In light of the Heartbleed bug, there’s been an awful lot of talk about Internet security. Although it’s a pressing issue for everyone regardless of gender, it’s especially urgent for women, who are often targeted by trolls, stalkers, hackers, and all-around creeps on a near-daily basis.
As a high-profile female investigative blogger who’s been named one of Forbes’ top 25 “Web celebs,” Violet Blue has experienced her fair share of trolling and online harassment. But as one of the Internet’s foremost sex and tech journalists, she’s also devoted her nearly two-decade-long career to covering these issues firsthand. The author of dozens of books and proprietor of the popular sex/tech blog Tiny Nibbles, Blue has been a columnist for the San Francisco Chronicle, CBS, and Znet, where she broke the story about the Snapchat security flaw that led to its user database being exposed. For the past few years, she’s also been on the revenge porn beat, co-founding and serving on the advisory board for the privacy rights non-profit Without My Consent.
Now, she’s sharing her wisdom with the rest of us in The Smart Girl’s Guide to Privacy, a practical guide for women to protect themselves against hackers, spammers, and creeps online. Written in plain, user-friendly language and covering everything from revenge porn to identity theft to online dating, The Smart Girl’s Guide to Privacy is specifically geared toward women and other vulnerable members of the online population, who need guidance navigating the murky, often treacherous waters of the Internet. The Daily Dot recently talked to Blue about Heartbleed, Tinder, revenge porn, and why we shouldn’t have to Just Say No to sexting.
This interview has been lightly condensed and edited.
Can you tell me a little bit about why you decided to write this book?
There was a big, big hole missing that I could see in terms of writing about privacy practices. I’ve been covering hacking and computer crimes for three or four years for major outlets like CBS, so I see the crimes happen from the perspective of the people that work at the company that’s been hacked and also from the perspective of the criminals themselves. What was really missing was how this affects the consumer. Once I started to address this in my work, I saw no one has been explaining this to regular Internet users. I also saw there weren’t any privacy guides out there that were in normal language, language that wasn’t technical and didn’t require you to learn any programming. And actually, something like Privacy for Dummies hasn’t been updated since 2002, so there’s a serious void [in the market].
Can you talk a little bit about why this is the smart girl’s guide to privacy, and not the smart man or person’s guide to privacy? Why do women have to think about these issues more than men do?
The book is addressed to all genders and all orientations. There’s information everyone can use. But I found the people who were disproportionately affected were women and LGBTQ people because we’re targets online, and a lot of the systems that we use were designed by people who are not aware of target and non-target status. They have huge privacy holes in them and they weren’t being designed in mind with the fact that people using them are going to be targeted. So, I wanted to address what I see as the biggest weak spots in privacy, which is the way it affects women.
Women are so incredibly targeted online, with stalking and revenge porn and being hacked. I wanted to go to the extremes of addressing every crazy thing that’s done when the biggest targets are gone after online, because that way I felt I could get the strongest information out there and cover a lot of topics that I don’t think a lot of people in privacy groups are covering.
In the book, you talk about how LGBTQ people are targets online, but it’s not overly emphasized. Do LGBTQ people face unique privacy issues online that hetero men or women don’t?
I believe they do, because they end up being double targets, and unfortunately women fight being silenced online all the time. That’s what gendered harassment directed at women is made to do, is to silence us. But what we end up running into with LGBTQ people and especially trans people is they’re not just silenced, they’re also discounted. Because they’re considered so other, they’re targeted and they’re not listened to.
It’s especially troubling for me, because I have transgendered family and I wrote this book with them in mind. I’ve been watching my aunt on Twitter for the past week and a half fight this constant stream of attacks. She’s dealt with a lot of online hate and abuse, a lot of people trying to expose her privacy, a lot of people trying to see what they can find out about her and put it online. She works for the Human Rights Commission, so she’s a pretty tough lady, but it’s been intense watching her go through that.
You talk a little bit about your own experiences with online harassment in the book. How has that played into your views on women’s safety online?
