How do you turn the enemy of privacy into an ally?
Smartphones have long been derided as an invader against digital privacy and anonymity. They watch you, hear you, and most likely know you better than any other device you own. Hackers, telephone companies, governments, and a variety of third parties gleen all sorts of personal data from your phone, often with little consent or knowledge from you.
“Cellphones are tracking devices that make phone calls,” software developer Jacob Appelbaum said in 2013.
That’s not good. Mobile devices like phones and tablets are the most popular, affordable, and fastest-selling devices on the planet. If we can’t figure out privacy for phones, anyone who cares about privacy is losing the battle.
On home computers, a wide range of tools exist to help guard against unwanted eavesdroppers. For instance, the Tor anonymity network is one of the most popular and powerful privacy programs ever, with over 150 million downloads in the last year alone.
Tor has been available on Android phones for some time, but its utility has been somewhat limited. Now, a new suite of programs allows users to anonymize every app they run, giving them the kind of strong protection needed to maintain real privacy. Here are the three apps you should download right now.
1) Orwall
The newest weapon in your mobile privacy arsenal, first released in July, is Orwall.
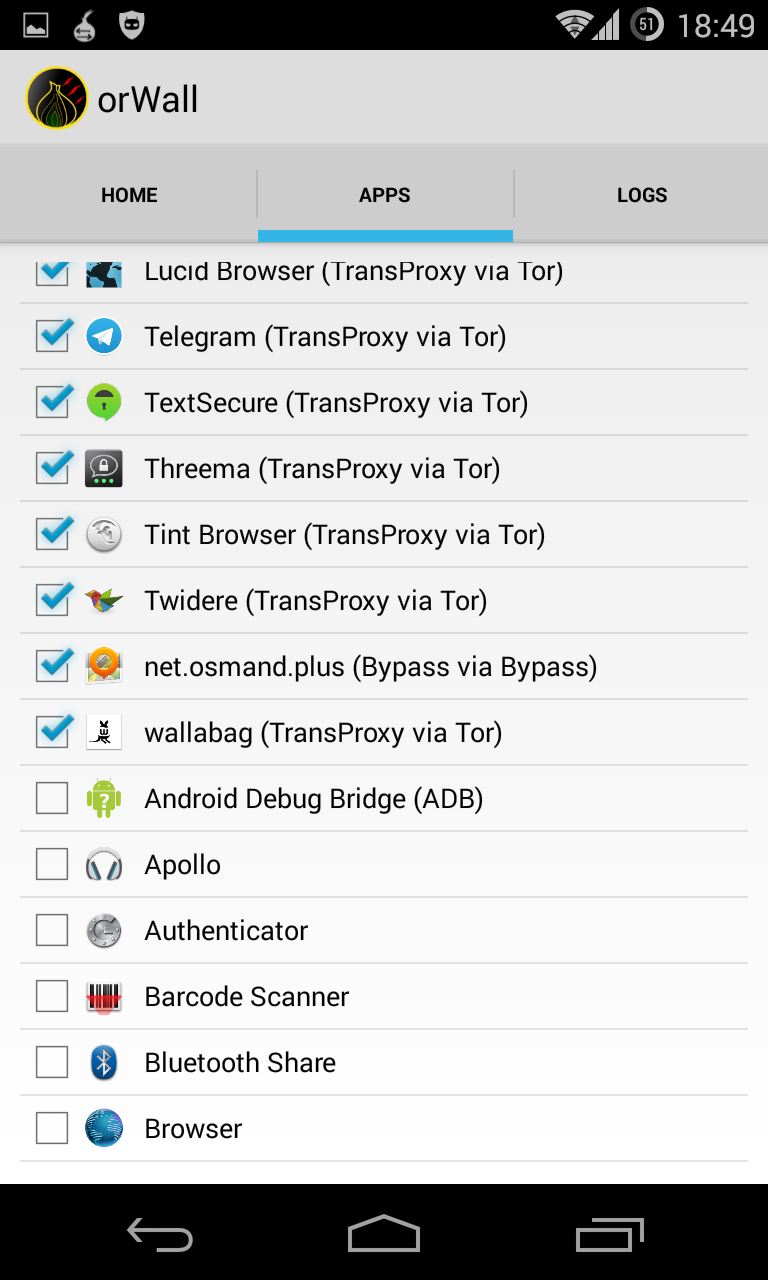
As its name suggests, Orwall is like a firewall for your phone. It forces almost all applications through the Tor network, and it prevents other applications from having any other kind of network access.
