For nearly two weeks, the foundation of Turkey‘s Internet has suffered an ongoing and debilitating cyberattack.
Many suspected Russia, after tensions rose between the two countries. Then Anonymous-branded social media accounts claimed responsibility, saying it was part of their attack on the Islamic State and its supporters. The press ran with it—despite the fact that the accounts making these claims offered no evidence of their involvement, aside from some YouTube videos.
That is to say, no one truly knows who is waging an historic attack on Turkey’s Internet.
Until, perhaps, now.
A Daily Dot investigation found that the Anonymous accounts claiming responsibility for the attack on Turkey’s Internet had nothing to do with the actual attack. Furthermore, the attack was likely conducted by a single person armed with powerful cyberweapons.
In an interview with the Daily Dot conducted over encrypted messages, the person who is most likely responsible explained how he waged a successful attack against Turkey’s Internet—and why.
Wiping Turkey off the map
On Dec. 14, Turkey experienced the biggest cyberattack it has ever seen. A distributed denial-of-service (DDoS) attack targeted NIC.tr, the nameserver registering domains ending with Turkey’s country code .tr and the administrator of Turkey’s academic Internet backbone, which is used by the country’s universities.
“I know what I did, and you know that everyone can claim something and use Anonymous name as a banner.”
Successfully attacking NIC.tr means disabling Turkey’s academic Internet and every website with a domain ending in .tr. This includes almost every company and bank working in Turkey, as well as government and military websites. Some 400,000 websites are believed to have been affected.
The DDoS attack—an intentional overload of servers with “fake” traffic—reached its peak at 40 Gbps, which greatly hindered the country’s Internet. Overloaded nameservers couldn’t return any request made by normal visitors, and almost every domain ending with .tr became unreachable.
When NIC.tr admins noticed this and decided to do something about it, things got worse. They blocked all the requests coming from outside of Turkey as a defense. This helped to slow down the attacks, but when someone outside of Turkey tried to send an email to a Turkish server, they received an “unknown host” error.
For nearly a day, Turkey was invisible to the rest of the world’s Internet.
Who’s really responsible?
Everyone’s first guess was that this was an attack sponsored by a state, specifically by Russia. After Turkey’s downing of a Russian jet near the Syrian border, and given ongoing tension between the two countries, most assumed this was part of Russia’s plan. But without evidence to back up the speculation, this remains nothing more than a theory.
Others wondered if the attack came from a group called CyberBerkut, a pro-Russian, Anonymous-like hacktivist organization. But the group never claimed responsibility for the attack, as it has done after other attacks, nor has anyone leaked data about the targets, which is also standard for CyberBerkut campaigns.
Then came the attack on Turkey’s banks.
On Dec. 24, another wave of attacks targeted top Turkish banks. This attack was claimed by RedHack, a leftist hacktivist group from Turkey, soon after the attacks started. RedHack is part of the Anonymous “family,” causing some to draw links between this attack and the Anonymous videos that claimed responsibility for the ongoing DDoS. But RedHack, like many other hacktivist groups, always claims responsibility for their attacks, which they did not do for the bombardment of NIC.tr.
Anonymous steps into the fray
On Dec. 18, the fourth day of the attacks, an Anonymous-branded account uploaded a video to YouTube, claiming the attacks in the name of Anonymous as a part of its #OpISIS campaign against the Islamic State. That video has been removed, replaced by a shorter version, which was uploaded on Dec. 23.
https://www.youtube.com/watch?v=ZgUxt7fLEyg
Both videos say basically the same thing. For example, in the video above, the Anonymous voiceover claims, “We won’t accept that [Turkish President Recep Tayyip] Erdoğan, the leader of Turkey, will help ISIS any longer.” The video justifies the attacks by citing evidence that the Turkish government is helping ISIS. All of this sounds in line with Anoymous’s #OpISIS campaign, but there is no evidence that this account has anything to do with the attack on Turkey’s Internet. Other details are off, too.
First, the timing is all wrong. Anonymous generally announces its plans before launching any attack. It’s rare for Anonymous groups to wait for four days to claim their moves. And when that happens, it’s generally because they are are infiltrating networks to steal and leak data, not just launching DDoS attacks. So far, there is no evidence that the attack on Turkey involves more than DDoS.
Furthermore, the YouTube channel behind the videos has credibility issues. The channel’s first video was uploaded three months ago. After a long silence, whoever is behind the account started uploading a slew of videos about different Anonymous operations, which is unusual behavior.
More importantly, all the people we’ve contacted from Anonymous say this video is definitely not related to the attacks. Of the two longtime Anonymous members we spoke to on this topic, both guessed that the account is run by Anonymous wannabes who are trying to get credit for an unclaimed attack.
These interviews, along with chats with other hacktivists, led us to a single person. The potential attacker provided little in the way of personal details but a wealth of evidence that suggests he or she is the lone wolf crippling Turkey’s Internet.
Amplify the message
The potential attacker is a “stresser expert,” a type of hacker who understands how to use the tools at their disposal in a highly efficient way, enabling a single person to wage an attack on the level of that which struck NIC.tr.
