A phishing scam disguised as an item on your pinboard has landed on Pinterest, and could be thieving the usernames and passwords of unsuspecting pinners.
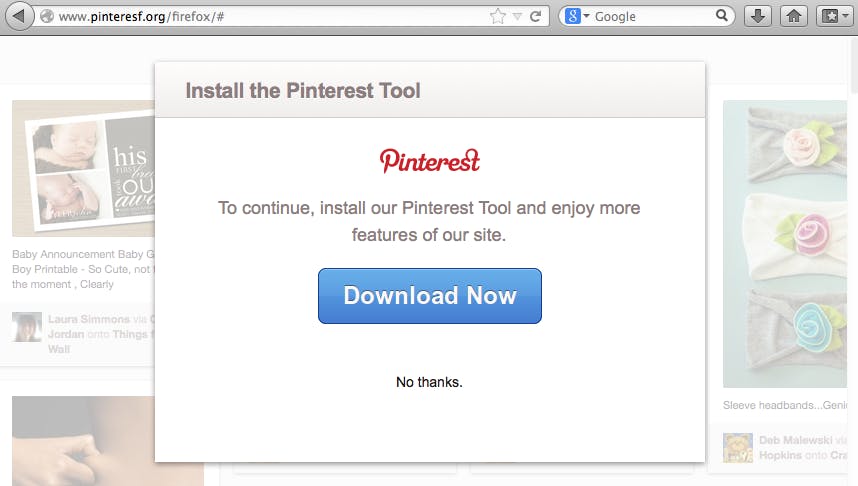
The scheme comes in the form of a pin, which, when clicked, redirects the user to a third-party site that asks you to download a “Pinterest tool.” Instead, the user downloads a browser plugin that reads the user’s password info for various websites.
Janne Ahlberg, an Internet security expert who frequently tests websites on his blog, analyzed the code for the “Pinterest Tool” and found it to be malware—specifically, an iteration of a known Trojan virus. According to Ahlberg and the F-Secure website, an Internet security testing site, the Trojan is designed to intercept “possible user name and password from visited websites and [send] them to the attacker’s server.”
Once you’ve inadvertently installed the malware, it masquerades as a regular browser extension:
But thankfully, the trick to removing it is easy: just go to your browser tools or extensions, locate the “Pinterest Tool,” and uninstall it.
The file name for the malware is Trojan.PWS.ZAQ., but Ahlberg believes there are other similar bugs around the site. One alternate version of the bug that was discovered over a year ago orders you to “install the Pinterest Tool to view this recipe. To continue, install the tool and enjoy more features of our site.”
Ahlberg recently unearthed a massive diet spam campaign spread over Twitter and Pinterest and involving hundreds of hacked websites. He advises that Pinterest users proceed with caution when accessing Pinterest, and shows them how to safely search Pinterest to see if a particular domain is infected.
Yesterday Ahlberg noted that the suspicious pins are still on the Pinterest website. But users looking to identify the culprit pins based on their addresses, however, might be thwarted: it appears the malware contains a bit of code that attaches itself to whatever normal pin a user might want to put on their site, causing it to redirect to an infected site housing the fake “tool.”
As Jason Hamilton at 404 Tech Support elaborates, the only way a casual user could tell something is off is by double-checking the URL:
In the case of these malware pins, the links went to a variety of blogspot blogs with a food blog sounding subdomain like icanhasrecipe.blogspot.com…. The url looks like icanhasrecipe.blogspot.com/?r=13498asd987149087&u=http://tasteofhome.com. Nothing [so] conspicuous that a casual user would notice something wrong.
Alhberg has identified over 20 such sites.
He expressed surprise that Pinterest has apparently done nothing to halt the spread of the virus. But even more surprising is that the version of the malicious plug-in discovered in 2012 is still there along with the newer version.
Wary web surfers might want to disable JavaScript in their browsers when they visit Pinterest, and make sure their anti-virus security protection is up to date.
Photo via Wikimedia Commons
