In light of recent events, this evening I decided to enable iCloud two-step verification. I expected it would be easy, but I was very, very wrong.
For reasons that defy all logic, Apple makes it extraordinarily difficult to enable two-step verification—the single most effective measure iCloud users can take against getting hacked. Not only does Apple fail to encourage iCloud users to take the powerful precaution, but it actively discourages users from setting up two-step verification. It’s nothing short of shocking.
I expected setting up the safeguard on my iCloud account to be simple, especially for a relatively advanced user like myself.
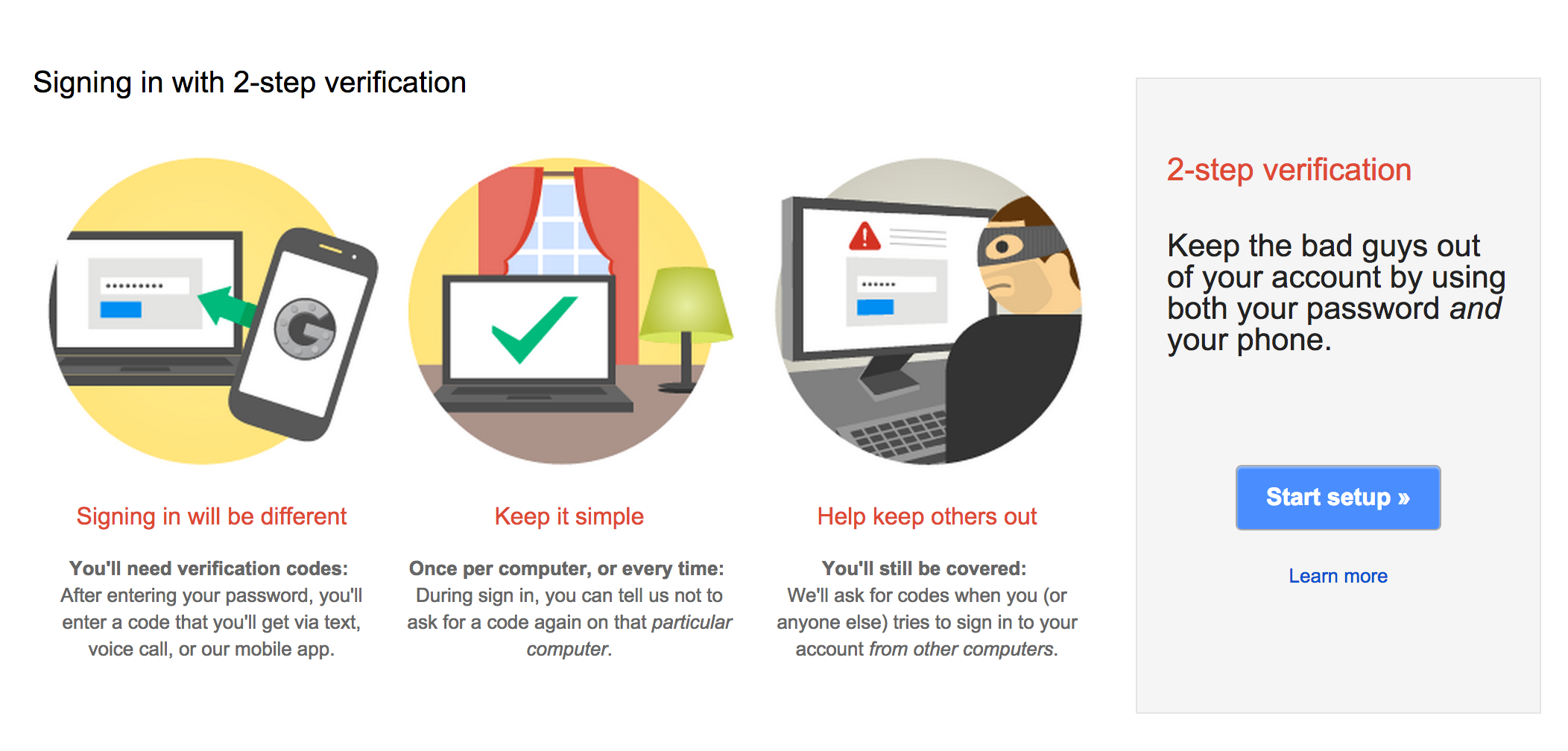
I already use two-step verification with my Google accounts. Setting it up there is a breeze (and highly encouraged)—it’s a very simple process with plenty of friendly looking support documentation to guide users on their brief journey. I use a Mac and an iPhone most of the time, but I had put off enabling two-step verification for my iCloud account. Today was the day.