Well, like many women, I’ve been stalked and harassed online. When I started working for the San Francisco Chronicle back in 2005, that’s when I got death threats. It was the first time I’d experienced anything like that. Now, I think unfortunately we’re aware that this is something that happens to women when they’re put in high-profile media positions. But it was my first experience with harassment online, and at the time I picked up two very dedicated stalkers who didn’t know each other, but they met in the comments on a post being abusive toward me. They basically teamed up for the next couple of years, and they followed me on the Internet, commented on everything I was writing. They also went out of their way to expose my privacy. They would go to people finder sites and pay to get information there and put it online, such as putting my address on my Wikipedia page.
At the time, this wasn’t happening in a widespread way. I worked with my legal team, and we were trying to figure out what we could do to solve this harassment, because there wasn’t anything like a restraining order for the online world. So we did what we could. We went to file a regular restraining order, which was no problem. But when I went to the judge, to get the restraining order granted, the judge didn’t understand how this could work online. This was 2007. So the judge didn’t grant it, but he left it open so I could refile in the future.
So [from my experience], I learned how my sausage was made, in terms of having my privacy exposed through a variety of different means and running into a lot of systems that just didn’t work and weren’t made to help me. Like online services that didn’t allow me to block people. Like, “Oh, my God, how did you design this without putting in a blocking option?” Things like that, where now we’re like, “Of course, women need this.”
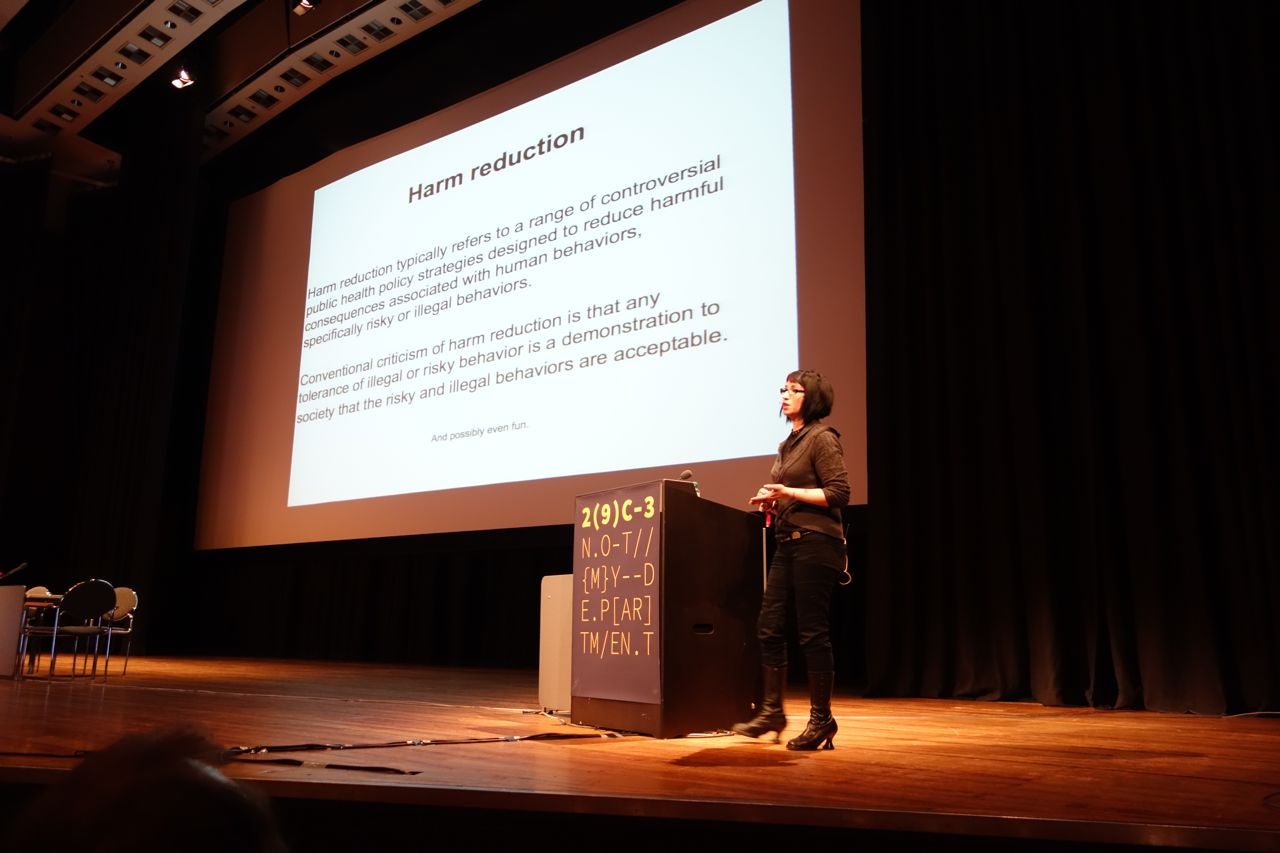
Blue speaking at a 2013 hacker conference in Hamburg, Germany. Violet Blue/Flickr (CC BY NC-ND 2.0)
Reading about your harassment experience, I got the impression—that happened almost seven years ago, and a lot has changed since then in terms of awareness of cyberbullying, but at this point women, to a certain extent, almost expect to encounter that kind of treatment when they go online.