To put it in simple terms, Orwall helps built a barrier between your phone and the outside world. It then opens only a single door to walk through towards the Internet: Apps can only make connections through Tor, or they can’t connect at all.
Thanks to longtime Tor developer Mike Perry, Orwall has recently received increased attention from the Tor community itself. It was developed by Cédric Jeanneret, a Swiss computer scientist and privacy activist behind EthACK.org, the “Swiss privacy bootcamp.”
Orwall requires root access to your phone (find out how to do that here), so it’s a little bit of work compared to a simple Google Play installation, but it pays off in expanded usability and protection.
2) Orbot
The next app in your arsenal, and likely the most essential, is Orbot.
Orbot is what allows you to actually make that connection to Tor. It’s extremely easy to download and install—just grab it in the Google Play store—but it also allows some advanced configuration, if you’re willing to put in the work.
Developed by the Android anti-censorship wizards at the Guardian Project, Orbot has several important functions. Like Orwall, it can push many of your mobile apps to use Tor. However, Orbot’s functionality is limited to apps that have proxy options, so using it with Orwall significantly expands the kind of Android apps that can use Tor and locks down the apps that don’t.
“Consider Orbot as a simple connector to Tor,” developer Cedric Jeanneret told the Daily Dot. “Orwall is the glue helping stupid apps without any knowledge of proxies to connect through Tor.”
That “simple connector” can be fairly called the most important part of the equation.

3) Orweb
The final program you’ll need is Orweb, the private mobile Web browser.
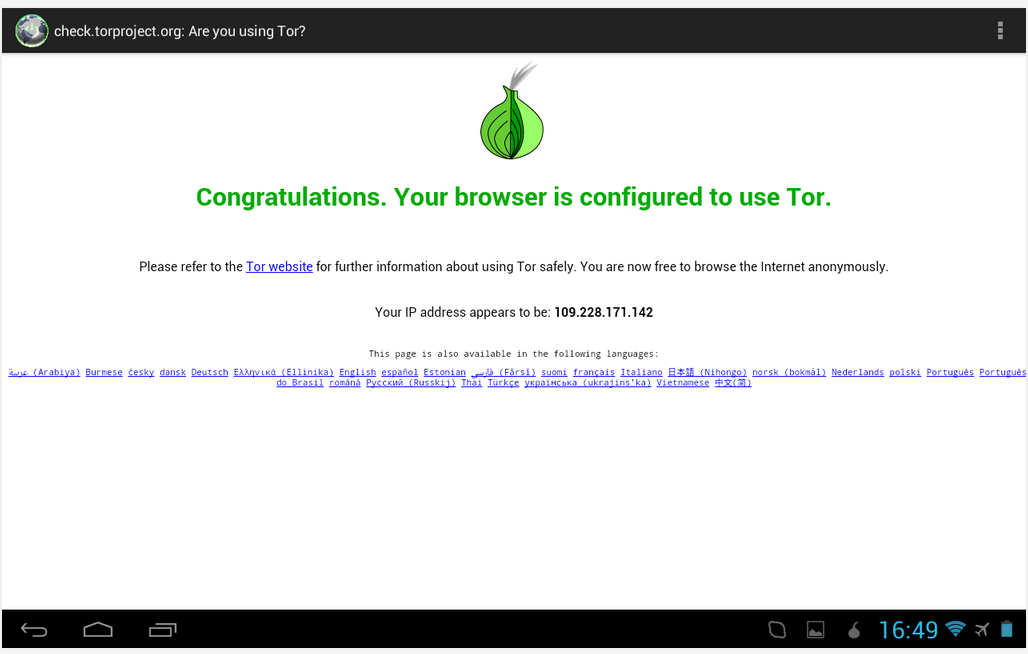
Orweb, also developed by the Guardian Project, is Orbot’s sister app. It’s the most private mobile browser on the market.
Utilizing the Tor network and configured to keep your data private, Orweb acts as the Android phone counterpart to the famous Tor browser that allows you to access the Internet anonymously as well as surf Tor’s hidden services.
These three programs do not add up to a silver bullet of perfect privacy—because a silver bullet doesn’t exist. There is no such thing as 100 percent security, and anyone who promises you an “NSA-proof” computer program is a snake-oil salesman.
Using these programs is a start, however, to flipping your phone from soft target to hardened privacy tool.
Photo via Opopododo/Flickr (CC BY 2.0)