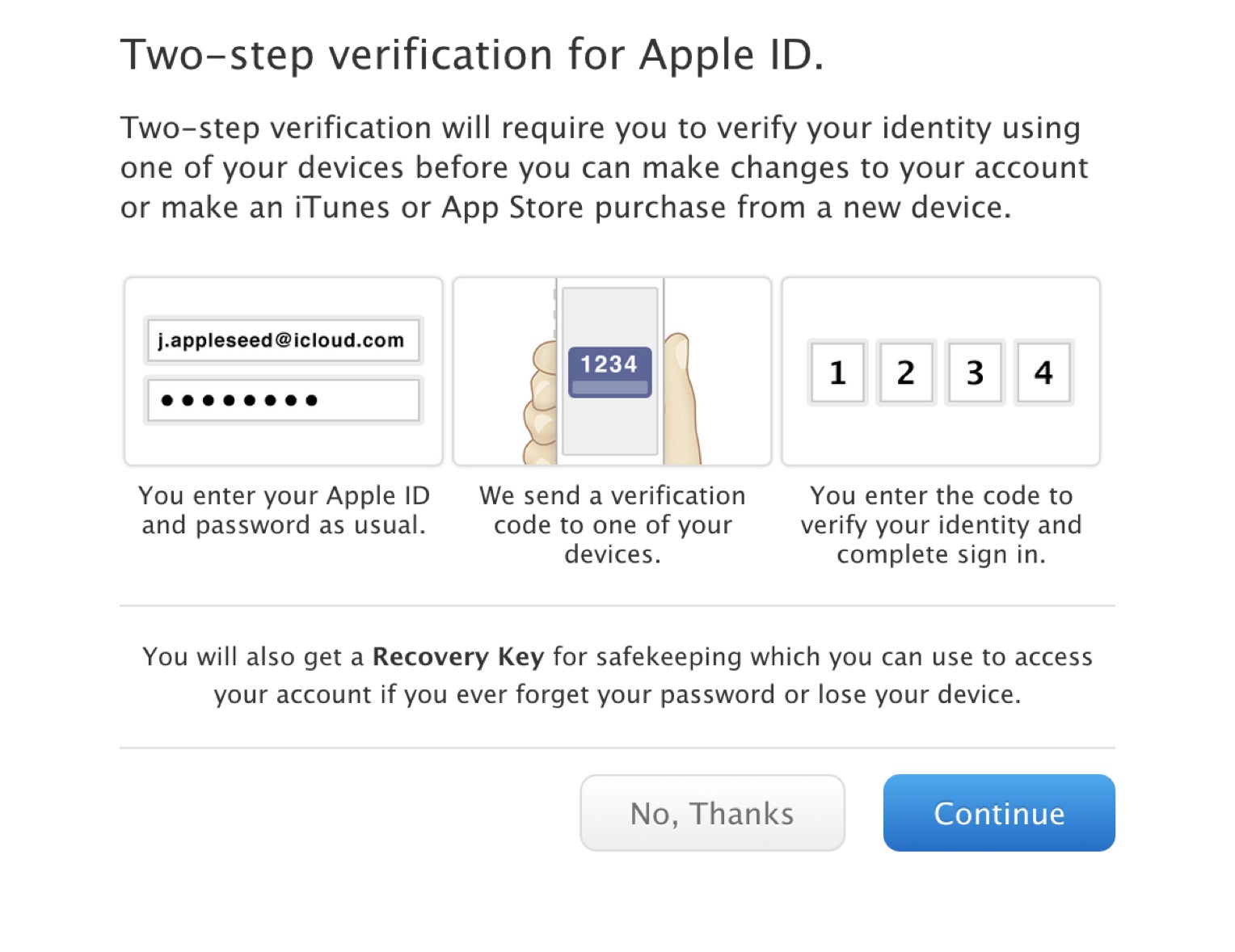
Here’s what happened. I googled “iCloud two-step” to find the right link to begin with. Once I did, I clicked through no fewer than four different pages before I was met with the button that let me turn the security measure on. (Once, it inexplicably logged me out of iCloud and I had to answer my security questions over again.) Even then, the button sat next to a button of equal size inviting me to rethink my privacy-minded actions.
