Last week, a 19-year-old British teenager pleaded guilty to running Titanium Stresser, a service that is alleged to have facilitated 1.7 million distributed denial-of-service (DDoS) cyberattacks.
Adam Mudd’s website, which he designed as a 15-year-old, earned him somewhere in excess of $385,000. It was marketed under disclaimer as a legitimate IP stresser, a tool for testing networks and servers. Titanium Stresser, though, was actually one popular vendor in a fledgling industry: DDoS for hire.
‘Booter’ services, as they are also known, advertise openly and operate as a normal businesses. One quick web search throws up hundreds of sites offering DDoS services for as little as $20. The Daily Dot came across the below booter website, Network Stresser.
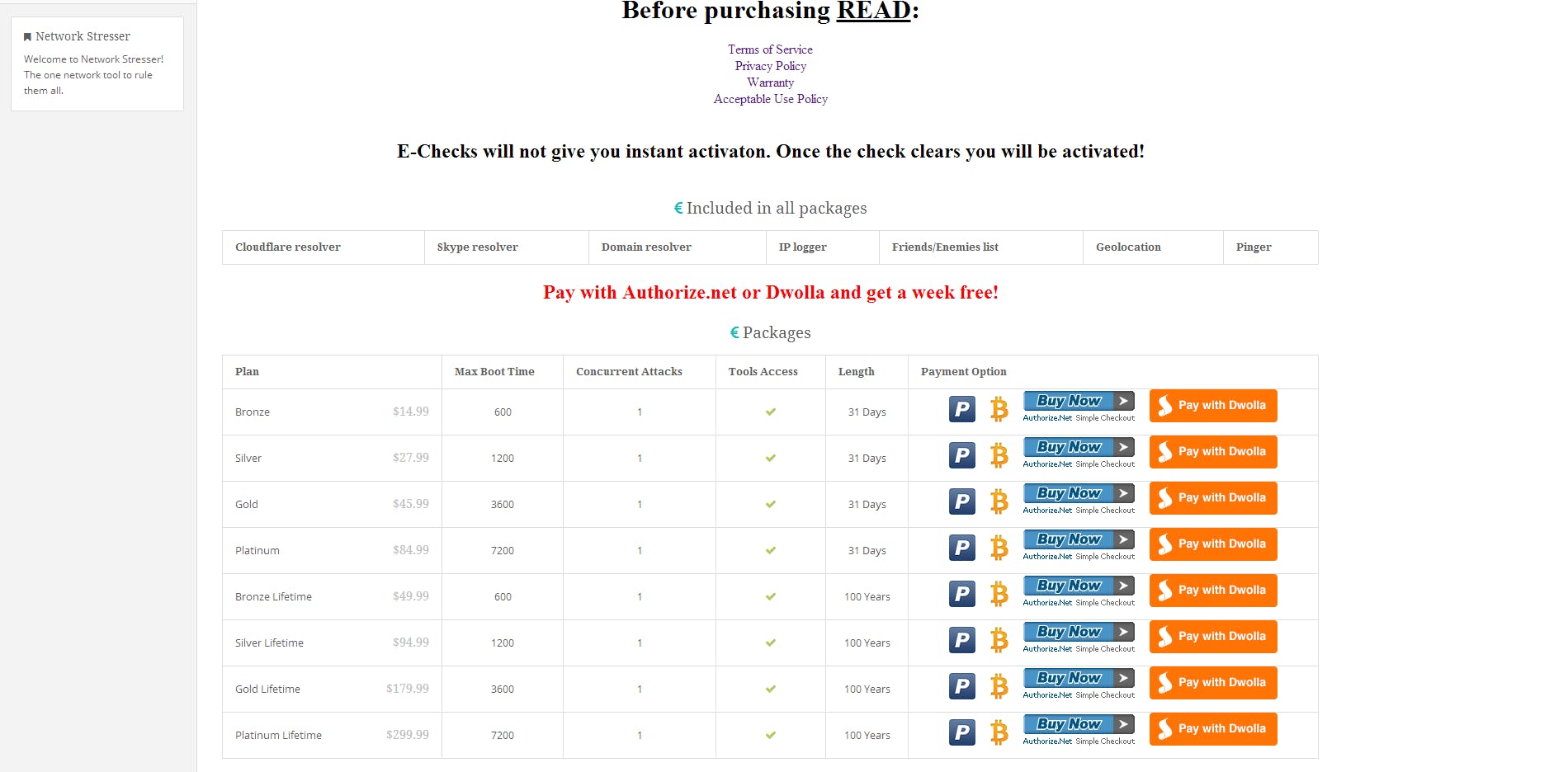
It offers a full range of subscription offers, ranging from the $14.99 Bronze package to the $299.99 Platinum Lifetime offering:
Price varies dependent on a number of factors, such as the intensity of the attack required and how long it should be sustained. Still, it can cost less than a monthly gym membership fee and, after an effortless transaction via PayPal, you’re ready to wreak havoc online.
Without getting too technical, a DDoS attack is a simple and seriously effective way to knock a website offline for hours by blitzing it with heavy traffic loads or junk data.
Often the target website’s application resources are overwhelmed and bandwidth drops out, ultimately forcing the site to crash—a denial of service. The attack is distributed in the sense that the attacker utilizes a coordinated network of malware-infected zombie systems or nodes (sometimes called a botnet) to shoot requests at the target website. In this sense, the attack appears to originate from thousands of IP-addresses and computer networks.
This type of debilitating cyberattack made the news in a big way in October, when a major DDoS attack took down a company called Dyn. Dyn manage the servers for some well known websites and social networks, like Twitter, Spotify, Sony Playstation, Netflix and Reddit. When Dyn dropped out, the sites became effectively inaccessible.
A DDoS can be vicious and the damage caused costs businesses dearly. A recent study commissioned by Neustar found that 82 percent of mid- to large sized organizations surveyed had suffered a DDoS attack. Further, the financial impact of a peak time attack could cost businesses between $100,000 to $250,000 per hour.
The size of the attacks being leveled at these companies is increasing, too, usually measured in bits-per-second and packets-per-second. More than half of the companies surveyed had to cope with attacks of up to 5Gb-per-second. Network Stresser, a highly rated DDoS-for-hire site, offers attacks of up to 120GB-per-second in combined power.
In the wake of the Dyn DDoS, it emerged that attackers had commanded a massive botnet of compromised internet-connected devices—chaos, caused by vulnerable webcams and DVRs. In Neustar’s survey, 80 percent of the companies attacked had adopted Internet of Things (IoT) devices as part of their infrastructure.
As far as cybersecurity experts are concerned, IoT devices with weak security protocols are the botnet armies of the future, ready to level governments and corporations in just a few clicks and for some pocket change.