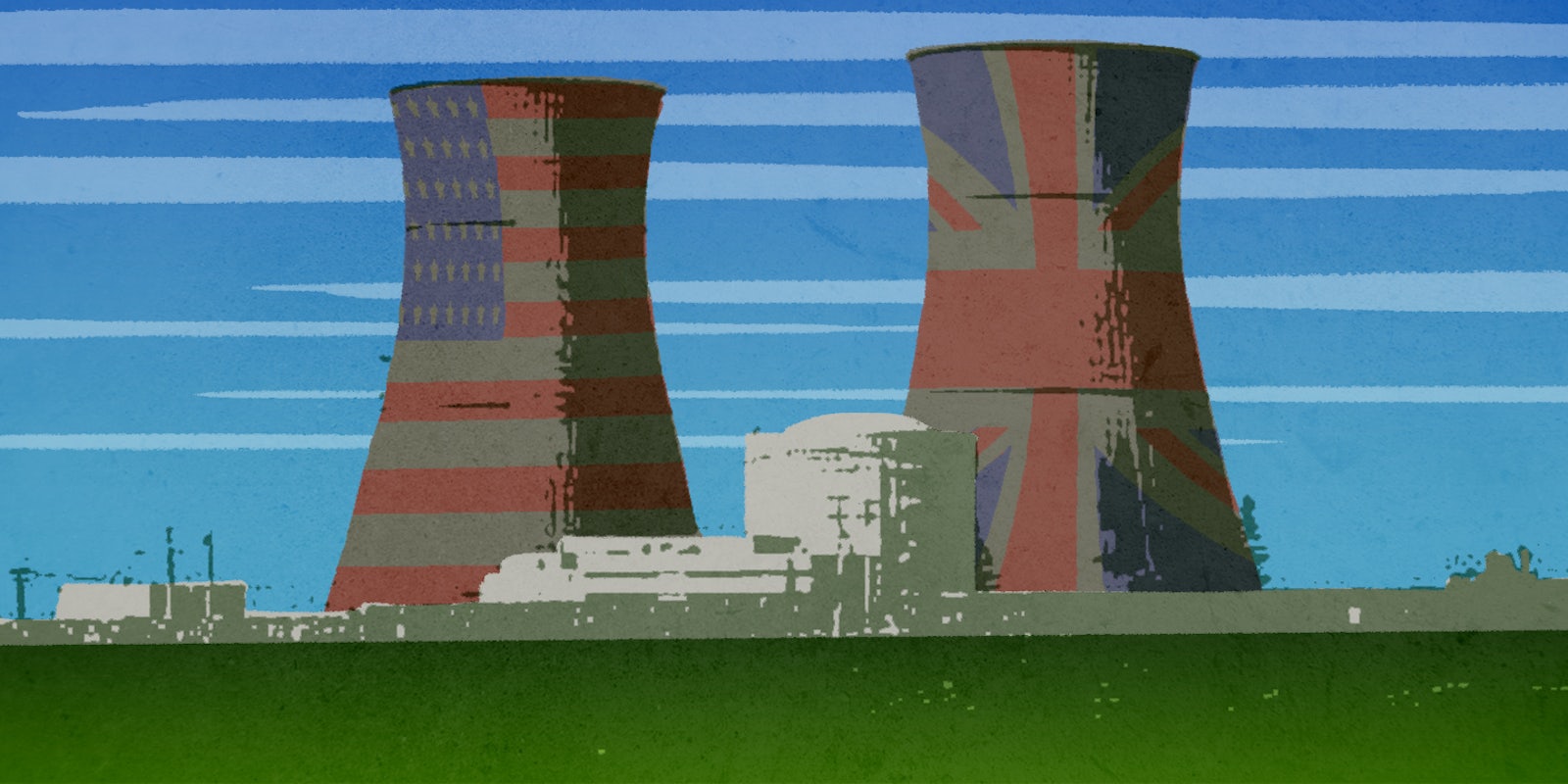
The United States and the United Kingdom will jointly test their nuclear power plants’ resilience against cyberattacks in a simulated digital attack on nuclear infrastructure next year.
“The exercise will simulate a cyberattack on nuclear power supplies to see how Britain and America can work together in the event of such a security threat,” the British government said in a statement on March 31.
The tests will build on last year’s Operation Resilient Shield, in which both governments assessed how vulnerable their financial networks were to digital infiltration and sabotage.
The British foreign and energy ministries did not respond to requests for details about the exercise. The White House also did not respond to a request for additional information.
The announcement of the U.S.–U.K. exercise came on the second day of the 2016 Nuclear Security Summit, which brought together the leaders of many nations in Washington to discussing looming threats like containment, arms control, and cybersecurity.
As hackers become more sophisticated and nation-states pour more resources into cyber armies, the specter of electronic attacks on the computers controlling nuclear plants has become an increasingly pressing concern.
Cyberattacks on power plants and other critical infrastructure are seen as an inevitable preliminary step in the next major kinetic war, because cutting off power to a region hamstrings both first responders and technologically dependent defense forces. But nuclear power facilities present special vulnerabilities due to the potential consequences of a successful attack. A sophisticated intrusion could cause them to malfunction and melt down, dealing catastrophic damage to the surrounding area if the proper containment mechanisms are not in place.
The first confirmed case of a cyberattack disabling a power plant occurred on Dec. 23, when malware linked to Russian hacker group shut down power to a vast swath of western Ukraine. The Russian government denied responsibility for the attack, and outside experts agreed that the attack bore the hallmarks of a rogue actor.
The United States and Israel pioneered the art of the destructive cyberattack when they aimed the virus dubbed Stuxnet at Iranian nuclear facilities in 2009 and 2010, eventually disabling around one-fifth of Iran’s nuclear centrifuges.
Cyberwarfare is a largely uncharted area of international relations, and there are few clear rules about what targets are off-limits during a time of war, much less what constitutes an act of war in cyberspace. U.S. and U.K. leaders are likely concerned that the relatively untamed legal landscape of cyberspace has created a space for low-cost, hard-to-trace, and incredibly destructive cyberattacks on nuclear infrastructure.
The United States produces the most nuclear energy of any country, far outpacing the United Kingdom and the other leading producers.