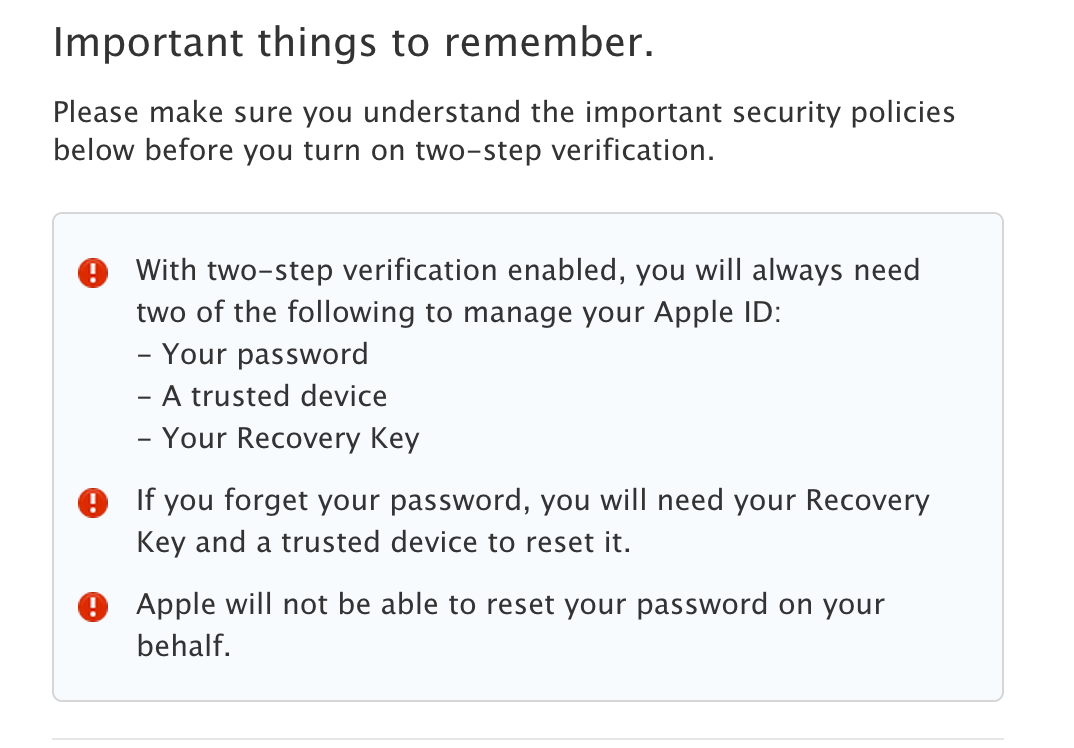
After telling Apple that, yes, I wanted to continue, I was met with the screen you see above. At first glance, I thought there was an error with my accounts. In Apple’s user interfaces, red exclamation marks usually mean that something is wrong. The psychological effect is akin to running into a virtual “Danger! Land Mines!” sign. I know that two-factor verification is a powerful way to protect my account, but it even had me thinking twice. Consumers don’t like anything that they can’t get fixed at the Genius Bar, so I can’t imagine many average users would continue with the process. It felt a little scary.
