Throwback Thursday means something a little different to Anonymous today. Meet #OpThrowback.
The first thing Anonymous’ #OpThrowback accomplished was getting its Twitter account suspended. After that initial stumble, however, they’ve gone on to what Anonymous would call serial success and the government would call “possibly indictable offenses.”
We’re talking about DDoS: distributed denial of service attacks. It’s a relatively old-fashioned form of digital attack—simple, if not elegant. A large group of computers from all different locations (“distributed”) is programmed to call up a particular website over and over. The relentless demand for the website crashes it. DDoS attacks typically neither last very long nor do permanent damage, but they do make the target website unavailable to the public for however long the attack lasts, assuming enough computers are involved in the attack in the first place. The more computers, the stronger the attack and the less likely the website will stay up. It embarrasses the companies to whom the sites belong, and also their web hosts, but it is not technically a hack, in that the databases are not accessed, passwords are not cracked, and nobody gets “inside” the site itself. It’s more like ringing the front and back doorbells and the phone at the same time, over and over.
#OpThrowback is a throwback: to OpPayback, the Anonymous operation that DDoS’d Amazon, Paypal, Visa, Mastercard, and others when they attacked online piracy and blocked donations to WikiLeaks. The Paypal 14, who were arrested for allegedly participating in OpPayback, go back to court today. The press release for OpThrowback says, “The DDoS attacks will be a powerful show of force to take a careful stand in opposition to the crimes against freedom that hold us down with each passing day. The United States decided to shake our nest, and for that, we will sting back.”
We spoke via Skype to Okapi, a supporter of #OpThrowback, about the goals and actions of the operation.
Is OpThrowback connected with the Paypal 14?
We aren’t in connection with ANY indicted Anons on this one and would like to make sure they are not seen as responsible for anything we do because the Paypal14 are already in trouble for what they do. Any declaration of alliance to them would be highly detrimental to their legal case. We aren’t out to hurt any of our allies or … comrades in arms, etc. We support them.
How did the operation start? You said originally you wouldn’t launch until Nov. 5, and yet you’ve taken down the sites of the American Nazi Party, the NSA, and Dianne Feinstein so far. Other targets announced include Verizon, AT&T, and the FBI, as well as some apparently random government contractors.
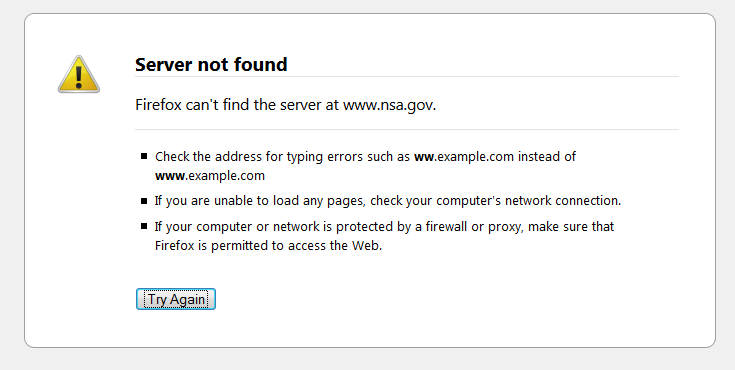
Screencap via Imgur
The American Nazi Party’s views of discrimination and hatred are entirely against what Anonymous stands for. It was a very useful place to start testing our DDoS capabilities. DDoS is a quick, dirty way to make a dramatic point. We haven’t decided on any conclusion date to the DDoS attacks, but it’s very possible we will take action up to and including the 5th of November.
This operation came about during talks in #OpNSA. Because #OpNSA has publicly stated it does not want to use malicious cyber attacks, we decided to form our own operation. We are like the edgier, more dangerous cousin of that peaceful op. The main motivation is to strike back against the government and corporations which supported it during the whole PRISM fiasco.
We will be targeting any corporations, contractors, agencies, and individuals that supported PRISM and other clandestine spying operations on the people of the world. This definitely falls under the banner of AntiSecurity (AntiSec). Not only did PRISM spy on the people of the U.S., but it took aim at multiple world leaders and multiple countries. It was a highly despicable act that must be met with action. Consequences will never be the same.
Given the number of Anons in custody or facing charges for DDoS attacks, what precautions are you taking against arrest? I see you are releasing the target list only in IRC now, rather than on Twitter.
We take security very seriously and have gone to great lengths to inform anons joining us that they should not take any action unless they know how to secure themselves. There are risks, but we feel that our security is sufficient to stand up to those risks and be successful in this campaign.
We all realise that as Anonymous, it is our duty to take firm action when someone infringes on our privacy or our rights.
Why is Anonymous Indonesia involved?
I noticed others Anons had taken action against Indonesian websites in the name of #OperationThrowback. Because we, as Anonymous, are very loose knit and anyone can lay claim to an operation with any action, it’s not our place to say someone isn’t part of our op. The operation is an anti-censorship, pro privacy operation which is taking action against governments because of their totalitarian stance.
So to the Anons out there taking action against their government sites, I say, “well done.”
Our allies in arms are taking action in ways we never even called for. Syria article up today, websites down today. Anonymous is on a roll.
— Okapi (@anonokapi) October 29, 2013
With Throwback, we are taking aim at the U.S. Government and its contractors for their own oppressive acts. Anonymous is comprised of every person out there who decides to act under the banner of Anonymous. The individuals from Operation Throwback could be anywhere in the world. We aren’t concerned with their location, but rather what they do to help the cause. And of course, anybody could be Anonymous. It could be the garbage man across the street, it could be your editors, it could be every person in every corner of the world.
What Throwback seeks to accomplish is to tell the government and its contractors that we are unstoppable and that they will lose the game.
Image via Anonymous Shocking Events/Facebook
