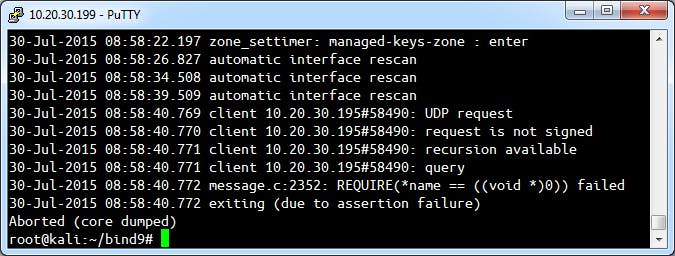
A new vulnerability in one of the Internet’s most important pieces of software made it easy for any hacker to crash thousands of servers by simply sending an easy-to-create packet at the target.
New research from Robert Graham, the CEO of Errata Security, showed the glaring weakness in BIND9, the most popular tool for translating numerical IP addresses into easy-to-read domain addresses.
Within an hour, Graham says he could have crashed a huge portion of the Internet.
The vulnerability was very recently fixed but highlights a pattern of problems with the popular software, according to Graham.
“BIND9 has lots of problems,” he wrote, “problems that critical infrastructure software should not have.”
The technology powering BIND is decades old and ubiquitous but, Graham argues, bloated and in many ways outdated.
He continues:
The point I’m trying to make here is that BIND9 should not be exposed to the public. It has code problems that should be unacceptable in this day and age of cybersecurity. Even if it were written perfectly, it has far too many features to be trustworthy. Its feature-richness makes it a great hidden master, it’s just all those feature get in the way of it being a simple authoritative slave server, or a simple resolver. They shouldn’t rewrite it from scratch, but if they did, they should choose a safe language and not use C/C++.
The exploit was not found in the wild before it was fixed but still sends a strong message about a fragile single point of failure in one of the most prevalent pieces of software online today.
H/T Ars Technica | Illustration by Max Fleishman