Yes. I agree, and I wanted to address that in my book. You’ll see men be like “I’m being harassed online,” but you rarely see women speak up about being harassed. And that’s because as women, we’ve become trained to be lone soldiers out there, knowing that if we send out a signal, it’s likely to attract more attackers than allies. The mentality of women online has been directly affected by these attacks, and I think as a result we behave much differently online than men do. It’s unfortunate, because I don’t feel like we can be as free as men are.
In terms of female sexual expression online: I feel like girls and women, in the discussion on sexting, are often told, “Never take pictures of yourself naked or express yourself sexually online, ever.” So if the photos are leaked or their accounts are hacked into and they’re posted online, the women are held accountable to a large extent. Can you talk a little bit about your stance on sexting and sexual behavior online, and how it differs from that?
It was very important to me to write this book and include a sex-positive stance. Not only because privacy is so important to us in terms of getting that space to explore who we are and what we like and don’t like in our private time, but also I don’t think that—it’s sort of like a “Just Say No to drugs” approach to people being sexually expressive in different types of media. People are going to do it. If you say, “Don’t take these pictures of yourself and send them”—well, people are going to do it anyway. And I think taking this “Just say no” approach which shames people and says “You shouldn’t have done that anyway,” or “You get what you deserve,” or just “Don’t do it,” it’s going to end up with a lot of victims that are blamed and shamed. It’s going to end up with a lot of people with no recourse for what ends up being reasonable expression. And we won’t end up with any solutions for what actually happens when stuff gets exposed.
So what I did was I took a harm reduction approach in acknowledging that women are going to be sexually expressive in digital media. Women are going to share intimate photos with their lovers, with people they’re attracted to, and I came from the perspective of wanting to share with them the tools they need to make the right decisions, to be able to protect their privacy and protect themselves and the people they care about, and reduce the harm, if anything harmful should come of it. So if something does happen, they know what the consequences are, they know what their recourse is. They can kinda just have more control of it in that respect and know that “If I send a photo, I am in control of this photo, whatever happens.”
Do you think that the situation for revenge porn victims has improved in the last few years or so? I feel like the landscape has changed pretty drastically: Hunter Moore was finally taken down, and all these states are talking about enacting anti-revenge porn legislation. There seems to at least be a lot more awareness as to the potential ramifications for the victims.
I agree with you wholeheartedly. I think if you look at the landscape of revenge porn and the proliferation of sites and the lack of paths to justice that women legally have, it’s easy to look at all of that and see a pretty bleak picture. But this stuff has been going on for a while, and now that we have a large mainstream awareness of it, I think we’re a lot more empowered to have a better understanding of what women face online, and also raising awareness has trickled over into legislation, and lawmakers are actively trying to figure out how to solve these issues in a productive way.
Five or six years ago, it was really a dark place. A lot of women were being exposed, attacked, victimized with revenge porn. Losing their jobs, having their lives destroyed. And there was no conversation about it at all. There were no support systems for them, and now there are. So I see the glass half full at this point.
What steps do we still need to take?
We need more awareness of how systems are abused to the companies themselves. It’s not just that we need to make Facebook aware of this and that, we need to make sure there are advocates for women who are stuck in these systems and have no recourse, because what’s happening in a lot of these cases, especially with the large companies like Facebook, is that women put in a complaint and they’re put into a bucket or a queue where they don’t have a direct line to be able to say, “OK, I put in this complaint that this person put this image online and it’s still sitting there the next day.” So nothing is working in terms of these systems being able to fact-check anything for them.
