by COLE STRYKER
Last year I wrote a book about 4chan and the hacktivist collective that sprang from its sordid trenches called Anonymous. This phenomenon became the biggest tech story of the year, and brought the identity question to the forefront of public discourse. When discussing Anonymous with friends and family, I found that there was a widespread knee-jerk reaction all too common when anti-social people encounter a new brand, or a new tool.
“There oughtta be a law,” these people would say. “People shouldn’t be allowed to say and do horrible things anonymously and get away with it. You couldn’t pull that crap in the street, why do we allow it online?”
It turns out that a lot of people feel this way. So I wrote Hacking The Future. It explores prominent manifestations of anonymity and traces a dual history of anonymous activism and technology in order to put today’s headlines in context. The excerpt below deals with hackers, specifically, the hacker ethic. It’s an extension of the free world’s rich heritage of anonymous speech, and it informs today’s hacktivists as both a philosophy and an aesthetic. If you’ve ever wondered what drives hackers to make mischief and fight for freedom, you’ll find part of the answer in this brief genealogy.
 The Hacker Ethic
The Hacker Ethic
After World War II, “Ma Bell” updated their long-distance switching system, basing it on twelve distinct “master tones.” When you dialed a number, you would hear a series of tones. This sound was generated by telephone computers sending information to each other to set up the call. The system would produce a combination of two fixed single-frequency tones played simultaneously. Eventually someone figured it out—Joe Engressia, a five-year-old blind kid with an acute sense of hearing and the ability to whistle the tones with perfect pitch. He was whistling out of boredom once when goofing around on the phone and the phone disconnected. So he called up the switch room and asked why. They explained the tone system, which fueled his desire to learn more. Within a few years, a vast network of “phone phreaks,” mostly kids, many of them blind, had sprouted up throughout the country. They memorized the clicks and whirs of the system and figured out which combinations of tones could accomplish what.
The ability to manipulate the network and exploit its flaws was intoxicating for the phreakers, but it wasn’t about the free phone calls. The early phreakers loved computer systems, figuring out how they worked, where they broke down. Some of them would call the company to give them tips about how to improve their system in order to make phreaking more difficult. This was done out of boredom—it would provide them with a greater challenge—but also out of an almost autistic appreciation for perfect systems.
The phreakers were geeks, before the word was commonly used to describe someone with an obsessive passion for a niche area of interest. Over time they figured out how to “trip” around the world on phone lines, calling up exotic locations and setting up conference calls with one another—all free and, as a result, all illegal. The sense of adventure and discovery must have been euphoric for these kids, especially the blind ones, who might typically be dependent on the help of others to travel to the grocery store. And here they were, virtually gallivanting across the globe through the wires. The ability to control and manipulate a global communications network, when so much of one’s life is determined by the decisions of parents and other authority figures, would be attractive to any teenager. It was this illicit thrill that would define the motivations of generations of hackers to come. By the ‘70s they had figured out how to make machines, dubbed “blue boxes,” that would generate exactly the right tones. A couple of teenagers, both named Steve, made the first digital blue box, before going on to found a prominent tech company called Apple. 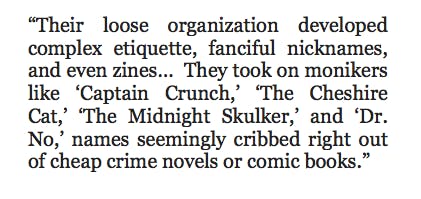
Their loose organization developed complex etiquette, fanciful nicknames, and even zines. In many cases, anonymity played a crucial role in preserving the integrity of the community. AT&T was understandably disturbed by the phreakers’ activities and took pains to figure out how to expose them. They took on monikers like “Captain Crunch,” “The Cheshire Cat,” “The Midnight Skulker,” and “Dr. No,” names seemingly cribbed right out of cheap crime novels or comic books. They were fun and flashy but deadly important, considering that messing with the phone system could land one in jail. The phreakers’ tendency to adopt noms de guerre directly influenced the pseudonymous nature of the early Internet, prompting the default use of handles and nicknames on early BBSs, especially among hackers who continued to bend the law in order to master computer systems similar to the way the phreakers owned Ma Bell.
