Security bugs and malware are commonplace in our connected world. With microchips in our mobile devices, wearables, computers, and even our home appliances, it seems something is always at risk of being attacked.
The latest scares, dubbed Meltdown and Spectre, are different, however. These vulnerabilities affect all x86 Intel CPUs shipped in the last 23 years. Reports also suggest that ARM and AMD processors are at risk, too. It doesn’t matter what operating system (OS) you’re running, and it’s not just your desktop—your smartphone is vulnerable too, as is data stored in the cloud on remote servers.
Meltdown and Spectre “exploit critical vulnerabilities in modern processors,” according to the official webpage on the matter, and give programs the ability to steal data being processed by your computer. Luckily, most OS makers were already made aware of the flaw and have patches available or in the works. Here’s where we currently stand, and what you need to do.
What to do to protect yourself against Meltdown and Spectre
Windows
On Wednesday, Microsoft issued a rare emergency Windows update to address the bug in Intel, ARM, and AMD chips. If you’re running Windows 10, it should have automatically downloaded and installed itself at 5pm ET. If you’re running an older system, Windows 7 or 8, the update is also available, but you may want to install it manually. The patch won’t automatically download until Tuesday next week.
In a statement to the Verge, Microsoft said that the company has “not received any information to indicate that these vulnerabilities had been used to attack our customers.”
Mac
If you’re running the latest version of macOS, you’re partially in the clear. If not, it’s time to start updating.
In macOS 10.13.2, Apple has eliminated “most, if not all” of the security concerns presented by the KPTI bug in Intel chips, according to AppleInsider. The next update, currently in development, should provide additional protections. To offer more protection against Spectre, Apple plans to release an update for Safari on macOS (and iOS, as well) “in the coming days.”
Linux
Over the past few months, some Linux patches have been released that address the issues presented by Meltdown and Spectre, but developers are working on directly addressing the Intel flaw in an upcoming kernel update. Those with Linux servers can follow the instructions here to update their systems.
Chrome and web browsers
Chromebook owners running Chrome OS 63, released Dec. 15, are protected against the flaw. The Chrome web browser also has an experimental opt-in tool called site isolation, which you can enable to help guard against Spectre hacks. Otherwise, a new patched version of Chrome is coming out Jan. 23. Other web browsers, such as Edge, Firefox, and Internet Explorer, already have patches in place in their respective latest versions.
Android
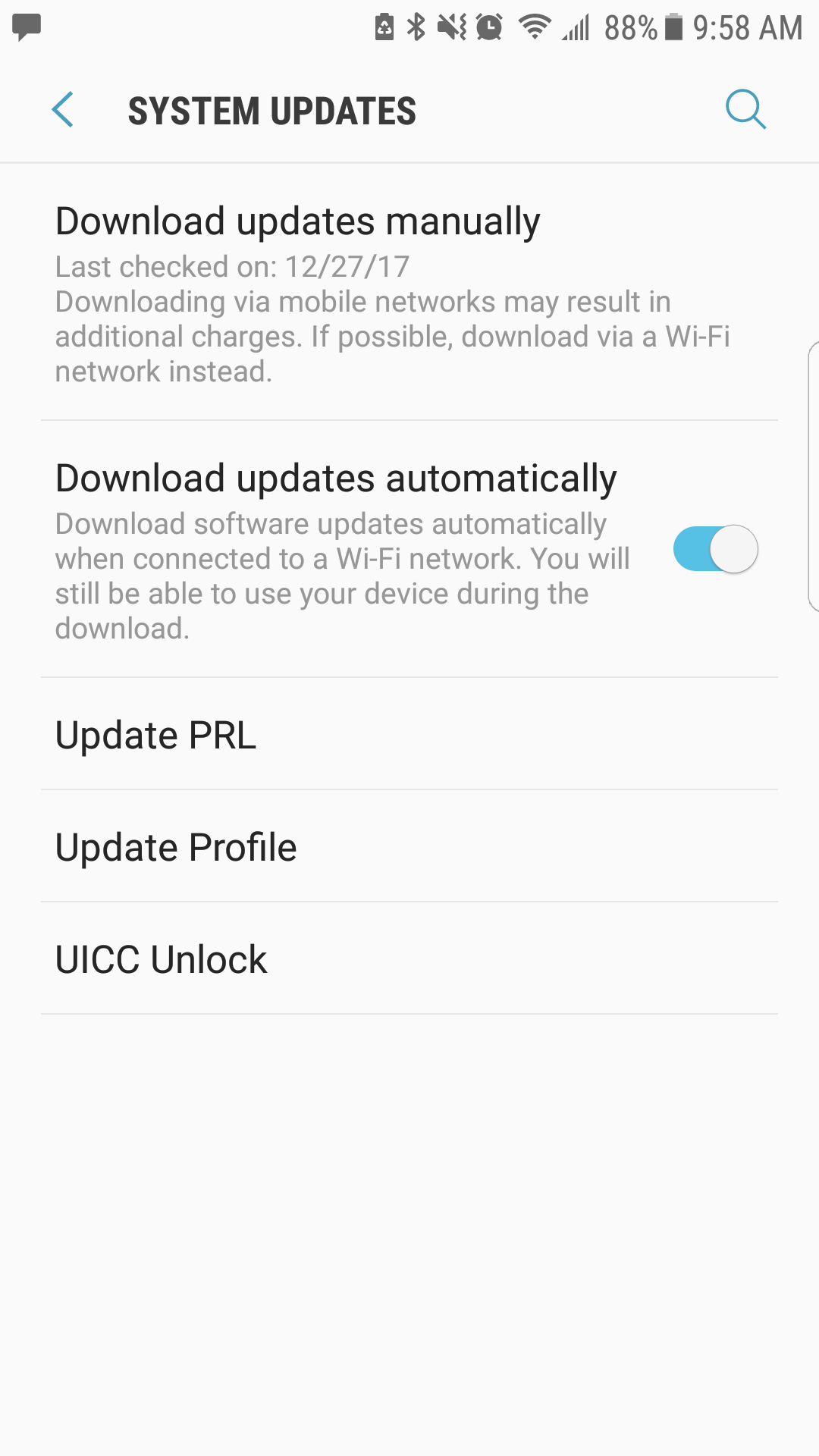
If you’re on an Android device and you’ve downloaded the most recent security update (issued monthly), congratulations—you’re in the clear. Your device is already patched against the threats of Meltdown and Spectre. If you’re not sure, you can head to your phone’s settings, then About Phone, and scroll to “Android version” and “Android security patch level” to check what version you’re running. You can then head to System, then System Update to download the latest update if you haven’t done so already.
In its security blog, Google details what devices are safe from the vulnerability and what products may need action on your part to ensure your data is protected. On top of that, Google researchers have ascertained that “exploitation has been shown to be difficult and limited on the majority of Android devices.”
iOS
Apple has confirmed in a support document that iOS and macOS devices are both vulnerable to Meltdown and Spectre, but its implemented security guards in recent updates against Meltdown-based attacks. Additional mitigation techniques against Spectre will come in a release in the next few days. The Apple Watch isn’t affected by the bugs.
Servers
Microsoft is planning scheduled maintenance for Azure on Jan. 10, and Amazon is planning a major security update to its AWS system in February. In a statement, Amazon said that most of its virtual machines are already protected. Don’t be surprised if you see downtime or slower performance in the coming days as these companies and others continue to update their systems against this critical security flaw.