Still, I pressed on. Then I ran into this.
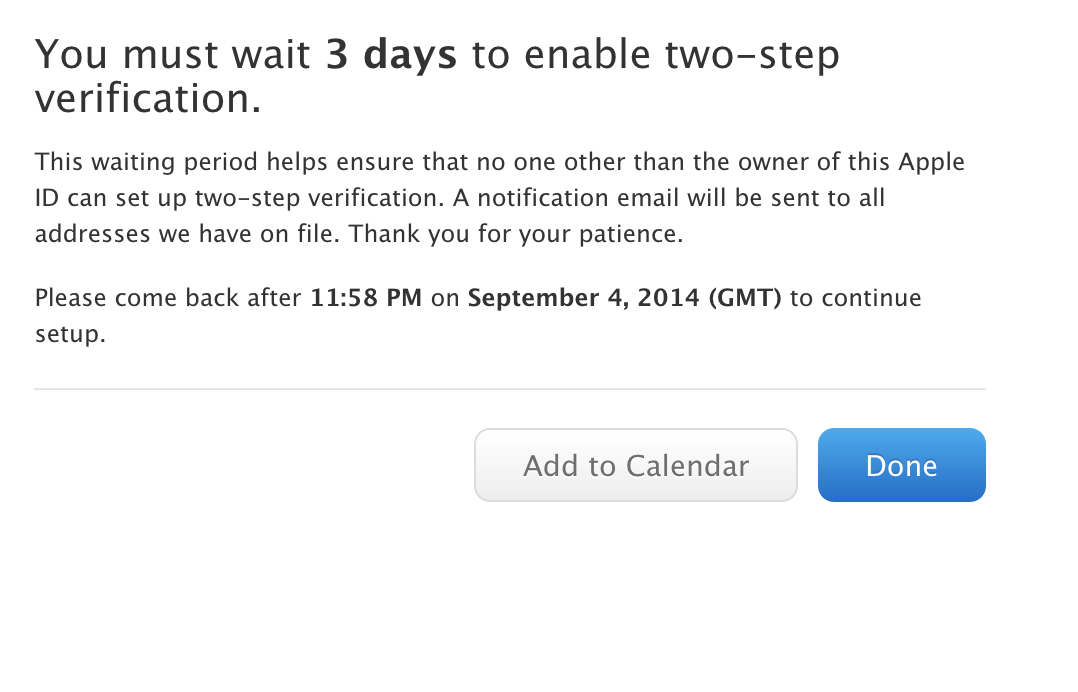
Apple wants me to wait three days to enable two-step verification… just in case someone wants to break into my iPhone and turn on a feature that will protect my iPhone? What? 36 hours is just enough time for me to absolutely not remember to scour my inbox for the notification email.
In theory, hackers could use this method to lock a legitimate user out of their account for good (assuming Apple really refuses to help at that point). But the more likely case is that they’d just tap into your unprotected account in a much more straightforward way, like by using a brute force attack—a technique that two-step verification renders useless.
Two-step verification is a form of multi-factor authentication that makes sure the person trying to get into an account (iCloud, in this case) is in fact the person who owns the associated device (my iPhone). The idea is that two-step verification enabled, someone would not only need to figure out your password, but they’d need your device in hand too.
