A pro-Palestinian hacker crew has attacked the websites of two companies whose business is helping defend companies against hackers, and they did it using a piece of obsolete 1980s technology: a fax machine.
In turn, a pro-U.S. hacker has doxed the Palestinian group’s members, revealing their names and personal details.
The KDMS Team, who last week hacked the security firm Rapid7 and who in the past successfully hit major antivirus companies Avira and and AVG, on Saturday successfully cracked and defaced the security firms ESET and Bitdefender.
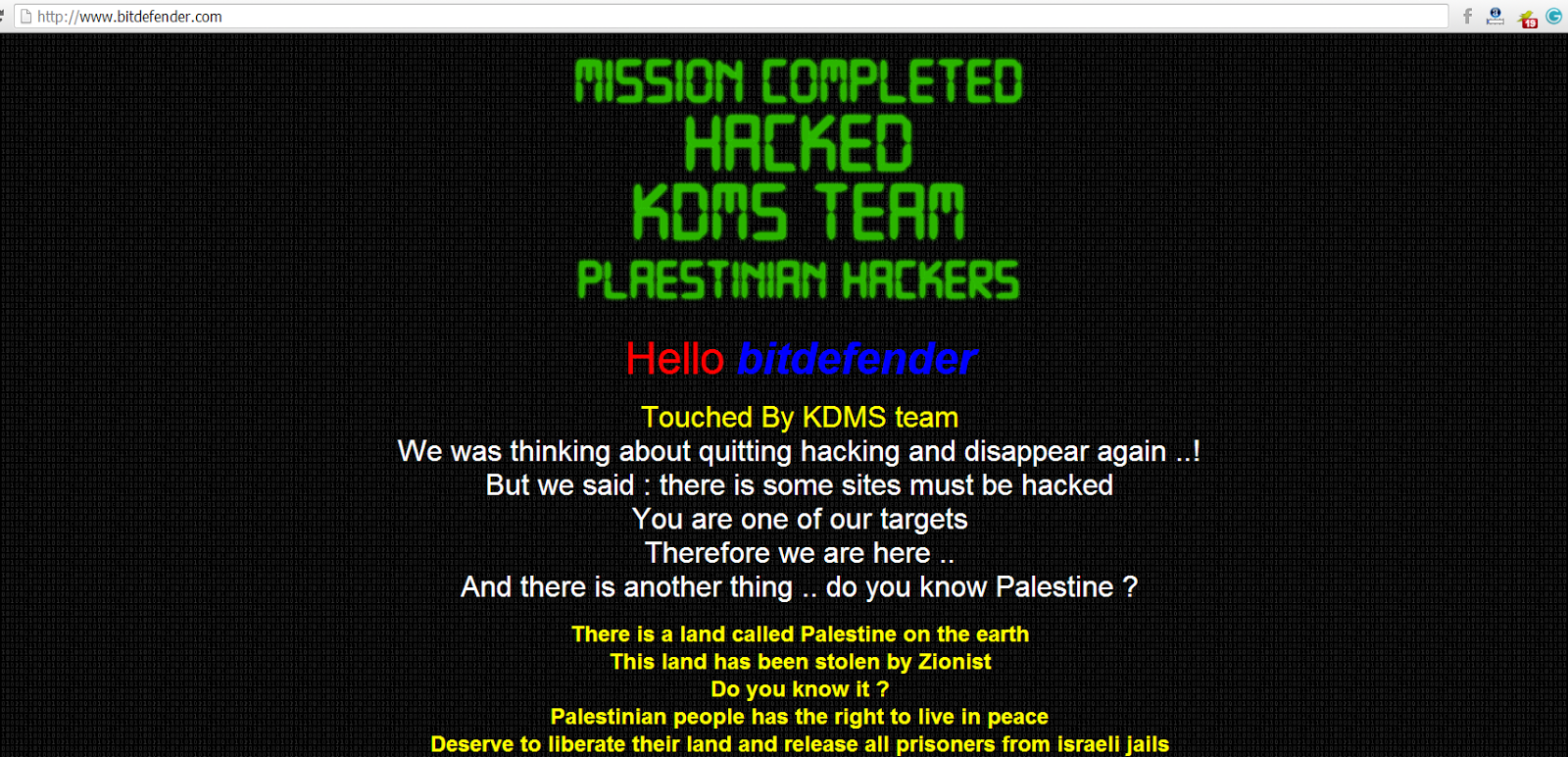
The crew broke past the security of the two firms and changed their DNS records to redirect visitors to a site that played the Palestinian national anthem under a message reading “You Got Pwned.”
Both ESET and Bitdefender, as well as Rapid7, were hacked via the domain naming service Register.com. The strangest detail, and one which shows how the human element is almost always the weak link in security environments, is that they hacked the sites without using a computer at all.
The sites, according to The Hacker News, were hijacked with a “spoofed change request faxed to Register.com.”
What could possibly be next? Spear-phishing via candlestick phone to BR549? Brute force attack by telegraph?
Alin Vlad, Global Social Media Coordinator at Bitdefender, said that Register.com had fixed the problem and that none of their customers were unprotected at any point.
In another development, the American hacker and self-described patriot known as The Jester claimed he had identified the four main members of KDMS.
After analyzing email addresses and Facebook accounts, he announced on Pastebin his belief that the group consists of Firas Abu Azab, Omar Ashraf, and Wassem Ashraf, as well as possibly Mohanad Abudalfa. He believes the owners of the Twitter accounts @white_2_2 and @mohnadk are also part of the group, with @white_2_2 playing a major role.
The fulcrum for The Jester’s investigation is the relationship between the official KDMS Twitter account and the 16 accounts it was following.
“Because of KDMS Team’s relatively new presence on Twitter,” he wrote, “it is highly suspicious that it knows about, and follows, accounts that have not been active or tweeted for 6 months to over 3 years.”
The main Twitter account was no more than a day old on Oct. 8. By the next day, it had unfollowed half of the accounts it was following the day before. By the Oct. 11, it was following no one.
The Jester felt the likelihood of those initial follows being group affiliates was high, there being no other reason to follow handles belonging to such irregularly updated accounts, and reasoned from there.
The Palestinian group has yet to confirm or deny The Jester’s allegations.
H/T The Hacker News | Photo via KDMSteam/Twitter