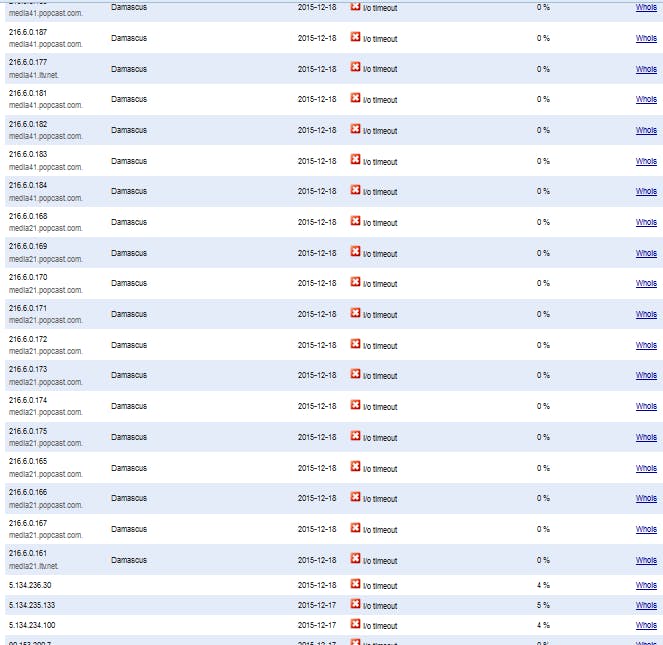
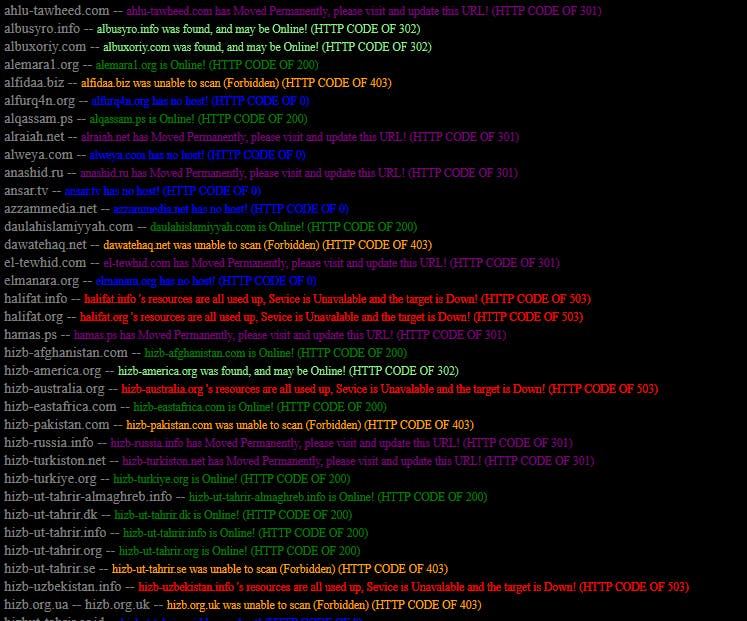
During our conversation with the NIC.tr attacker, we had a chance to see how powerful the hacker’s tools really are. In one instance, the attacker, who spoke using a throwaway pseudonym under the condition of anonymity, managed to pull down most of the Syria‘s DNS servers for around 15 minutes. The hacker also attacked the websites of a number of jihadist and radical Muslim organizations simultaneously.
The attacker says he was able to paralyze NIC.tr using, in part, a tactic called a DNS Amplification Attack. This type of attack is difficult to explain without getting deep into the weeds of cybersecurity lingo, but it basically uses the system against itself to achieve a far larger attack than might otherwise be possible. Web services company CloudFlare, which offers its clients protection against DDoS attacks, explains that a DNS Amplification Attack can be 50 times as powerful as other types of DDoS attacks.
When asked for more details about the attack, the attacker rattled off a range of technical terms about various DDoS methods, which he says he used in his efforts against Turkey’s Internet.
“Well, the type of attack varies. Sure, it’s a DNS server but due to ‘lists’ powering servers that cause DDoS, sometimes you have to choose different methods of attacks. Generally you use NTP or DNS attack against a DNS server. In this case, my DNS list was pretty weak, needs rescan. My NTP list is being used to much. So I chose DNS, SSDP and chargen against the DNS server. Normally DNS servers only accepts UDP data and DROP TCP sata – generally. If you flood the pipe enough, making the server DROP a lot of TCP packets, it will DoS itself. So chargen was its downfall, since chargen is an Amplified UDP/TCP method, using random chargen. And my chargen list is pretty powerful.”
“Chargen,” mentioned by the attacker above, is shorthand for Character Generator Protocol. The technique allows a hacker to bounce traffic off of a certain type of application that multiplies the input data and can, in turn, send up to 1,000 times more traffic to an intended victim’s server, potentially overloading the targeted machine.
We also asked whether the attacker tested NIC.tr for specific weaknesses. The attacker said his effort was experimental and that he learned the most effective methods of attack on the fly.
“40Gbps was not something I calculated, it’s “Is it down yet or not” Kind of a thing, you send 10Gbps, no, send another 10Gbps, no, send another 10, almost down, send another 10 and down – check it multiple times and it’s down for more than 12 minutes and you got your answer, no WAF or firewall kicked in, etc. So basically you stop the attack, wait 5 minutes and then send it all at once to flood the pipe faster and harder, generally can nullroute depending on the server and what router runs the network etc.”
The Anonymous connection
The attacker, who did not reveal his nationality, said his reasons for hitting NIC.tr are definitely political, calling it a protest. The attacker said he saw the news, documents, and claims that the Turkish government—and Turkish President Recep Tayyip Erdoğan specifically—were helping ISIS, or at least turning a blind eye against the group, which inspired the attack. Besides, he said, he was already helping some Anonymous groups in organizing #OpISIS.
The attacker says, however, that he does not operate under the Anonymous banner full time. The attacker occasionally works with different Anonymous teams, but he says he often works alone. It’s reasonable to call the attacker a part-time Anonymous hacktivist.
So does this mean that this was an Anonymous attack? Not exactly—or, at least, not how you might imagine it. The attacker said this DDoS was a one-man operation, planned only by himself.
When we asked about the Anonymous video claiming responsibility, the attacker had a simple answer.
“I know what I did,” he said, “and you know that everyone can claim something and use Anonymous name as a banner.”
Illustration by Max Fleishman