A Federal Court judge in Idaho has ordered a programmer’s computer seized and its contents copied because he described himself as a “hacker.”
Lynn Winmill, judge on the U.S. District Court for the District of Idaho, called his own decision “very rare” and “extraordinary,” according to Computerworld.
“The tipping point for the Court,” he wrote, “comes from evidence that the defendants – in their own words – are hackers.”
A hacker is someone who creatively manipulates code. That’s it. Many hackers prefer the term “black hat hacker” or “cracker” for someone who uses that talent for personal gain or in defiance of the law.
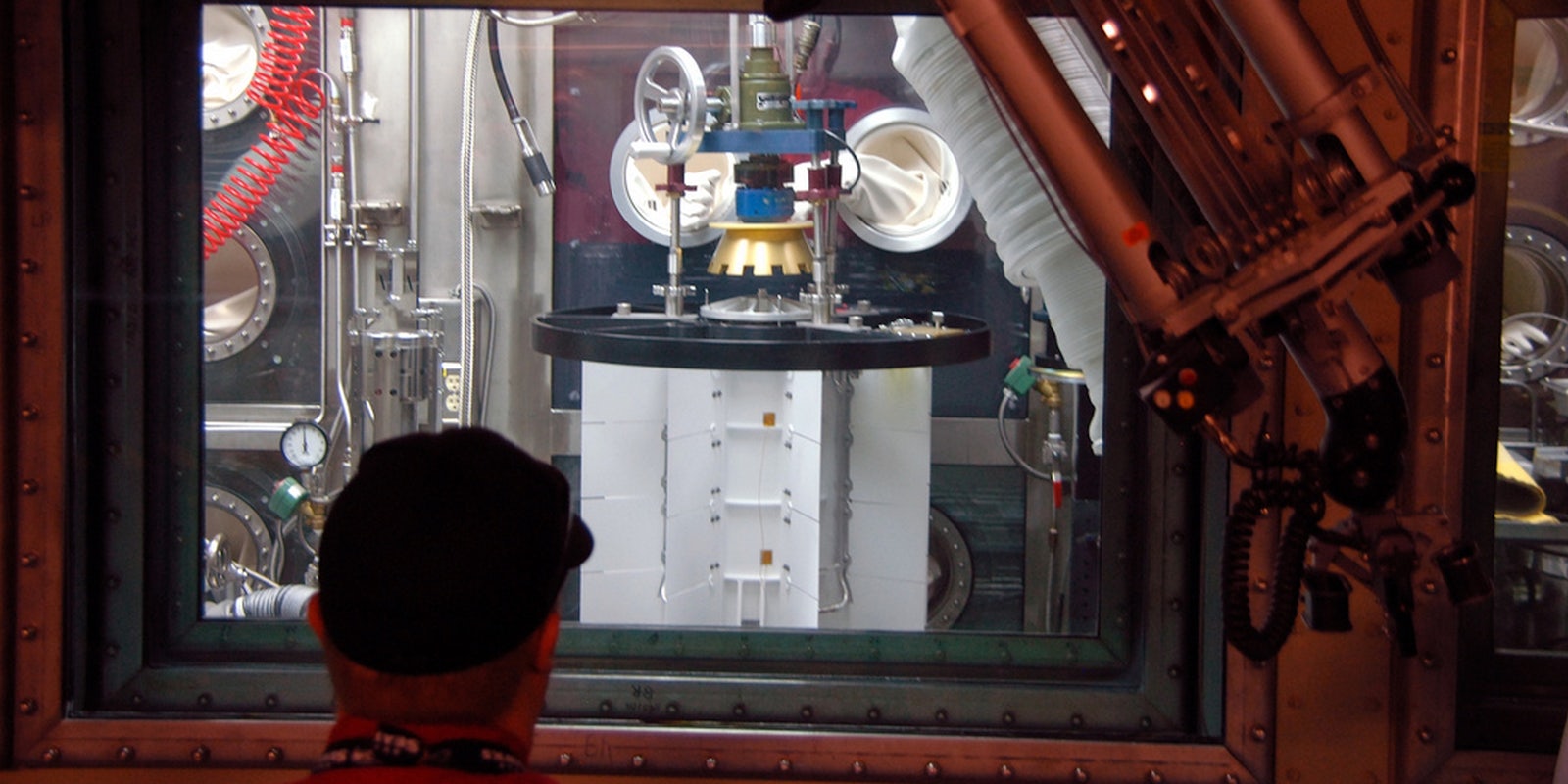
Cory Thuen worked for Battelle Energy Alliance, a company that operates the Idaho National Laboratory (INL) for the U.S. Department of Energy. In 2009, he was part of the Battelle team hired to develop “Sophia,” a tool to detect and arrest aberrations on INL’s network.
In 2012, Battelle made the decision to license Sophia to operators of industrial control systems and Supervisory Control and Data Acquisition (SCADA) systems. (The Stuxnet virus was designed to affect SCADA systems.)
Since Battelle lacked a department devoted to leveraging its products, it sent the process out for bids. Thuen left Battelle to start Southfork Security so he could bid on commercializing Sophia. However, after submitting a bid early this year, Southfork withdrew it. Afterward, Southfork began marketing “Visdom,” its own monitoring product, promising to make the software open source.
Battelle filed a complaint alleging Southfork was guilty of copyright infringement, trade secret theft, and breach of contract, and requested a temporary restraining order to keep Thuen’s company from releasing Visdom.
Why were Battelle’s claims strong enough to merit a no-notice restraining order? Judge Winmill explained, writing “The court finds it significant that defendants are self-described hackers, who say, ‘We like hacking things and we don’t want to stop.’”
Missing the forest for the trees, the judge also wrote, “The defendants have identified themselves as hackers. A well-known characteristic of hackers is that they cover their tracks.”
Admitting that having the defendant’s data copied was “a serious invasion of privacy,” the judge rationalized it by playing the hacker card. Because Thuen and his employees are self-described hackers, Judge Winmill said Southfork must have the “necessary computer skills and intent to simultaneously release the code publicly and conceal their role in act.”
In Thuen’s “Declaration” (PDF), he attempted to educate the court on what being a hacker means.
“As a cybersecurity professional, I am aware of, and possess ability for, many ‘hacking’ techniques that may be used in illegal ways, but I put them to use improving my customers’ security. In other words, I’m much like a locksmith who possesses the ability to pick a lock and uses his knowledge to help as a contributing member of society.”
Thuen told The Daily Dot that Battelle was being disingenuous with its charges.
“The misuse of the term ‘hacker’ is a common problem that people in our industry (i.e. the good guys) have had trouble with in the past,” Thuen said. “The real problem, in this case, is that Battelle is my former employer and knows exactly what I mean by ‘hacker’ because they paid me to do that very job for over three years. Misrepresenting the term to the judge is litigious bullying, plain and simple.”
The subtext of the judge’s ruling seems to be that a “hacker,” despite any evidence to the contrary, is a criminal, and that criminals should be presumed guilty until proven innocent.
We have reached out to Battelle for comment but have not received a response.
H/T Computerworld | Photo by Idaho National Laboratory/Flickr