Moscow-based security company Kaspersky Lab says its discovered spy software, which it traced back to the NSA, on computers in more than 30 countries.
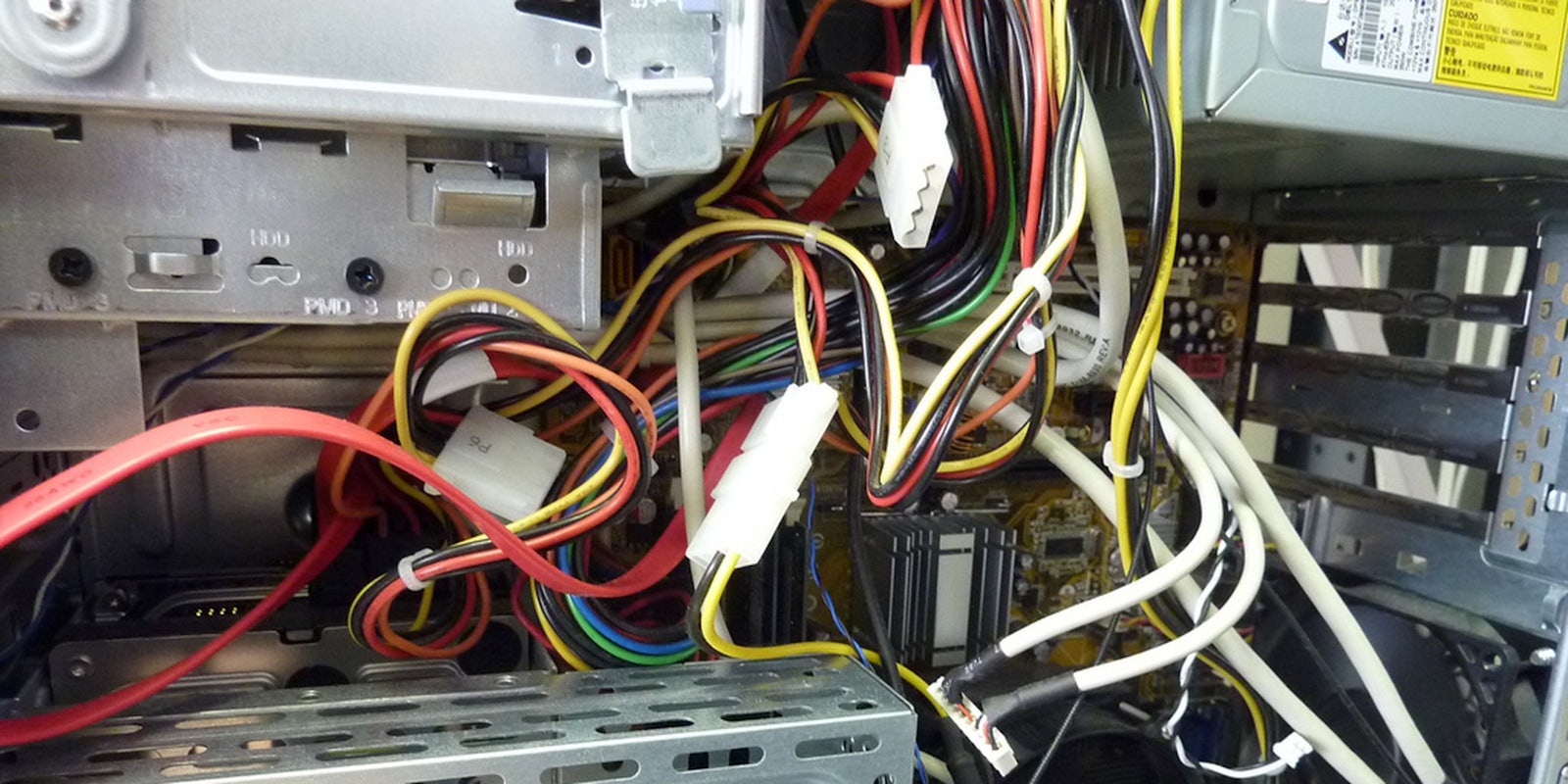
The software was concealed on the hard drives made by Western Digital, Seagate, Toshiba and other top manufacturers, Kaspersky reported, raising new concerns internationally about the seemingly boundless nature of American cyber-espionage.
Unsurprisingly, Kaspersky found infected computers in Iran, Russia, China, Pakistan, and other Middle East and North African countries. The targets include government and military agencies, banks, energy and nanotech companies, phone companies, media institutions, and Islamic activists and scholars.
Kaspersky declined to identify the NSA by name, but noted, however, that it was closely linked to Stuxnet, an NSA “cyberweapon” directed at Iran, reportedly with Israel’s aid. A former NSA official confirmed Kaspersky’s analysis to Reuters on Tuesday.
Officially, Kaspersky refers to the threat only as the “Equation group,” so named for their “love for encryption algorithms and obfuscation strategies.” The group has allegedly been engaged in sophisticated network exploitation as far back as 2001, and perhaps as early as 1996.
“The Equation group is probably one of the most sophisticated cyber attack groups in the world; and they are the most advanced threat actor we have seen,” the report said. “It is quite possible that the Equation group malware was used to deliver the Stuxnet payload,” it added.
One concern is that the spying programs could not have been written without access to the hard drives’ proprietary source code, information that’s not available to the public. That indicates that either the authors gained access to the code illegally, or alternatively through a clandestine partnership with the affected manufacturers.
The NSA has been accused of partnering with companies in the past and tampering with consumer products to make them less secure. For example, RSA, a U.S. network security provider, was accused in 2013 of accepting millions of dollars to weaken its encryption standards.
Both Western Digital and Seagate have denied any knowledge of foreign code in their hardware. Former U.S. intelligence operatives told Reuters that to obtain the company’s source code, the NSA might pose as a software developer and acquire it directly. Additionally, the code could have been acquired during a security audit, if the companies sold products to the Pentagon or other sensitive agencies.
H/T Reuters | Photo by Van Jacobs/Flickr (CC BY 2.0)