Microsoft worked to provide the FBI with court-ordered user data after the company began using encryption for customers who used Outlook, according to newly-released documents first leaked by Edward Snowden.
Snowden, of course, is the former National Security Agency contractor who obtained a huge cache of agency documents and passed them to a handful of journalists, including Glenn Greenwald, in 2013. Among the earliest programs his documents revealed was PRISM, which allows the NSA to get emails, chats, and other files from targets who use any of nine different American tech companies, like Yahoo, Google, and Facebook.
Some of PRISM’s specifics are still sketchy, but U.S. officials have admitted it’s authorized by section 702 of the FISA Amendment Act. While most PRISM companies have explicitly and specifically denied working with the NSA to knowingly give the agency customers’ information, these documents contribute to the knowledge that the FBI played intermediary between the tecnology giant and the NSA.
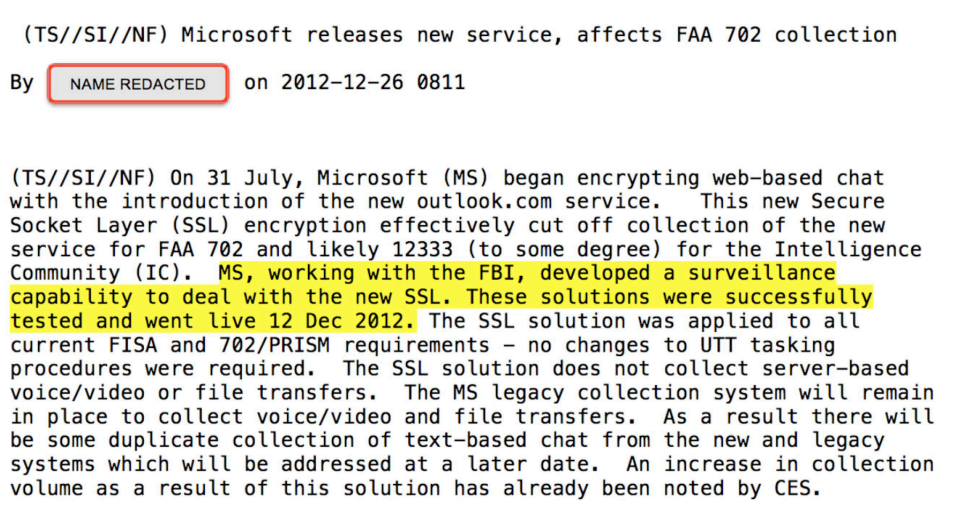
Referencing Microsoft’s implementation of Secure Socket Layer (SSL) encryption for its customers who use Outlook, one newly-revealed slide—released as part of Glenn Greenwald’s recent document dump that coincides with his new book tour—says:
MS working with the FBI, developed a surveillance capability to deal with the new SSL. These solutions were successfully tested and went live 12 Dec 2012. The SSL solution was applied to all current FISA and 702/PRISM requirements.
A spokesperson for Microsoft declined to go on the record, but strongly rejected the implication in that document that the company had given encryption keys to the government.
In an earlier blog post responding to the PRISM program, Microsoft General Counsel Brad Smith wrote that when the company began using encryption as the default for Outlook users, it kept those encryption keys a secret, but still obeyed court orders for user information:
To be clear, we do not provide any government with the ability to break the encryption, nor do we provide the government with the encryption keys. When we are legally obligated to comply with demands, we pull the specified content from our servers where it sits in an unencrypted state, and then we provide it to the government agency.
When news of PRISM broke, most of those nine companies denied knowingly worked with the NSA on the PRISM companies. Microsoft’s specific statement was:
[W]e provide customer data only when we receive a legally binding order or subpoena to do so, and never on a voluntary basis. In addition we only ever comply with orders for requests about specific accounts or identifiers. If the government has a broader voluntary national security program to gather customer data we don’t participate in it.
Another PRISM slide makes it explicit that PRISM doesn’t have for a direct relationship with Internet companies, and that such a relationship is available “only through FBI.”
Clarification: This story has been updated with additional contextual information from Microsoft, as well as new language to make clear that Microsoft denies any attempts to hand over user data to the FBI without legal obligation.
H/T Matthew Keys | Image by Jason Reed