Mac-based spyware was discovered last week on a computer belonging to a Ugandan activist attending the Oslo Freedom Forum, an anti-authoritarian open society conference.
The spyware, discovered by respected hacker Jacob Appelbaum, who has been affiliated with Wikileaks and the Tor Project, was described by security firm F-Secure as “a new and previously unknown backdoor.”
In a subsequent post, F-Secure announced the discovery by the security company Norman that the spyware seeding “is apparently connected to larger espionage effort — and those efforts look to be connected to India.”
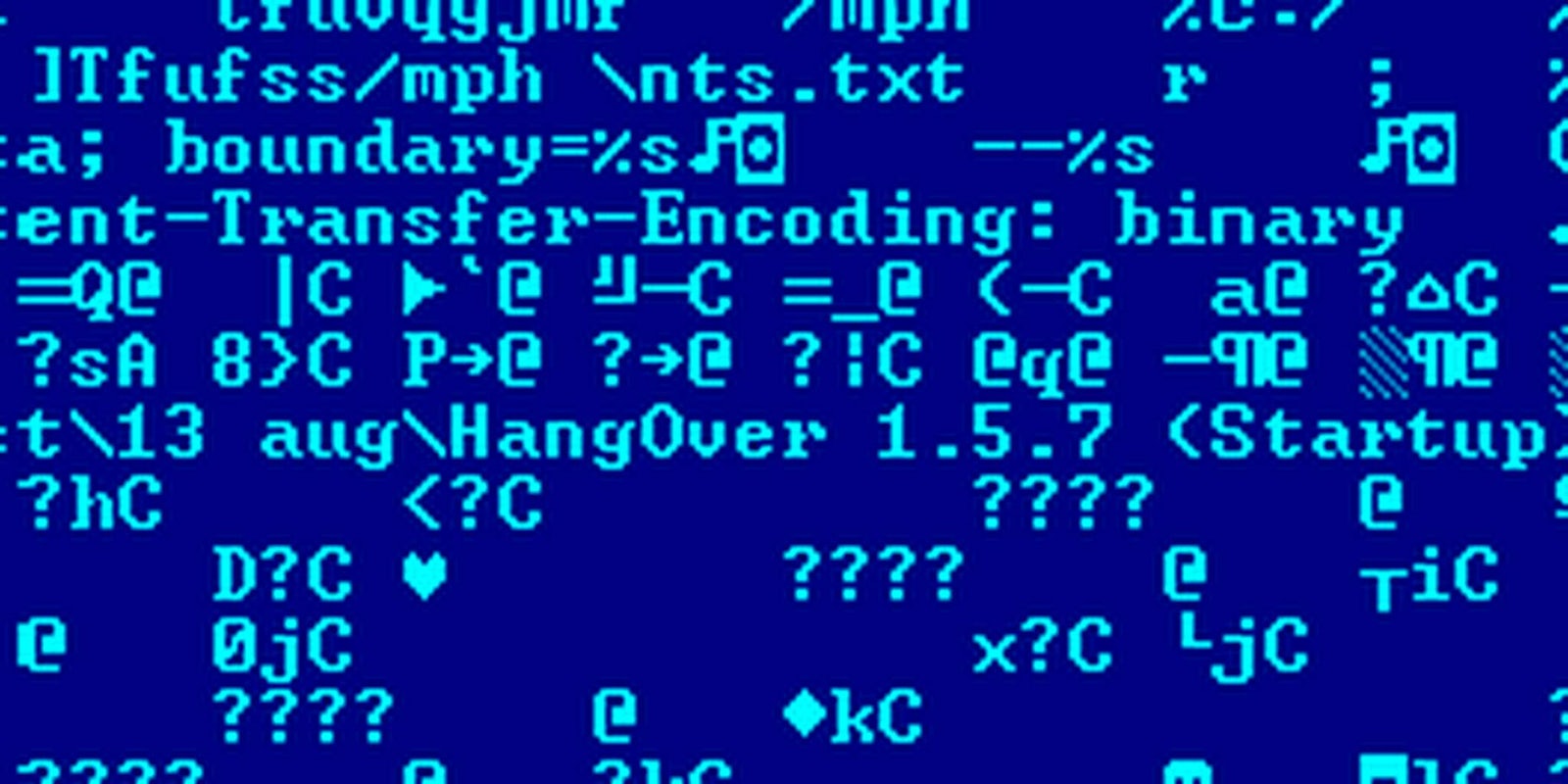
Norman issued a report last Friday that outlined the activities of an Indian-based hacking group operational for at least two years and known as “the Hangover Group.”
In a blog post about the report, Norman’s Snorre Fagerland, principal security researcher in the company’s malware detection team, noted that “the same attack group has apparently turned to another business area: Providing surveillance services to those who would like to spy on activists.”
The group’s focus was originally primarily on targets of interest to the Indian government, many Pakistani. But the group branched out to hit industrial targets as well, including targets in the finance, mining and engineering sectors. Target countries, in addition to Pakistan, include Norway, the U.S, Iran, China, Taiwan, Thailand, Jordan, Indonesia, the U.K., Germany, Austria, Poland and Romania.
“Based on the sample and Command & Control domain mentioned in the F-Secure post, we can say quite conclusively that the Oslo Freedom Forum attack was performed through the same attack infrastructure. We also found another MachO executable apparently written by the same person (same Apple Developer ID).”
In the same way that militias have assumed a role in prosecuting the will of a country’s leadership on the street, these cyber militias serve a similar role online. It seems likely this officially unofficial hacking will continue to be an issue in both international relations and private enterprise, both of which are functions of an increasingly shrinking and entangled global world.
H/T F-Secure | Photo by Norman