The internet is all fun and games—until it’s not. Contracting malware can ruin more than your day. It can destroy your files and give criminals all types of personal information about you—and even take over control of your device, snap pictures of you, and more.
While there are plenty of ways to protect yourself against malware, it remains a widespread problem, affecting all types of devices around the world. Here’s a brief rundown of everything you need to know about malware and some of the easiest ways to protect yourself.
What is malware?
Malware, short for “malicious software,” is the term used for any program that performs harmful actions on a computer, smartphone or other devices. Malware can perform a variety of functions on the targeted device without the user’s consent. This can include stealing, destroying, or tampering information; spying on users; or hijacking the computer’s functionality to conduct malicious activities against other targets.
Malware can be embedded in different file formats, including executables, scripts, and macro-embedded documents.
What are the different types of malware?
Based on their behavior, most malware falls within one or more of the following categories:
- Virus: Any program that performs malicious activity on the infected computer, such as deleting files, draining memory on the hard disk, and corrupting data
- Worm: A type of malware that is designed to replicate itself across a network and propagate to other computers
- Trojan: A virus that is disguised as a legitimate program but performs malicious activity after being installed
- Spyware: A type of malware that steals information from the infected computer and sends them to a remote location
- Adware: Software that is installed without the user’s consent in order to display ads when they connect to the internet
- Browser hijacker: A type of malware that modifies the behavior of your browser to alter the content of pages, redirect you to other locations, or perform other malicious operations
- Rootkit: A malware that gains administrative access to an infected device and uses it to cause harm
Some programs may not be malware but manifest malware-like behavior. For example, a Windows 10 upgrade stealthily downloaded itself on machines running older versions of the operating system.
How does a device get infected with malware?
Cybercriminals use various ways to install malware on target computers. One of the most common methods is phishing scams, in which attackers send an email containing a malware-infected attachment to the target and name it something that’s difficult to resist clicking on.
READ MORE:
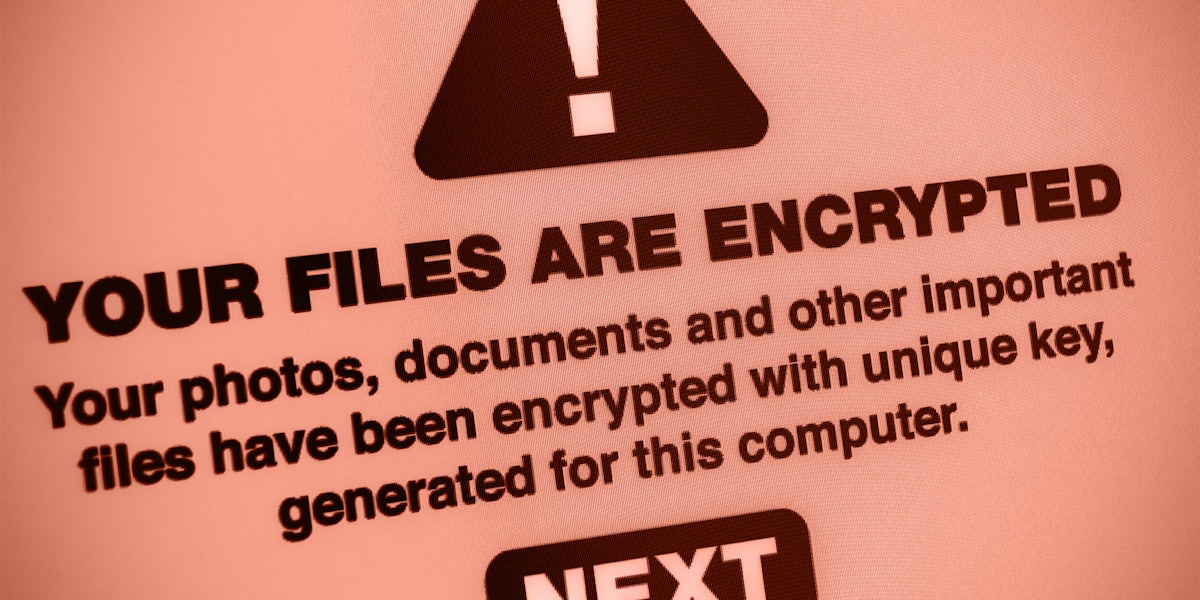
- How to protect yourself against ransomware
- The best free VPN to maintain your privacy online
- How to encrypt an iPhone in seconds
USB drives and other removable media are also a popular medium for distributing malware. Baiting, a famous social engineering attack, involves putting malware-infected thumb drives and DVDs with alluring labels in random (or targeted) locations to lure victims into picking them up and connecting them to their computers.
Resourceful hackers use more sophisticated methods. Malvertising is an attack that involves embedding malware in third-party ads that appear on websites. Other hackers stage watering hole attacks, in which they hack a website frequented and trusted by their targets, and use them to send malware to the visitors of the website.
How to protect yourself against malware
The most common way to prevent malware from finding its way into your computer is to install an anti-malware solution. Most operating systems come with built-in anti-malware functionality, but there are also some good free and paid third-party options out there.
Most anti-malware solutions have a database containing the digital fingerprint of all known malware types, which they compare against all files that are downloaded and executed on your computer to detect and block malware.
While this approach is effective against most malware, it’s not enough, especially as malware developers are employing new techniques to circumvent signature-based detection techniques. Some newer endpoint solutions use behavior-based detection and other techniques to outsmart and block malware.
However, no technology has yet been able to replace common sense and general cyberhygiene. Cybercriminals largely rely on user error to spread malware. Keeping your system and software up to date, avoiding attachments and links in suspicious emails, or refusing to downloaing files from unknown websites are some of the most important measures that will protect you against malware.
Ben Dickson is a software engineer and the founder of TechTalks. Follow his tweets at @bendee983 and his updates on Facebook.