Enough spam to warrant a lawsuit isn’t the only nasty thing you can find on LinkedIn.
Dell’s SecureWorks lab says it’s uncovered evidence of a network of fake LinkedIn profiles which, it says, trace to an Iran-based “threat group” known as TG-2889 and were used to spy on targets who use the social business site.
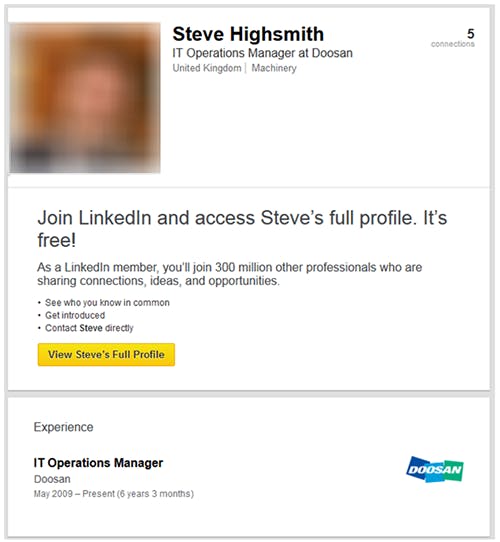
There’s little doubt that the 25 profiles named in the report are fake. They use avatars found elsewhere online, and many details on their resumes are identical to older profiles on the site.
Most appear to be a generic westerner in business who has lots of connections to other users—propped up in part, according to the report, by other fake profiles.
During the course of its study, SecureWorks noted that one profile changed its name, job description, and avatar—but kept the same unique LinkedIn ID, as evidenced at the bottom of each.
Though the fake profiles tend to claim to be westerners, most of their connections are in the Middle East, and a substantial portion of them work in telecommunications, which may be evidence of TG-2889’s ideal target.
“We do have a team dedicated to protecting users from these kinds of risks,” Mary-Katharine Juric, LinkedIn’s corporate communications manager, told the Daily Dot.
Recurring details in the fake resumes, the report found, bear a strong resemblance to a different attack using resumes. Dubbed Operation Cleaver by Cylance, the security firm that discovered it, that attack sent fake resume applications—often using the same phrases and job titles used in these fake LinkedIn profiles—that contained malware. Cylance traced that attack to Iran, and concluded that the Iranian government likely played a role in its execution.
The fake profiles have since been deleted from the site.
Update 12:28pm CT, Oct. 8: Comment from LinkedIn added.
Illustration by Jason Reed