Hackers reportedly managed to penetrate multiple U.S. voting machines in a relatively short period of time at a conference in Las Vegas this week, a cautionary demonstration for people concerned with the integrity and security of American elections.
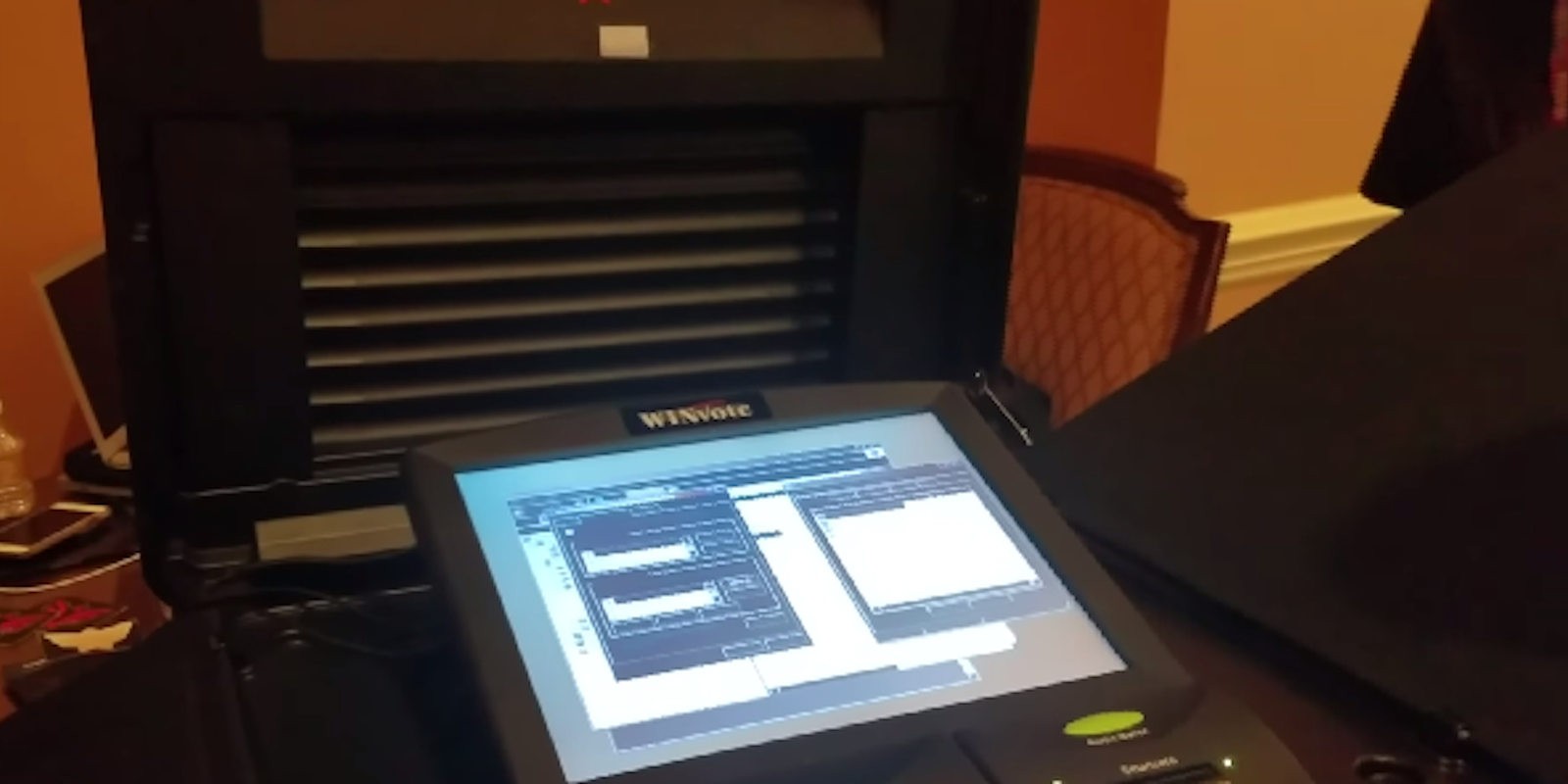
The group of hackers attending the annual DEF CON conference reportedly took just 90 minutes to compromise 30 different voting machines, breaking through different companies’ security measures, including Winvote, Diebold, and Sequoia. In some cases, the machines included external ports that could be used to plug in malware, while others―perhaps more concerning―had poorly secured Wi-Fi connectivity enabled, allowing the hackers to breach the systems remotely.
Jeff Braun, a cybersecurity expert at the University of Chicago, reportedly convinced the DEF CON conference to take up the demonstration, hoping to show whether voting machine companies’ assurances of security could be trusted. After the event concluded, he told the Register that the perils are obvious.
“Without question, our voting systems are weak and susceptible. Thanks to the contributions of the hacker community today, we’ve uncovered even more about exactly how,” Braun said.
“The scary thing is we also know that our foreign adversaries—including Russia, North Korea, Iran—possess the capabilities to hack them too, in the process undermining principles of democracy and threatening our national security.”
Election cybersecurity has been a hot topic in recent months, thanks to the U.S. intelligence community’s broad concurrence that the Russian government attempted to interfere in the presidential election. Specifically, it’s been widely alleged that Russia hacked the Democratic National Committee and the email account of Hillary Clinton’s campaign chairman John Podesta, in an attempt to funnel damaging information about her into the public consciousness.
It’s also been reported that Russian hackers accessed U.S. voting machines in 39 states in the run-up to the election, although there’s no evidence that any votes were changed.
Update 3:58pm CT, Aug. 1: Hackers discovered the records of 654,517 people in an ExpressPoll-5000 electronic voting machine at Voting Village, according to a Gizmodo report.
The records appear to be from people who voted in Shelby County, Tennessee, and contain names, addresses, dates of birth, political party affiliations, whether people voted absentee, and if they were asked to provide ID.
Security researcher Josh Palmer first discovered the database by simply removing the memory card from the voting machine and connecting it to a computer. Palmer told Gizmodo it was not encrypted and didn’t even have a password. The conference quickly confiscated the memory card to protect the more than 650,000 voters whose personal information was left unprotected. If Palmer had the card before an election, he said he could write a script “in seconds” that would make it appear as if all people already cast absentee ballots.