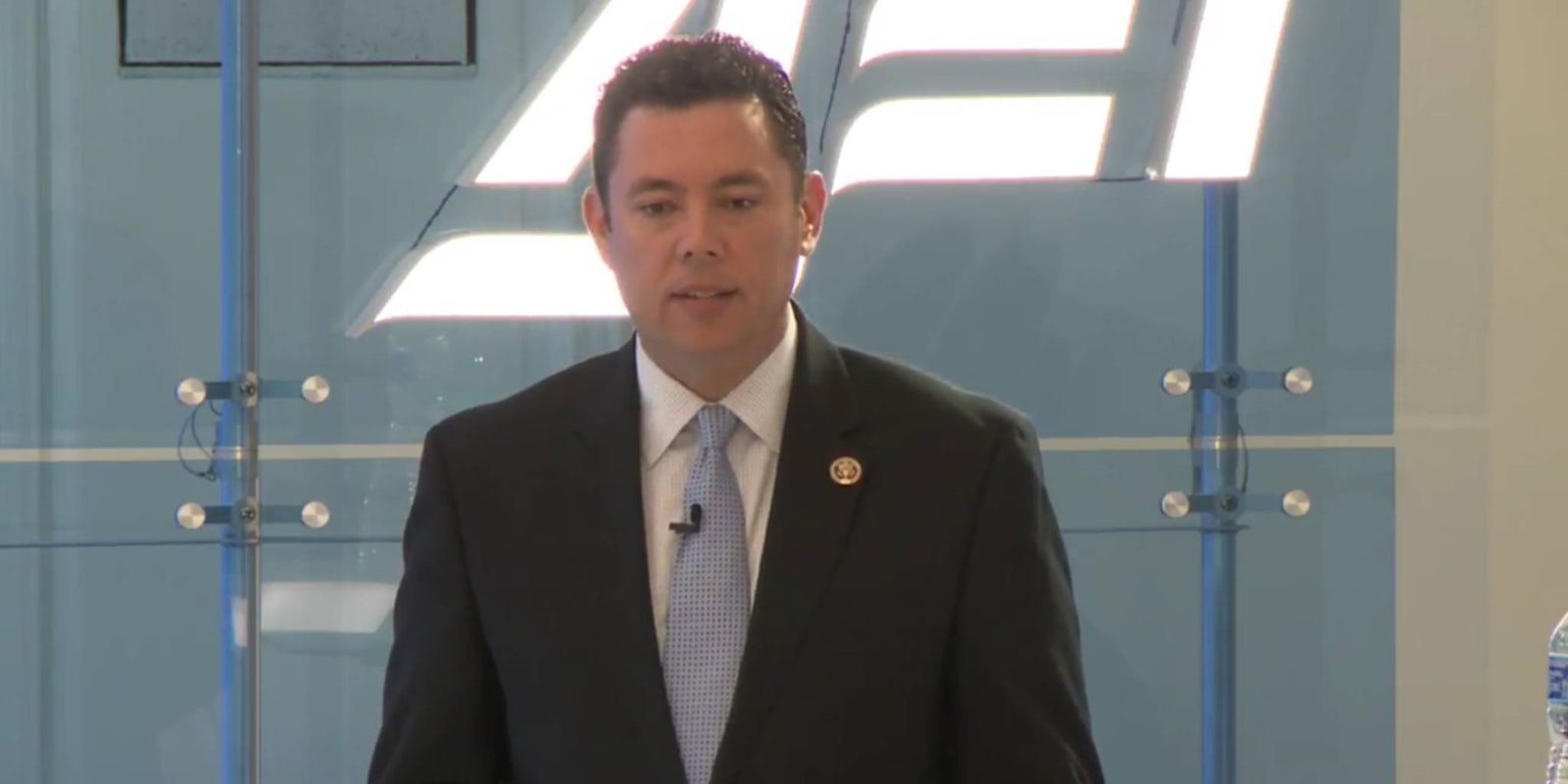
A cascade of failures led to the one of the most successful hacks ever against the U.S. government, Rep. Jason Chaffetz (R-Utah) argued in a speech on Wednesday morning, echoing the findings of a new congressional report.
“The government of the United States of America has never before been more vulnerable to cyberattacks,” according to a 241-page report commissioned by the U.S. House Oversight & Government Reform Committee, which Chaffetz chairs, and released on Wednesday. “No agency appears safe.”
The hack against the U.S. Office of Personnel Management, which resulted in the theft of personnel files of 4.2 million government employees and background information on 21.5 million individuals, was preventable had the agency acted more responsibly, the committee’s investigation found.
https://twitter.com/HowellONeill/status/773495586570039296
The agency had been warned since 2005 by its inspector general about serious vulnerabilities to hackers. From 2007 and on, the reports grew more dire about worsening information security “weaknesses” at OPM.
The investigation also found that OPM has been under consistent attack since 2012.
The report offers the most exhaustive timeline of the incident, publicly revealed in June 2015, including new details on the technical facts of the attack as well as the play-by-play of how and when the agency found out about the breach in 2014. The Department of Homeland Security told OPM in 2014 that the attack was underway.
But there are major blindspots due in large part to problems with OPM’s cybersecurity. In particular, OPM and the investigators did not figure out how the first attacker, called Hacker X1, accessed their networks because OPM did not monitor their own networks. They missed the second attacker, Hacker X2, for months longer.
“This is in large part due to sloppy cyber hygiene and inadequate security technologies that left OPM with reduced visibility into the traffic on its systems,” the report charged. “The data breach by Hacker X1 in 2014 should have sounded a high level, multi-agency national security alarm that a sophisticated, persistent actor was seeking to access OPM’s highest-value data. It wasn’t until April 15, 2015, that the OPM identified the first indicator that its systems were compromised by Hacker X2.”
A litany of mistakes allowed other hackers to continue to work even after that original notification of a breach.
“The agency’s senior leadership failed to fully comprehend the extent of the compromise, allowing the hackers to remove manuals and other sensitive materials that essentially provided a roadmap to the OPM IT environment and key users for potential compromise,” the report reads.
The report does not lay blame on a specific attacker. However, the incident triggered a flurry of diplomatic activity between the U.S. and China, which was widely blamed for carrying out the attack.
Chaffetz also charged that OPM was slow to secure their systems and attempted to keep the breach quiet. An OPM staffer is reported to have said there is “no need” to “notify the public” of the attack despite it affecting tens of millions of Americans.
The report, and Chaffetz in particular, praised the new acting director of OPM, Beth Cobert, for improving OPM’s cybersecurity in the wake of the attack. Cobert wrote a blog post published on Wednesday in response to the congressional report.
“While we disagree with many aspects of the report, we welcome the committee’s recognition of OPM’s swift response to the cybersecurity intrusions and its acknowledgment of our progress in strengthening our cybersecurity policies, and processes,” she wrote. “We also appreciate the panel’s willingness to work with us on these important issues and find many of the final recommendations to be useful for OPM and the federal government at-large.”
Democratic lawmakers on the committee said the report omitted a key element of the environment that made OPM vulnerable to hacker: federal contractors.
“The Republican staff report fails to adequately address federal contractors and their role in cybersecurity,” according to the Democrats. “The most significant deficiency uncovered during the committee’s investigation was the finding that federal cybersecurity is intertwined with government contractors, and that cyber requirements for government contractors are inadequate.”
Contact the author: Patrick Howell O’Neill, pat@dailydot.com