I think we need a lot more legal help, a lot more legislation. The people in the higher courts want to make the right decisions on freedom speech, and that’s incredibly important. But at the same time, this is going to still continue, so we need to find ways to deal with it, possibly at the domain level, where we can have some sort of filing system or online restraining order system. Something like that would be nice. But if you want to ask what still needs to be done, the list is very long.

Photo via Violet Blue/Flickr (Samantha Wolov) (CC BY – NC – ND 2.0)
You write about privacy and security issues and online dating, but you don’t go into an enormous amount of detail about apps like Tinder, which are incredibly popular and have had their own embarrassing security slipups, like the security flaw that inadvertently exposed your location to users—
—Right, which is really scary, obviously. Yeah, that’s the thing—and we need to have more awareness on this in general. Apps are usually made really fast. They’re often outsourced. And they’re often made with big security flaws. They’re probably one of the weakest areas in terms of security that I can imagine at this point, and there are a lot of really shady people trying to get into the app market. I wrote about this super shady guy who started this thing called Puffchat that he wanted to be a Snapchat competitor and as you know you take these photos and they disappear and people were finding direct URLs to the photos on this guy’s server, just out in the open. And it was under 10,000 users, but it was still enough to make you worry.
So if there’s one thing I’d say about apps in general, you need to be extra extra careful about using apps because they’re made terribly for security. Even some of the biggest, most popular ones, like Snapchat, have big, gigantic security holes, and if they have big security holes that means a hacker will find it. And whether or not that means it’s public or not, you only find out if it becomes public, and that’s kind of scary. So if you’re setting up an online profile, you should always use a different email address. Never use your full name, and just basically do anything you can to mask any information that can be used to track you down. You should do a reverse Google image search on any photo that’s associated with your information, because one of the first things a hacker is going do to find out more about you is look that image up to see what kind of information they can find out about you.
So [using these apps] comes with an inherent risk. Some of the companies you can trust a bit more in terms of having security locked down, but are you trusting the company with your information, or are you trusting the company against hackers with your information? Because while I think I can trust Facebook against hackers with my information, I don’t think I can trust Facebook with my information. It’s a complicated landscape, and again it’s a matter of knowing what all the risks are with the different things you use and making the right choice in terms of what you’re OK with printing.
What about Heartbleed? What have your thoughts been like for the past few days?
Oh, God. I’ve been resisting writing about the Heartbleed thing, because it’s just such a grand catastrophe and a meltdown of epic proportions. It’s been such a trainwreck to watch. I think we’re going to see a lot of questions raised over the next few days, questions about practices for different companies that need to be answered. I think one of the most interesting things I’ve heard about is the one about the IRS, where the IRS wasn’t affected about it. I think that’s a really interesting question: Like, what hasn’t the IRS updated in a long time in terms of security? I think there are a lot of questions that still need to be answered about the way this bug was revealed. It had a snappy name, a snappy website, a great logo. This was not about this one time. I’m really wondering what the processes behind that were in terms of due diligence of all the people affected, because it’s a lot of people. We could also use a lot more answers about how consumers are directly affected by this. I foresee more drama, fingers pointed, for sure (laughs). It’s a big storm.
What’s so striking to me about it is I haven’t gotten a single email from anybody about this, from any companies that have been affected. I’ve pretty much had to do my research on which passwords I have to change and when, all on my own.
Exactly. I haven’t gotten an email from anybody. Granted, I’ve seen it on Digg, and I’m glad it’s on some mainstream-ish sites explained in some consumer-friendly language. But I got one email about it today, finally, and that was from my ISP, and that’s only because I have a really progressive privacy-protecting ISP. That’s the only notification I’ve gotten. And I use all the big services like everybody else. It’s kind of appalling, actually.
The way I would see it affecting people who are targeted online… you have a time period, right, where people know there’s this vulnerability and they can get access to all this information. There are people around the world waiting to hear about this and they’ll go after everything they can, they’ll scrape up everything they can, and put it together and resell it on the black market in different packages. So if there’s any fallout for this, that’s what I can see happening: If something got scraped up in a big cache by somebody and sold. But other than that, I don’t necessarily see how it will affect anybody directly, unless there’s a high-profile hack that happens, where a mass of passwords gets sold somewhere.