Even though most of them had never met in the real world, and didn’t even know each other’s real names, the community grew. Most remarkably, all of this was done outside of any extant institutional channels. It rose organically through the sheer power of, and enthusiasm for, emerging networking technology.
The phreakers were the first hackers, and with the rise of the home computer, they realized that the hacking possibilities with these new machines were comparatively limitless. A hacker club emerged at MIT, whose members whiled away their days manipulating the mainframe computing systems on campus, figuring out ways to make them perform not just more efficiently, but differently. With the rise of networked computing, hacker clubs with names like the Knights of Shadow, Cult of the Dead Cow, Legion of Doom, and Chaos Club popped up throughout the world. 2600: The Hacker Quarterly, named after the frequency the phreakers used to bust into the phone system, published its first issue in 1984.
As the hacker underground developed, those with more sinister inclinations began to appear in headlines. Some hacker collectives, while not explicitly antisocial, were prankish in nature. The Cult of the Dead Cow declared war on the Church of Scientology a decade before Anonymous got around to it. But for the most part, hackers were about improving systems of all kinds through the open sharing of information. In Hackers: Heroes of the Computer Revolution, Steven Levy summarizes the hacker ethic’s five general tenets:
- Sharing
- Openness
- Decentralization
- Free access to computers
- World Improvement
Dave Marcus is the director of security research and communications at McAfee Labs, but beyond that, he’s a hacker. He spends a lot of time with fellow hackers in a place called “Unallocated Space”: eighteen hundred square feet dedicated to geeks exploring systems, analyzing problems, and figuring out solutions. They do hardware hacking. They do lasers. They do robotics and lock picking and carpentry and something called “fire vortexes.” It’s a sandbox environment for geeks to learn about how stuff works.
Some of the hackers Dave hangs out with are deeply concerned with hacktivism, privacy issues, and legislation that affects the Internet; others couldn’t care less:
It’s about answering the question, “Why?” Why does it work like that? Why was it designed like that? What happens when it malfunctions? It could be carpentry, or robotics, or metal-smithing. Hacking is basically an inquisitive way of looking at something and asking, “How can I make this do something it wasn’t designed to do? It can do twelve things, how can I make it do that thirteenth thing?”
Chris Wysopal is another one of those hacker–turned–security experts. Currently the CTO of Veracode, a security company that boasts clients like the Federal Aviation Administration and Barclays, Wysopal spent his college years exploring the technology behind computer systems. He got a taste for the hacker world by dialing up BBSs and accessing text files, written by fellow hackers, that explained how phone and computer systems worked.
Because several of the security experts I’ve spoken with grew up hacking into other people’s networks, I asked Wysopal if he could estimate how much of his industry is made up of people who grew up doing the sorts of things that the industry tries to expose.
I wouldn’t draw the line at people who say they have accessed networks illegally because you just never know what is truth. Some people tell tall tales and some people are very quiet about any illegal activity. You know a hacker pretty quickly after a few minutes of conversation. They know how to penetrate systems, how to size up the weak spots, and how to operate with stealth. They see technology and they just think differently about it. They understand how to control it and manipulate it in ways never intended by the designers. I would say about 20% of the industry thinks like this. They end up at security consulting companies and in the research teams at software and service providers.
The cyber security industry can be described as an arms race between people building and maintaining systems and those who want to break into those systems. Among the latter group, white-hat hackers do it to show off their skill and point out flaws, whereas black-hat hackers do it to steal data or humiliate a victim. The thrill of keeping smart hackers out can be as rewarding as hacking itself. But with Anonymous bringing attention to some of the adventures available to those with enough savviness to figure out how to download the LOIC (not much), the average company now has to contend with the potential of an army of faceless teenagers bearing down on its servers with the fury of a DDoS attack. And according to Wysopal, most of them simply aren’t prepared. He says that organizations have been focused on stopping cybercrime and, to some extent, the theft of their intellectual property. They have hardened their financial systems and put access control around secrets.
But malicious hackers don’t always target those things. Some, like Anonymous, seek to raise awareness of the injustices they see. This can be done by simply embarrassing the target by exposing any information for which they are custodians, such as customer names and e-mail addresses. Another technique is to simply deface a Web site of little importance that is associated with the target or bring it down through DDoS. All of these techniques send a message that the target is incompetent or not to be trusted. 
