After a slew of break ins to social media accounts belonging to celebrities and tech executives, hacking collective OurMine managed on Tuesday to hijack news site TechCrunch.
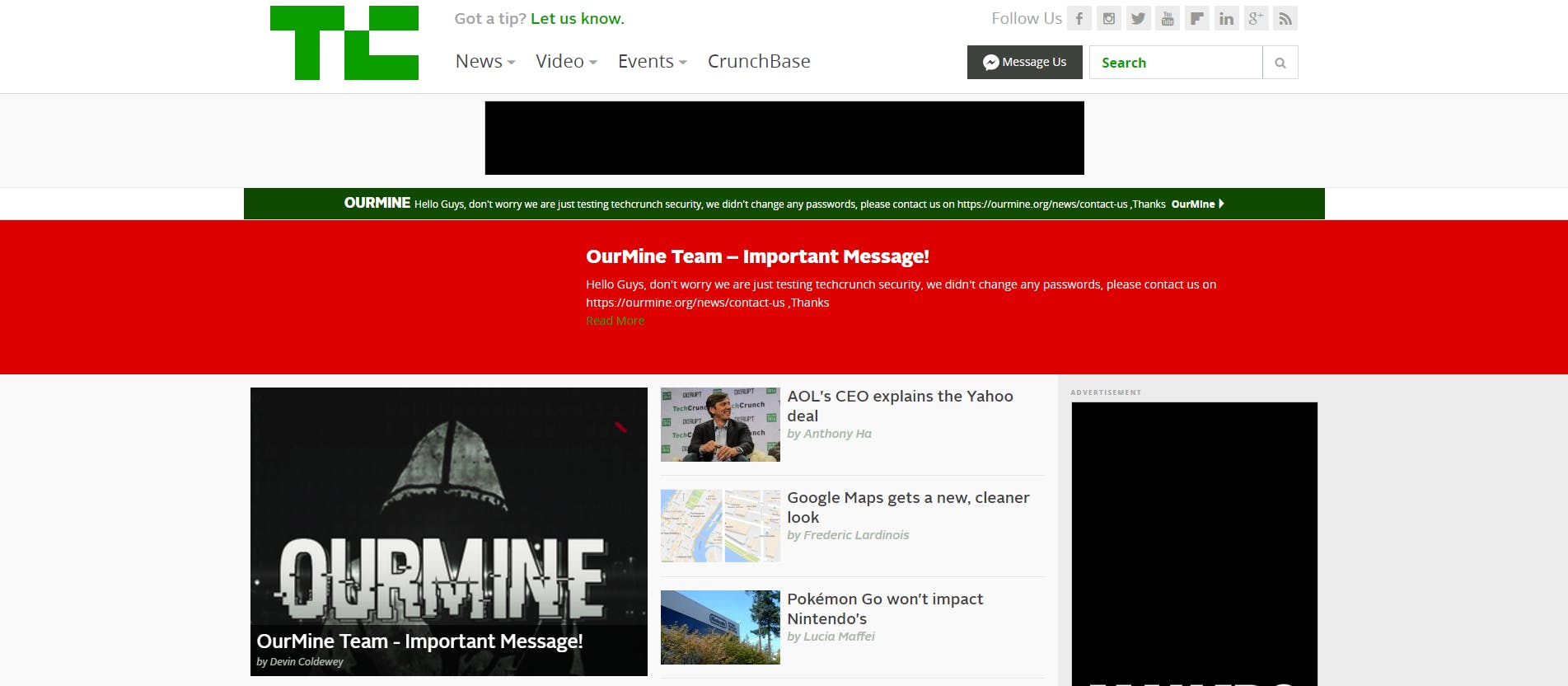
The temporary invasion into TechCrunch’s content management system (CMS) took place early Tuesday morning, and allowed OurMine to publish a post with the headline “OurMine Team — Important Message!” that appeared on the front page of the site and disrupting the publication’s operations.
The post itself is no longer available, but a cached version of the page is still available. The body of the article created by OurMine read: “Hello guys it’s OurMine Team, we are just testing TechCrunch Security , don’t worry we never change your passwords.”
OurMine was also able to share the post via TechCrunch’s Twitter account and managed to hijack the banner atop the TechCrunch home page, where they placed a message similar to the post.
As is standard operating for OurMine, the group requested TechCrunch contact them to retrieve the compromised account and shared a link to their contact page.
A member of OurMine told the Daily Dot they were able to compromise the account of TechCrunch writer Devin Coldewey by using a “brute force tool” the team created, though they declined to provide any additional details about the tool.
OurMine considered the break-in a simple test of TechCrunch’s security methods. According to an OurMine member, the group told TechCrunch to enable two-factor authentication on all of the site’s accounts to prevent any additional breaches.
Others have suggested a different means of entry; namely, the group found a password belonging to Coldewey and managed to log in as the writer through through TechCrunch’s CMS.
OurMine rejected that notion when asked, but it has been called into question in the past if the group has truly “hacked” their way into accounts or if they have used login credentials found in databases from other sites that have spilled online in recent months.
While Business Insider reported OurMine has been around since 2014, the group grew to prominence this year after taking over several high-profile social media accounts beloning to celebrities and executives at tech companies.
The group has claimed responsibly for taking over the dormant Twitter account of Facebook founder and CEO Mark Zuckerberg, as well as Amazon CTO Werner Vogels, Spotify CEO Daniel Ek, Uber CEO Travis Kalanick, actor William Shatner, and many others.
That increase in awareness came shortly after a number of databases appeared online containing millions of account credentials belonging to users of popular social networking services like LinkedIn, MySpace, and Tumblr.
Many of those usernames and passwords have been hosted online by a service called LeakedSource. Functioning primarily as a way to allow people to search to see if their account was compromised in any of the stolen databases, LeakedSource also offers a paid service that gives nearly unlimited access to the usernames and passwords housed in the leaks.
For a small fee, users are able to search any email address or account name and see the passwords associated with the login. LeakedSource told the Daily Dot it has since updated its protections to only show part of the password, but will reveal the password in full if a person enters it correctly.
A Twitter user named Lid admitted to using LeakedSource to take over the Twitter account of Oculus CEO Brendan Iribe earlier this month, he told the Daily Dot that he was once associated with the OurMine collective and claimed the group simply took passwords from LeakedSource.
Since many people reuse passwords don’t change their passwords regularly, Lid claimed OurMine is able to find other accounts belonging to a user that have the same password.
The claim from Lid may explain why OurMine’s hacks often aren’t direct access to an person’s social media presence but rather through an ancillery account that is linked to a person’s Twitter. Such was the case for Google CEO Sundar Pichai, who had his Quora account taken over. Because it was linked to his Twitter account, posts made on on his Quora account appeared in his Twitter feed.
OurMine denied any association with Lid and claimed to have never used LeakedSource—a claim they maintain in regards to the TechCrunch situation. It is worth noting that an email address associated with Coldewey is present in one of the online databases that houses login and password information.
TechCrunch has not commented publicly on the incident. The Daily Dot contacted Coldewey for comment but didn’t receive a response at the time of publication.
H/T Engadget