A popular app that allows anyone to find their celebrity look-alike left users’ photos exposed online, TechCrunch reports.
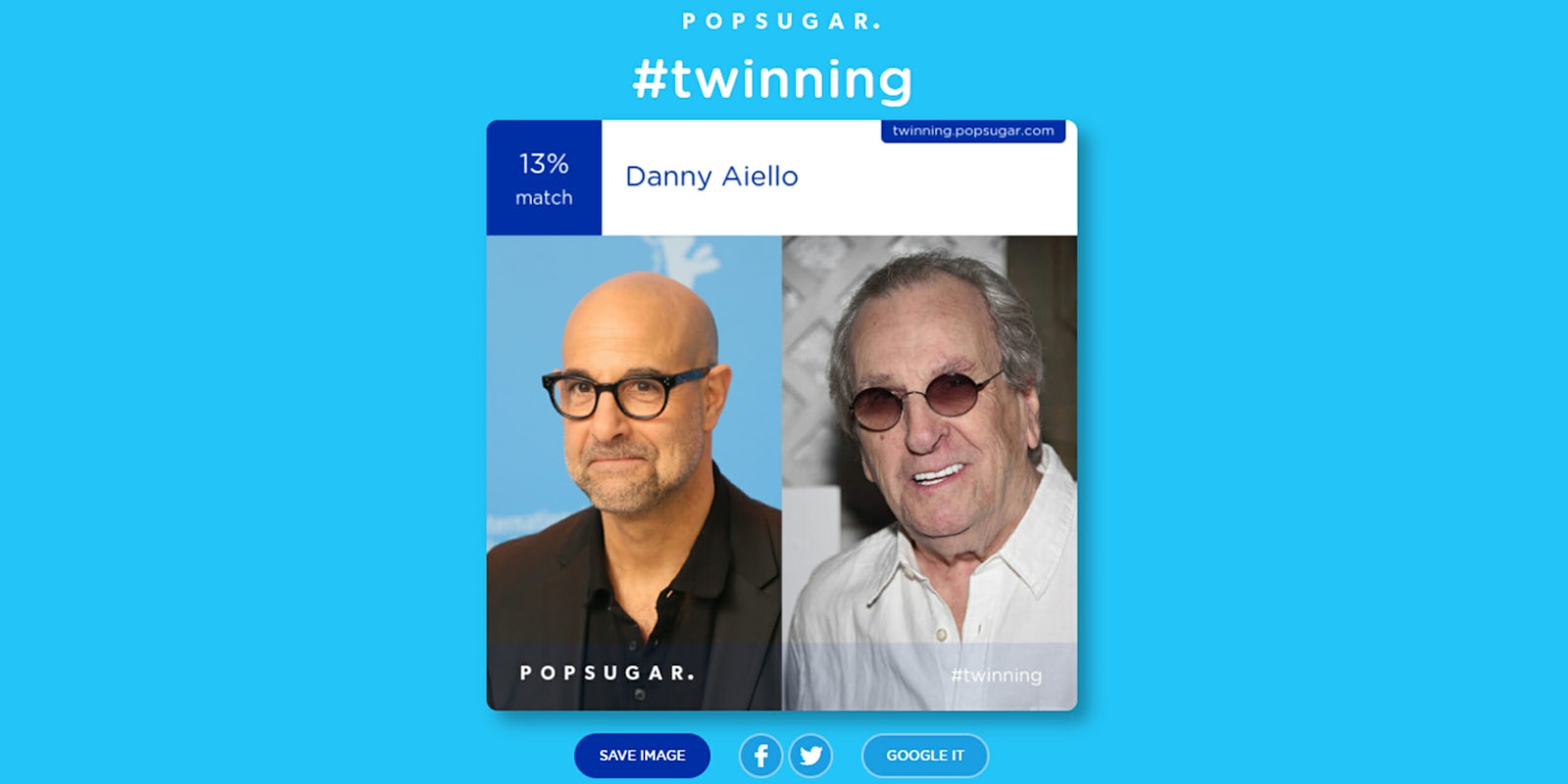
The “Twinning” tool, developed by American media and technology company PopSugar, works by comparing a selfie or any other image to a database of celebrity photos. Users can then share their results, which includes their top five look-alikes as well as their “twinning percentage,” on social media.
But TechCrunch’s examination of the Twinning tool’s source code reveals the web address of where the selfies are uploaded—an Amazon Web Services storage bucket.
That bucket, however, was not secured properly, allowing anyone with its URL to view and download the hundreds of thousands of selfies being uploaded in real-time.
TechCrunch says it was able to verify the issue by “uploading a dummy photo of a certain file size at a specific time.”
“Then, we scraped a list of filenames uploaded during that time period from the bucket’s web address, downloaded them and found our uploaded image by searching for that photo of a certain file size. (We didn’t download any more than necessary to preserve people’s privacy.)” TechCrunch states.
Although PopSugar did not respond to requests for comment from TechCrunch, the publication says the bucket was quickly locked down after it sent an email.
Mike Patnode, vice president of engineering at PopSugar, later admitted to TechCrunch that “the bucket permissions weren’t set up correctly.”
While users may not be concerned about their selfies being exposed, the incident is a reminder of how vulnerable data can be online. Had the mistake involved social security numbers or other personal information, the results may have been much more serious.