So what are, like, the two or three most important things women need to do to protect themselves?
There are some basics. Doing a privacy self-checkup and going through the privacy settings in all your major accounts, and making sure you do a little cleanup of your password, doing a couple Google searches on yourself and seeing what comes up. It doesn’t sound very sexy, but it’s one of the most important things I tell people to do. To add to that, I would say getting yourself off people finder and search websites. They put forward freely available a lot of information about you that can be bought as a package. Going to a company like [online privacy company] Abine, you can pay them to go through and have that information removed, which I think is a really, really good idea. So if God forbid a stalker comes after you, they’ll be a little less information about you. Then there’s just general best practices. Making the Internet wear a condom, as I say.
From the perspective of a journalist, though, I feel like these people finder and search websites are an incredibly valuable tool for me, in terms of finding information and tracking down sources. As someone who’s both a privacy advocates and a journalist, do you ever feel like you have to negotiate the tension between the two? Because in a lot of ways, as a journalist, you need to compromise people’s privacy or access information that they wouldn’t necessarily want you to access, in order to write your story.
I’m really glad you asked that question, because it’s a really good one. One thing to keep in mind when we talk about this is in the past, if you wanted to find information about people, we would have to go down to the place where the records were kept and do the work ourselves and search for actual files. The laws around freedom of information were created with that structure in mind, and that structure is completely changed. Now anybody can do that. What’s happened is the laws were created with the idea in mind that there was a significant barrier to access, and that would restrict people’s use to more legitimate use, rather than use by stalkers or vengeful exes. The landscape has changed, and now it’s accessible to everybody. I don’t necessarily think that’s a good thing.
In terms of my own journalism, in terms of how I do my work, I don’t compromise the privacy of my subjects. I’m very careful to do that, but that probably sets me apart from many of other journalists. I work to protect my sources and subjects. I’m not going to be the journalist to put someone’s name online, unless it is key to the telling of the story. A lot of other outlets will go out of their way to put a porn actress’s real name down, for instance, even if it’s against her wishes. It’s just happened too many times, and I go “You know what? I’m going to keep my practices and keep what’s relevant to my story.”
In your book, you write about how many of the privacy breaches haven’t been due to malicious hackers, or greedy companies taking advantage of your personal information: It has to do with a lack of consensus over what constitutes a private and public space online. It sort of reminded of the Buzzfeed controversy over that Twitter conversation, where rape victims talked about what they were wearing during their assault, and a Buzzfeed reporter wrote about it using her sources’ Twitter handles, and it raised similar questions over the division between private and public space online.
I think there’s sort of a ripple effect of people realizing just how public the Internet is that is still happening. And I think seeing #WhatIWoreWhenIWasRaped revealed that people don’t quite understand just how public things are on the Internet. On one hand, it’s “OK, I trust you to respect my privacy in sharing this with you,” but in doing so in a public space, where literally anyone can see it. That’s sort of the harm reduction warning that I’d like to impart as well: Know the risks, and know that when you put it out there, it’s out there. Eventually it will go away. You can make a lot of noise to make things go down in search and eventually they’ll fade away, but sitting at home on your computer on Twitter isn’t actually a private space.
Would you personally have run that story with their names?
I don’t think I would have. That’s not an area I report on in general, but if I were reporting that, I probably would have focused on the questions it raised about privacy and the assumptions these women were making about Twitter being a private space. But I wouldn’t have gone out of my way to draw attention to the victims. It’s the lone soldier mentality—I know drawing attention to these women online will draw attention to hackers. I don’t know who’s served by that, or if the story is served in any way from that.
The thing is, someone’s always going to do the bad practices. Someone’s always going to do it in media, always going to do it in the social space. Someone’s always going to come along being malicious and find that weak spot, find that exploit, and troll you and try to make your life hard. That’s a little bit of what I put in the book: I want people to start thinking like hackers, to start thinking like stalkers. Thinking as the attacker, and you’re attacking yourself. “How can I best exploit myself?” Because if you do that, you’ll be able to think things through a little better in terms of: “OK, is this going to be defensible? Is this something I’m going to be able to live with if someone does something bad with it?” You gotta think like a hacker. That’s how you can protect yourself online.
Photo via Violet Blue/Flickr (CC BY NC-ND 2.0)
