If you’ve been on Tinder in the past week or so, perhaps you’ve been matched with an attractive young woman named “Haley.” If you reached out to Haley, you might’ve had a conversation similar to the following exchange:
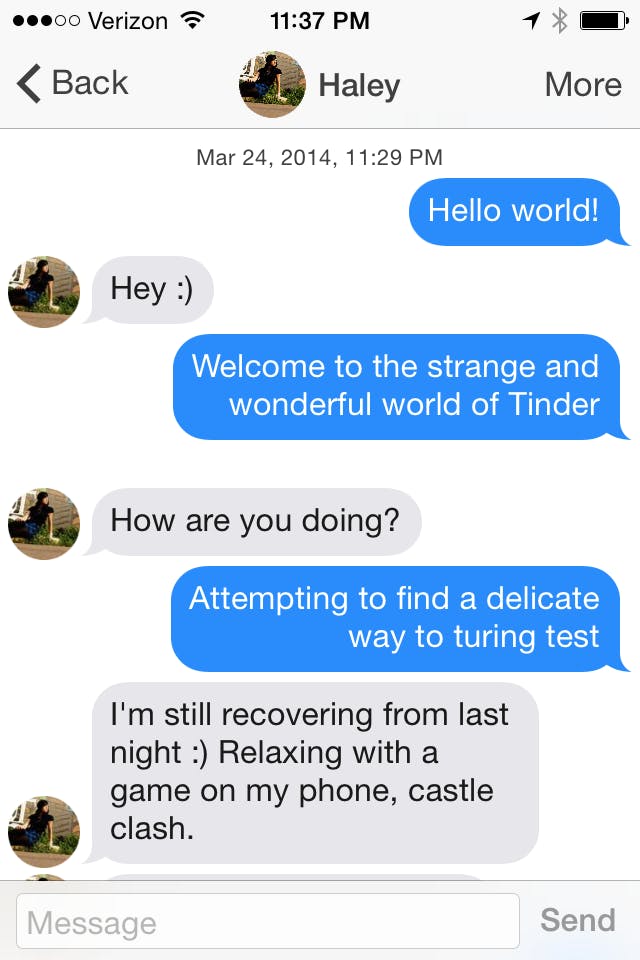
At first glance, Haley seems like a pleasant enough human with a fondness for the mobile game Castle Clash and a mild drinking problem. But Haley is not a human. She’s an automated bot promoting Castle Clash on Tinder.
According to TechCrunch, Tinder has been overrun by these Castle Clash bots. Under the guise of Tinder users, they’re messaging other users and sharing a link to the game under the URL Tinderverified.com, making it seem as if Castle Clash is being endorsed by the app itself (it is not).
Since a Reddit user noticed the hack a little more than a week ago and posted the above exchange with Haley in r/Tinder, dozens of other Tinder users say they’ve been contacted by similar bots, who will typically message them with a “hi” or “how you doing :)” before mentioning Castle Clash and sending the URL.
wow i finally got a match on tinder had part of a conversation with them and turns out it was a bot to get me to download “castle clash”
— jay (@readreceiptpapi) April 1, 2014
Are you serious? A tinder bot trying to get me to download gay ass castle clash. What has this world came too? pic.twitter.com/a9n1NiYD4e
— micah (@mhazelip1) April 1, 2014
lol, thought I try going on tinder again and found a bot shilling for a game. A GAME. ON A DATING SITE.
— Robert (@23Breach) March 30, 2014
It’s unclear whether Castle Clash’s developer, IGG.com, is behind the hack, or if it’s the work of an ambiguous third party trying to promote the game. But needless to say, it doesn’t really reflect well on Castle Clash to be resorting to such tactics to boost its downloads. And it definitely doesn’t reflect well on Tinder, especially because the Castle Clash URL makes it seem as if the bot is associated with the Tinder brand.
In a statement to TechCrunch, Tinder said it was aware of the Castle Clash bots, and it’s taking the steps to delete the spam accounts, referring to the hack as an “isolated incident” (it isn’t, really: Tinder has been overrun by bots in the past). Either way, needless to say this doesn’t exactly inspire a rush of confidence in the app’s ability to safeguard its users from spammers and sleazy marketers. But it does make me want to download Castle Clash, kinda!
H/T TechCrunch | Photo by NeitherFanboy/Flickr (CC BY 2.0)
