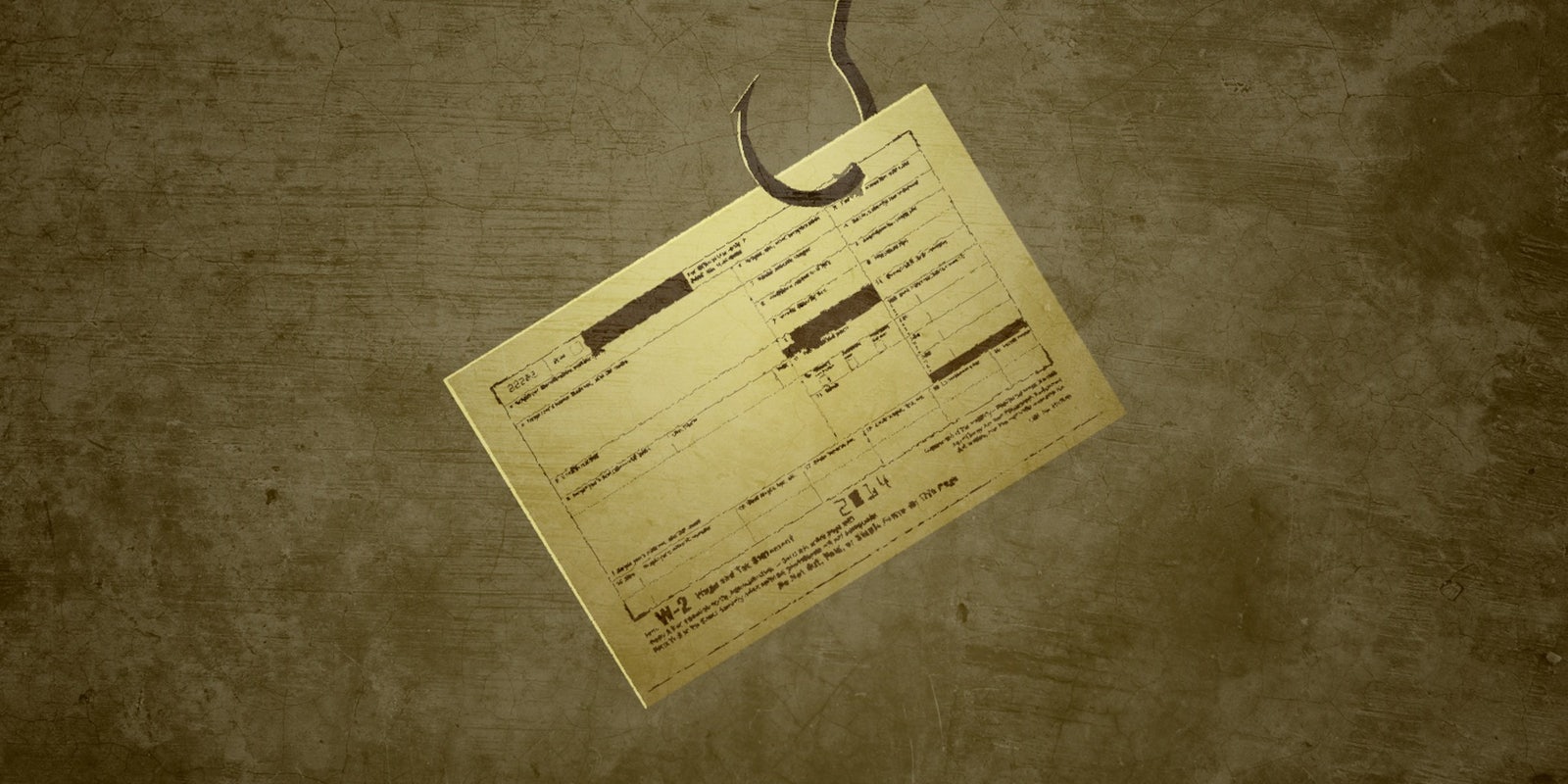
It’s bad enough to have your private details stolen by scammers. But it’s far more painful when it happens to a payroll services vendor, resulting in all of their clients’ employees’ personal information being emailed to criminals.
Sadly, that is exactly what happened to Alpha Payroll Services LLC, a division of Alpha Card Services.
On April 29, external counsel for the firm notified the New Hampshire Attorney General’s Office that an employee had fallen for a phishing scam targeting clients’ 2015 employee W-2 information.
W-2 statements include an employee’s full name, postal address, Social Security number, wage and salary information, how much an employer deducted in taxes, and other employer information. W-2 data can be used for tax refund fraud and identity theft, making it very desirable information in criminal circles.
The letter, signed by Blaine Kimrey of the law firm Vedder Price, explains, in part:
On or about March 1 or 2, an Alpha Payroll employee responded to a “phishing” scam email in which the sender represented himself or herself to be the CEO of Alpha Payroll and disguised his or her email address as that of the CEO. In this email, the fraudster requested copies of all the 2015 W-2 forms produced by Alpha Payroll on behalf of its customers.
Such scams, also known as “Business Email Compromise,” have been a significant problem this year. A tally on DataBreaches.net currently indicates that 100 such incidents have been reported so far this year.
In the most basic sense, email phishing schemes work by sending a target an email that appears to come from someone she knows with an infected link that will allow attackers to access the target’s machine or network. Or, as appears to be true in the case of APS, the email itself is infected.
Casual inspection of the email request that appeared to come from APS’s CEO probably did not raise any flags. As Kimrey explains in the letter:
As a result of hidden commands embedded within the email by the sender, upon responding to the email, the reply message was rerouted and sent to the email account of the third-party sender.
APS, which is headquartered in Trevose, Pennsylvania, and has offices in California and New Jersey, first became aware of a problem on or about April 8, when a customer contacted them to report fraudulent tax returns filed under the identity of a New Hampshire resident, according to the letter:
Upon notice from a customer of the filing of fraudulent tax returns under employee Social Security numbers on or about April 8, 2016, Alpha Payroll immediately launched an investigation to determine whether a security incident had occurred. Although no definitive proof exists at this time connecting the fraudulent returns to the phishing email response of the Alpha Payroll employee, the investigation that began on April 8, 2016, uncovered the inadvertent release.
In response to the discovery, APS took several steps, according to the letter, including terminating the employee, hiring experts to assist with its investigation, and contacting law enforcement, “including the Criminal Investigation Division of the IRS and the FBI, regarding the incident.”
APS’s response also included retraining all employees on phishing schemes and the need to confirm the legitimacy of any email requests. The firm is also offering those affected by the scam one year of identity-protection services through AllClear ID.
The notification letter does not indicate how many individuals in total are being notified of the incident, and APS does not provide any list of clients in the notification to the New Hampshire Attorney General.
Neither APS nor APS’s law firm responded to emails and voicemails requesting comment and further details.
Dissent Doe is the pseudonym of a privacy advocate who reports on privacy issues and data security breaches on PogoWasRight.org and DataBreaches.net. Her research on breaches has fueled resources such as DataLossDB.org and InfoisBeautiful, and it has served as the basis for a number of investigations by the Federal Trade Commission.