The ultimate way to keep your computer safe, we all thought, is to keep it off the Internet.
Building an “air gap” between your machine and the Web has long been one of the cornerstones of digital security. Intelligence agencies, secretive militaries, national security journalists, corporate technologists, and almost everyone else with extremely sensitive data to protect has used this technique.
Journalists and experts working on Edward Snowden’s documents use air gapped machines. The most powerful governments on earth use it to protect their own networks from adversaries on the Internet.
But even an air gap can be beat.
New research from top Israeli cryptographers recently outlined how an all-in-one printer, complete with built-in scanner, can be used to sneak into air-gapped machines and networks and walk out with all the data you please.
With no Internet connection, the attack must begin by infecting target through other means. That can be as simple as briefly plugging a USB drive into a computer, the way it’s theorized that American spies have attacked adversaries like Iran. However, when the Americans did it in the past, they had no way to communicate with the malware and therefore could not do more or take data out. After the initial plug-in, the attack was on auto-pilot and couldn’t communicate back with its owners.
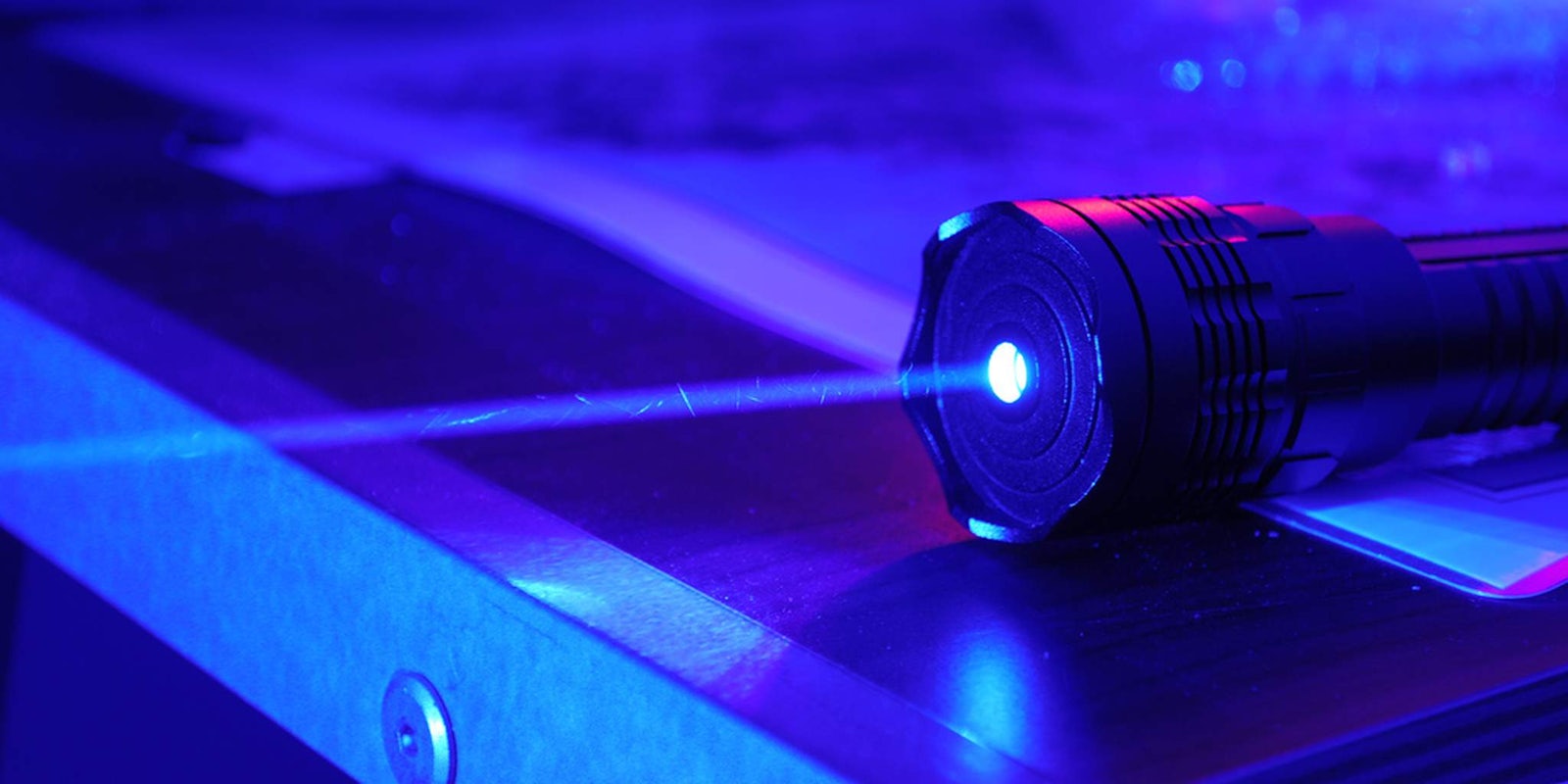
This new attack changes all that. Now, attackers can control and communicate with malware. The technique uses a long-distance laser to break in and a video camera on a drone to break out. The heist breaks down an important digital safety guard used to protect all sorts of secret data.
The research was presented by cryptographers Adi Shamir, Yuval Elovici, and Moti Guri at the Black Hat Europe hacking conference earlier this month.
Shamir and his team set their sights on Beersheba, Israel’s self-described cybersecurity hub, where many major tech firms have regional offices, and focused on an HP Officejet Pro 8500, though the attack is not limited to that device.
The team sent signals from more than 1 kilometer away—though its range could reach as high as 5 kilometers—using a blue laser that blinks malware in binary code. The printer’s scanner, in turn, reads that code, and sends new instructions to the malware.
That’s how you get malware doing its job on the air gapped system. To get stolen data out, the scanner that originally read the code can also send code outward in blinks of light. Shamir’s team used a small drone and video camera to hover 100 meters over the scanner and record the light, but any recording device can do.
This isn’t the first time an air gapped system has shown weakness. In addition to Stuxnet, researchers last year explored attacking air gapped machines through speakers.
All of a sudden, militaries all over the world aren’t just unplugging their Internet connection. They’re unplugging their printers, too.
H/T Bruce Schneier | Photo via fastlizard4 (CC BY SA 2.0)