shift in the ATM malware landscape from attacks that require physical instruments to network-based approaches. Instead of using skimmers, USB-ports, or CD drives to infect a machine, hackers are now infiltrating a bank’s internal networks to gain access to ATM funds.
The steps in these attacks aren’t unlike the many cyberattacks we’ve seen over the past few years. Hackers first send malware using an email phishing scam to a company’s weakest link—its error-prone human employees—before stealing admin credentials and hacking into networks. Once that’s complete, criminals can gain remote access to ATMs and start dispensing cash.
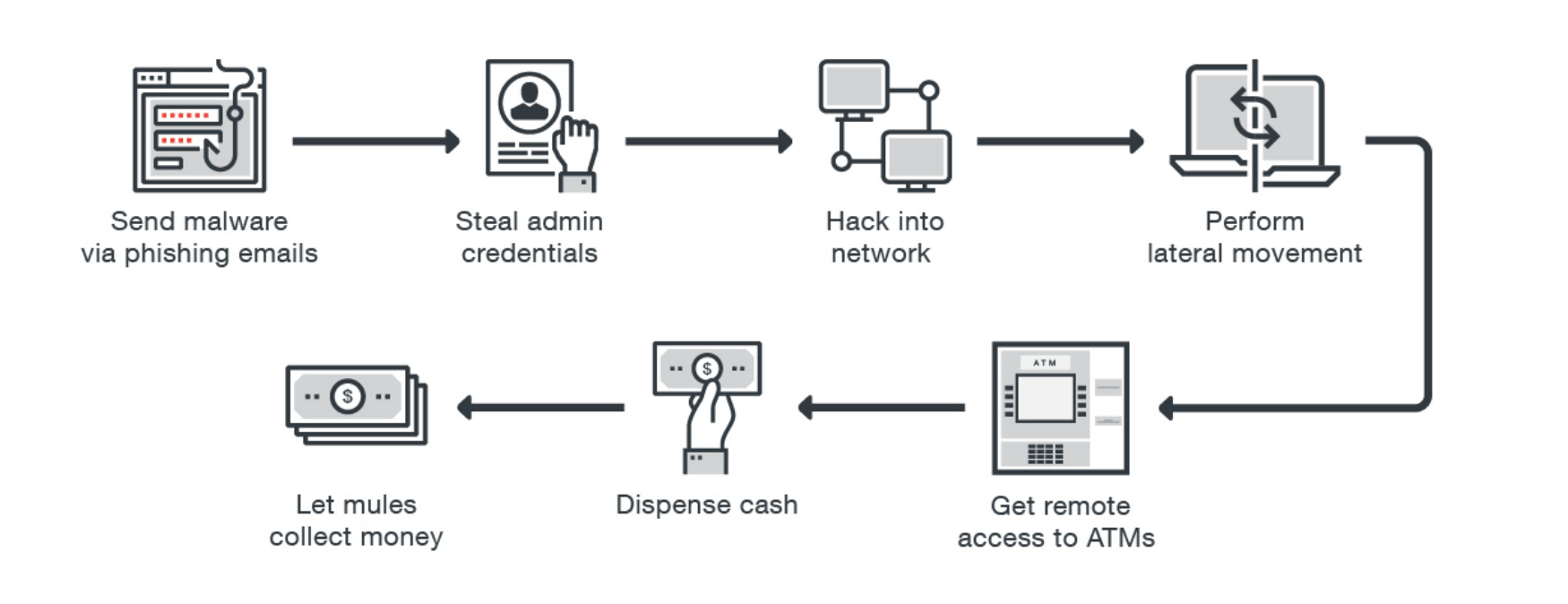
A benefit of using remote attacks is that any ATM connected to the compromised network can be attacked, unlike a physical attack which requires targeting a single machine at the most opportune time. Hackers can even attack multiple machines simultaneously, spewing out money to cash mules who act like they’re making a standard transaction. Some malware even has self-deleting properties, making it nearly impossible to trace back to the source.
Trends Micro says it worked with European Cybercrime Center (EC3) to examine how network-based attacks have developed over time. The internet security company presented the Ripper case as one of the most damaging examples. In 2016, hackers stole more than 12 million baht, or around $350,000, in Thailand from 21 ATMs. Around 10,000 machines were vulnerable to the attack.
“It could be that these are regular criminal groups that already had access to the bank’s network and eventually realized that they could hop onto the ATM network,” Trends Micro writes. “In Ripper’s case, though, it shows that some of these criminals are specifically looking for the ATM network as a target and not stumbling upon it by mere chance. These gangs have both the inclination and the technical knowledge to target these machines over any other resources of the targeted bank.”
The report explains that hackers have two main objectives when going after an ATM: to either empty its cash out or collect payment card data while people are using them, similar to a skimmer. Network-based attacks are much more complicated than physical attacks, but often lead to higher payouts.
Attacks using remote methods have not been reported in Europe or the United States, but Trends Micro and EC3 believe it is “probably going to consolidate in 2017 and beyond.”
H/T Gizmodo