And just for comparison’s sake, this is the presentation and wording Google uses for its two-step verification process:
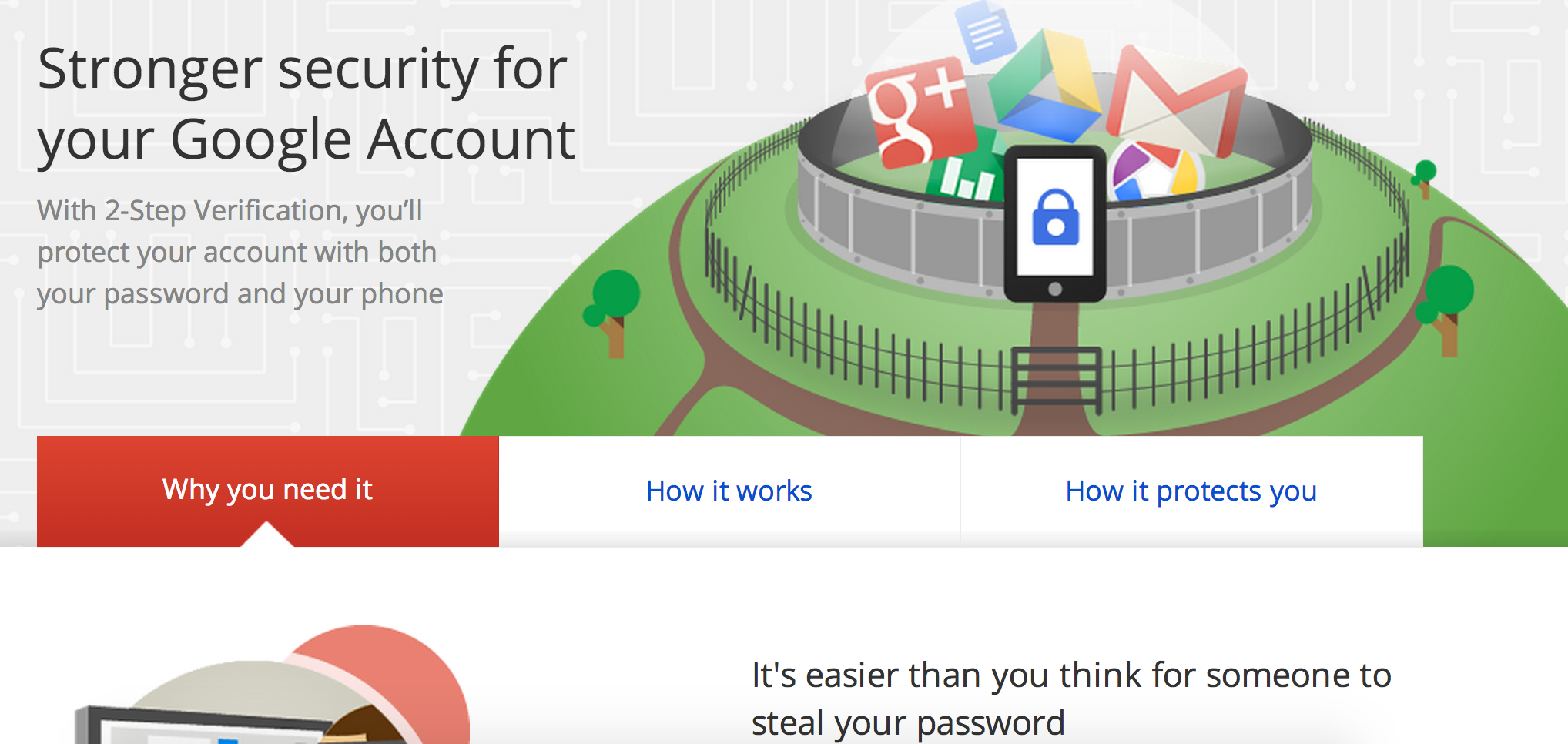
For cloud-syncing software that we use across multiple devices, this safeguard is the most robust around. Unfortunately, it only works if you can turn it on.
[Note: We reached out to Apple for an explanation of its two-step verification policies, but have yet to hear back.]
Photo via teezeh/Flickr (CC BY-SA 2.0)


