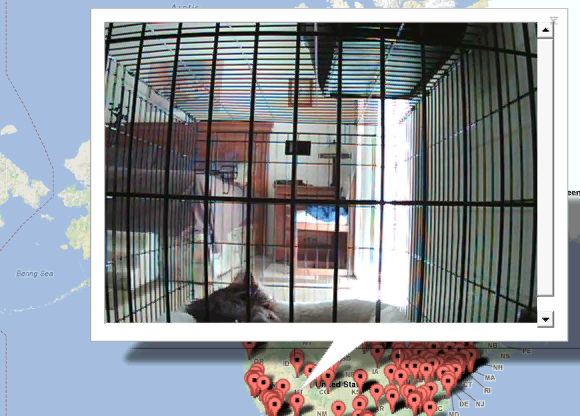
Have you ever wondered what a baby in British Columbia is up to on a Tuesday afternoon? Or whether the snow lifts at New York’s Mohawk Mountain are packed with people?
Well thanks to a software loophole in a line of TRENDnet Internet security cameras, you can.
The live feeds of more than 300 cameras around the world—including countries like South Korea, Colombia, and Israel—are accessible thanks to a new Twitter account and Google Maps-powered application that highlight links to unprotected TRENDnet cameras.
The software flaw was discovered a year ago by blogger console cowboy. In February 2012, the Torrance, Calif., based company offered a free downloadable firmware update to address the bug.
“Only select cameras purchased between April of 2010 and the present may be affected and require a firmware update,” the company stated. “18 camera models have been identified.”
The company also ceased production of the affected security cameras last year “and pulled any remaining cameras from store shelves,” The Verge reported.
At this time it is unclear why so many cameras are still spilling their live feeds onto the Web. Security blogger Ms. Smith of Network World believes these 300 or so cameras have not been updated with the new firmware.
“TRENDnet is doing everything it can to notify all TRENDnet IP camera users to update the critical security firmware on affected cameras,” TRENDnet IT Director Brian Chu told Network World. “Obviously, it is an ongoing project. We appreciate your help in notifying TRENDnet IP camera users.”
Photo via @trendnetexposed/Twitter
