Monday’s report from the French paper Le Monde didn’t just show the world that the National Security Agency spies on French citizens.
It offered a little more insight into the NSA’s controversial, mysterious program called PRISM by releasing an additional three slides from the agency’s PowerPoint presentation on the subject.
PRISM was the second program made public after being leaked by former NSA contractor Edward Snowden, and few have so captured the public’s imagination. Marked with an ominous prism logo, NSA’s slides described the program as offering “direct access” to nine American companies’ users’ files, including Google, Facebook, and Yahoo. Those companies fiercely responded with very carefully tailored rebuttals that said they hadn’t willingly engaged in any big government spy program, with the very notable exception of when they were compelled to by secret law.
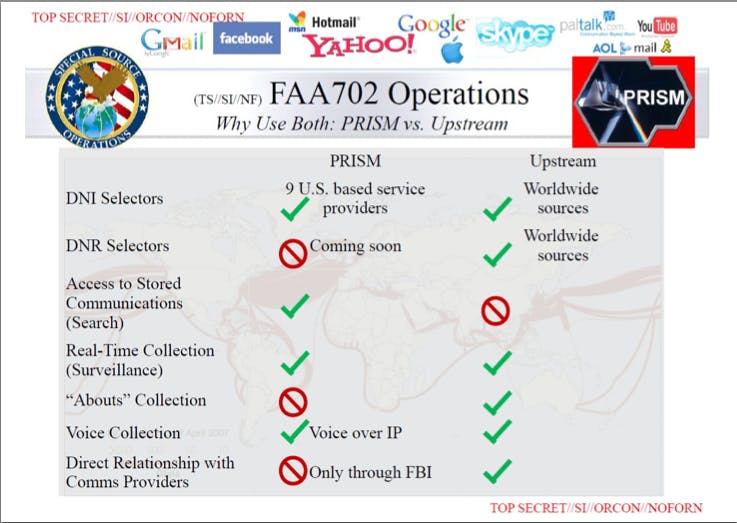
The first of the three new slides shows that the NSA makes it regular practice to use PRISM in conjunction with upstream collection—the process where the agency gets Internet information as it travels through major communications hubs. Together, the two processes can compile a remarkable amount of information on a target: old communications and new, and what the target’s doing online in real-time. “DNI selectors” refers to keywords the NSA can search for—are they using a certain term online today? Does that word show up in their old Yahoo emails?
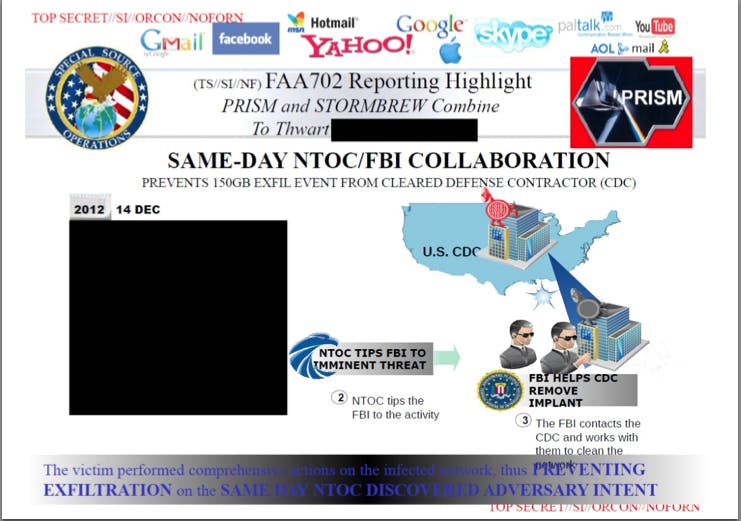
The second appears to show something of a success story. NSA director Keith Alexander has tried to brag about NSA programs catching illegal activity before it happens, though that’s largely been very vague instances of thwarted terrorist attacks that didn’t clearly need NSA intelligence to stop.
On Dec. 14, 2012, the slide says, the NSA Threat Operations Center spied that someone was trying to get 150GB worth of information from a defense contractor, using the combined tools of PRISM and the upstream collection program Stormbrew. NTOC alerted the FBI, which in turn worked with the contractor to stop the attack.
NSA watchdog blog Empty Wheel noted that this is indicative of the fact that, as much as NSA defenders tout the agency’s ability to stop terrorism, it’s far more accomplished at stopping cyberattacks.
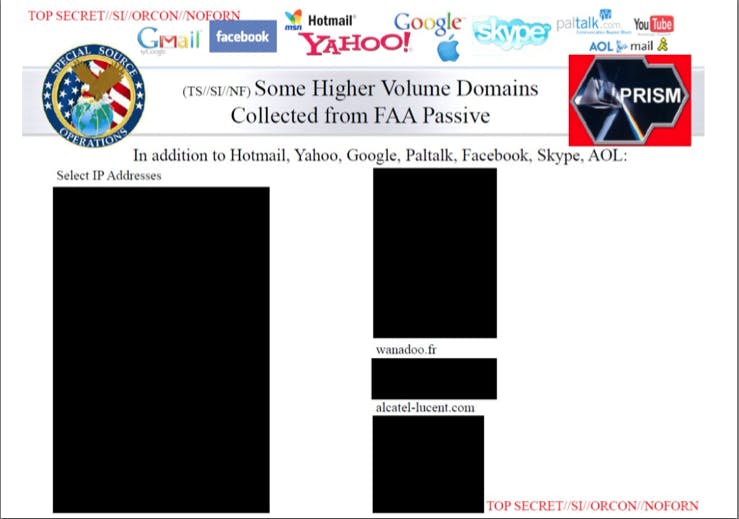
The final slide shows approximately 50 “high volume” domain names that the NSA collected information from. Le Monde notes this refers only to the 30-day period from Jan. 1-30, 2013. The paper redacted nearly all of the domains for fear of interrupting ongoing investigation. Wanadoo, since rebranded as Orange, is an Internet service provider that operates in Europe and the Middle East. Alcatel-Lucent is a French telecommunications company that offers substantial cloud storage services.
Whether the slides released so far explain the program’s full mechanics is still unclear. But it’s safe to say that as recently as this year, it was an active program, one used in conjunction with the ability to search Internet traffic in almost real-time, to track the U.S.’s perceived enemies.
Photo by El Bibliomata/Flickr. Remix by Fernando Alfonso III