Blackphone, the supposedly ironclad mobile device that places emphasis on protected and secure communications, found a chink in its armor. A recently fixed vulnerability in the phone’s suite of apps made it possible for attackers to decrypt messages, steal contacts, and take control of device functions remotely.
The bug was found in SilentText, the messaging app developed by Blackphone maker Silent Circle that comes bundled with the device. SilentText allows users to send messages through encrypted channels created by Silent Circle’s Instant Message Protocol (SCIMP). The implementation of SCIMP on Blackphone, known as libscimp, contained a memory corruption flaw known as a type confusion vulnerability.
Essentially, someone could exploit the bug by corrupting a pointer in the memory and gaining remote access to arbitrary code execution on the handset. The potentially damaging end result could be loss of data or a complete hijacking of the device.
The flaw was brought to the attention of Blackphone by Mark Dowd, a consultant at Australian-based Azimuth Security. He reported the bug to Silent Circle to be addressed before detailed the findings of the flaw in a blog post. Dowd spoke about type confusion vulnerabilities at a Black Hat security conference in 2009.
Even with the flaw fixed, it’s worth noting that there is no such thing as completely foolproof security measures. Blackphone purports to be the safest mode of communication available and it fell victim to a vulnerability. If anything, it should serve as a good reminder to take extra precautions with your own privacy.
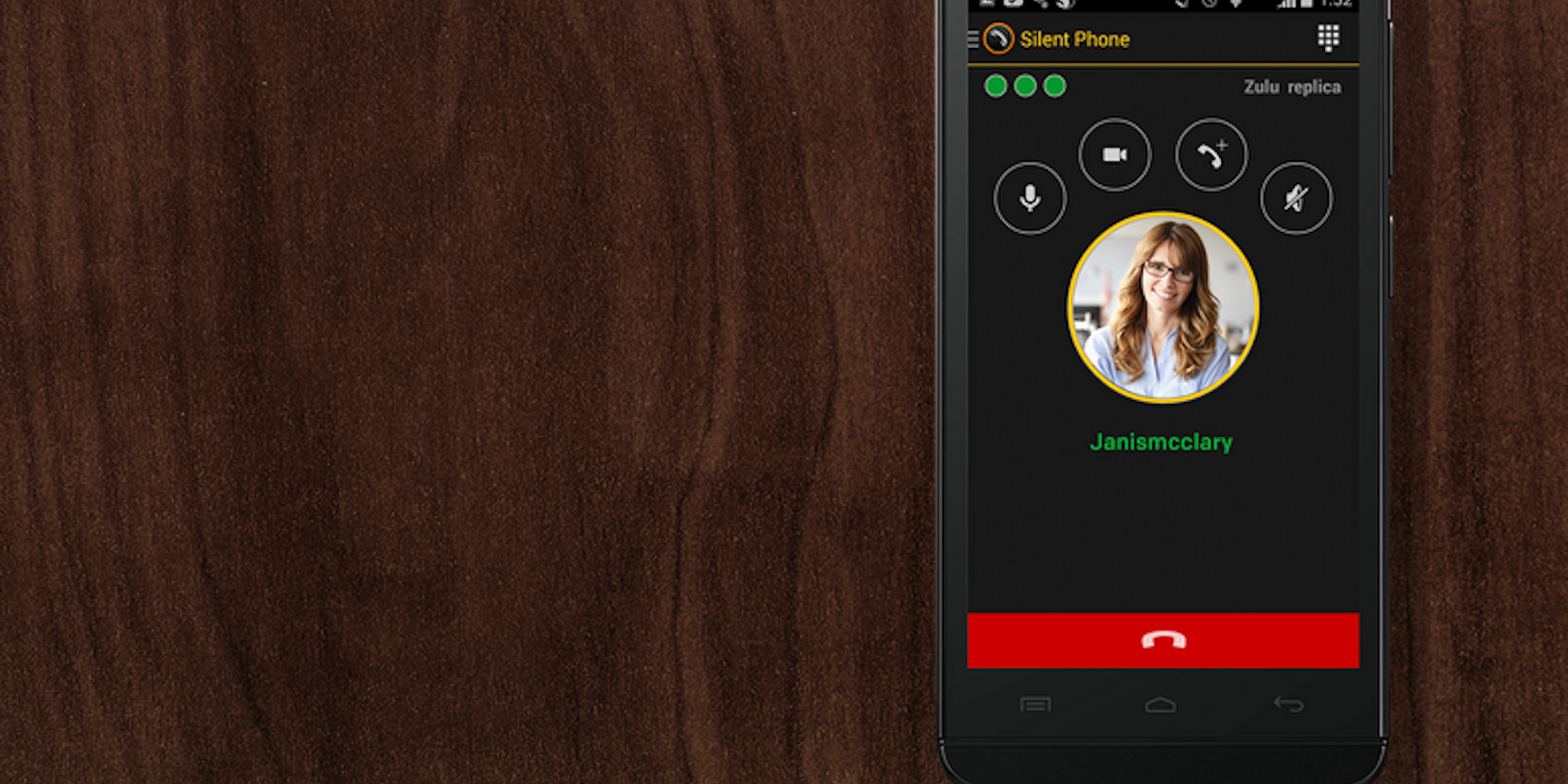
H/T Ars Technica | Photo via Blackphone