The more recently politicized hacktivist groups embody the aforementioned elements of the Hacker Ethic as defined by Levy, but is the group sustainable within the broader hacker ecosystem? Will corporate network systems adapt to the threat of low-level mass attacks and infiltrations, or will Anonymous figure out ways to stay one step ahead? Wysopal and many others think they are here to stay.
I think Anonymous can adapt. Their actions have certainly had an effect in raising awareness to the vulnerabilities they have exploited and the security industry is paying attention. There are already solutions to most of the attacks Anonymous uses, it’s just that the target companies and organizations don’t want to make the tradeoff in cost or flexibility in their computer operations. …Additionally when investigations start people go underground and figure out new ways of operating. New people spring up. I don’t think Anonymous will just go away.
Computer security is like insurance. It seems really expensive until you need it. If anything, groups like Anonymous will behave as an inoculation against real cyber threats, like the Russian hacker ring that infiltrates your network, steals millions of dollars’ worth of data, and sells it on the black market data trade …without you even knowing they were in your system. Karim Hijazi, of security contractor Unveillance, which does business with clients in the pharmaceutical and tech industries, among others, told me that the real bad guys will lease botnets for a few weeks, use them to infiltrate a network, pillage millions of dollars’ worth of data, then leak a story to the media, telling them that their target is leaking information. Then they’ll short sell the stock, making even more money off the resulting media frenzy.
Anonymous, despite causing relatively little damage (with two big exceptions—HBGary and Sony, which managed to survive the attacks with egg on their faces), has caused a great deal of awareness for the need for cyber security among companies who deal with large amounts of sensitive data.
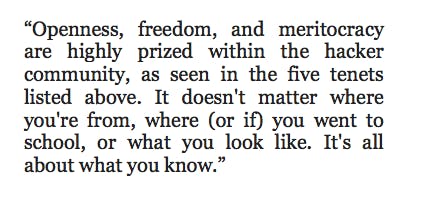
Openness, freedom, and meritocracy are highly prized within the hacker community, as seen in the five tenets listed above. It doesn’t matter where you’re from, where (or if) you went to school, or what you look like. It’s all about what you know. For the hackers, computer technology leveled the playing field and enabled them to achieve a sense of social equality within the virtual world that they might otherwise not have enjoyed. One’s ability to hack is the ultimate determinant of acceptance within hacker groups. Not all hackers distrust authority, but many do. They see authority figures imposing their will (not to mention their flawed systems) through legislation, excessive policing, closed systems, privacy intrusions, and other forms of bureaucratic bullying. Hackers know they can do it better.
The expansion of hacktivism indicates a natural evolution of the hacker subculture, although I must stress that most skilled hackers look down on Anonymous. They are recognized, rightly, as a handful of computer geniuses who actually know what they’re doing, surrounded by a multitude of loud and often sophomoric voices who exist only to cheerlead. However, Anonymous marks the advent of collaborative hacking. As the internet has become more social, so too has hacktivism. Tools like DDoS require the power of the collective to be effective. Twitter has become a soapbox for hackers who wish to flaunt their epic wins and taunt victims and rivals.
Given all this, it’s easy to see why anonymity, or, in most cases, pseudonymity, flourishes within hacker circles. It’s not simply because hackers tend toward illicit activities. A pseudonym puts the focus on the act rather than the actor. It reinforces the universal code of meritocracy within the hacker underground. Anonymous as Guy Fawkes mask-wearing hacktivist might not live forever, but his ideals, which match up nicely with the hacker ethic, will.
The Web is bursting with new ways of reading and writing. Publishing is changing—from what people want to read, to how they want to read it. The rise of the e-book, new media tools, and new communities of readers and writers are transforming the very way we tell stories. This series will feature excerpts from the work of digitally self- published authors, e-book authors, or from new books that look at Internet culture in order to give a taste of the new frontier of literature in the digital age.
Photograph by Adobe of Chaos
Reprinted by arrangement with Overlook Duckworth, Peter Mayer Publishers, Inc., from Hacking the Future, by Cole Stryker. Copyright © 2012 by Cole Stryker.